On-Premise & Cloud Network Penetration Testing
Protect Yourself From The Risk Of Cyber Attacks & Data Breaches, And Avoid 5-7 Figure Fines & Lawsuits With Singapore's Most Affordable & Reliable Network Pen Testing Services
Why Work With Privacy Ninja?


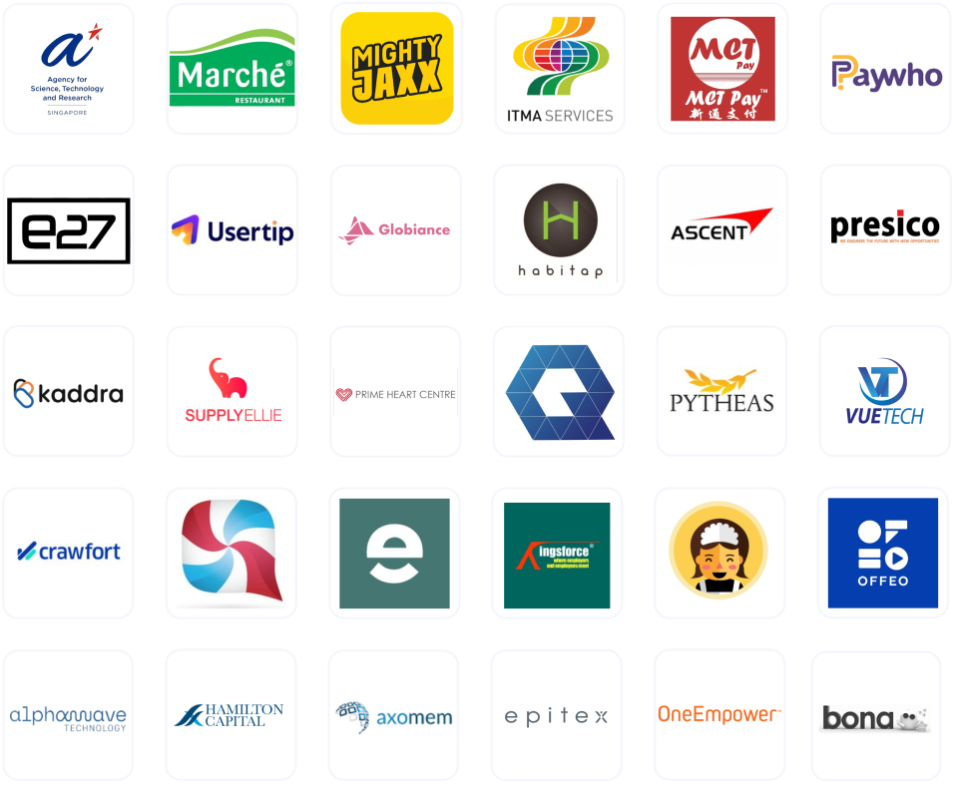
Look at our track record
We founded Asia’s first bug bounty platform and have been keeping Organisations, MNCs and SMEs all over the world safe from cyber-attacks and data breaches.
Large organisations like A*Star Research, Marché, E27, MightyJaxx, AlphaWave, Wallex, and The Law Society of Singapore trust us with their cyber security.
Not one of the companies we’re working with has suffered a data breach after engaging us.

Our team is made up of the best penetration testers in the world
Our pentesters are hall of famers who have ethically hacked the most secure systems in the world, like Microsoft, Google, Facebook, etc.
As there’s nothing our pentesters haven’t seen, we complete our VAPT within 7 days of project commencement!

Despite being the best in Singapore, we’re the most affordable
We pride ourselves on being the best pen-testing provider in Singapore but are also 100% committed to being the most affordable.
If you find other licensed and registered penetration testing service provider who are cheaper than us, we’ll match the price.
Our Double Guarantee

Price Match Guarantee
Annual VAPT is mandatory for all networks, mobile, and web apps that store personal data in databases. We believe businesses shouldn't have to pay extra to stay compliant and avoid penalties. If you find a lower price with another licensed VAPT service provider, for the same scope of work or more, we'll match their price. Terms & Conditions apply.

Our Security Guarantee: Unlimited Revalidations Until You’re Fully Secure
We’re not just affordable — we’re trusted. None of our clients who used our VAPT services have ever been hacked, and we’re committed to keeping it that way. That’s why we offer a 1-Year Unlimited Revalidation Guarantee: unlimited revalidations for a full year after the initial test, at no extra cost. While others charge for revalidations , we don’t stop until your systems are completely secure. Because if we can’t help you stay protected, we don’t deserve your trust. Terms & Conditions apply.
As Featured In

Lian He Zao Bao
Bank Phishing

Channel 8
Dark Web

Interpol World
Cybersecurity

Channel 8
IoT Security
Complete Your Network Pentest With Privacy Ninja in 7 Days
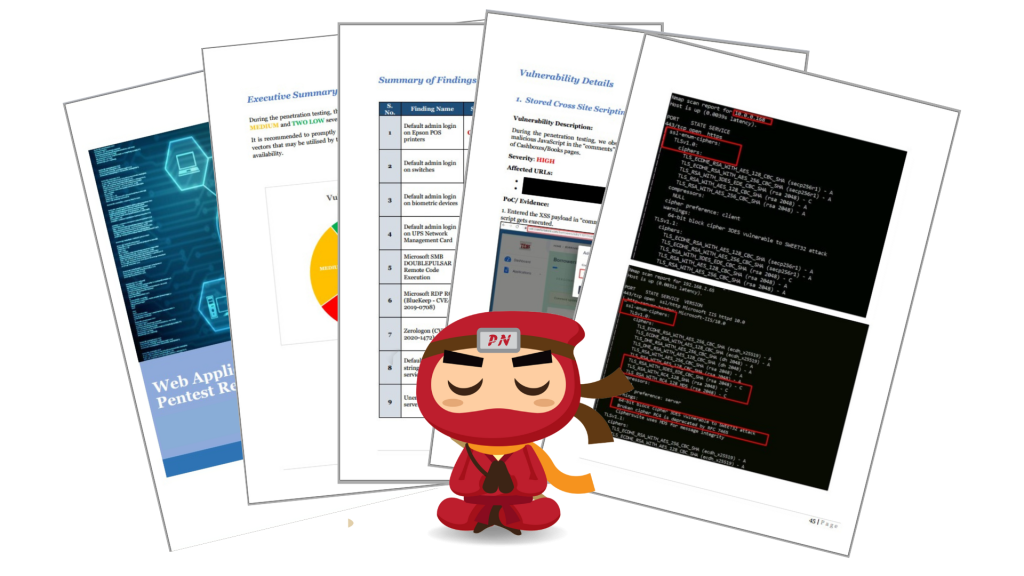
Affordability is one thing. A solid report is everything.
After the VAPT exercise, you will gain access to all findings in a detailed report that includes:
Overall findings summary
Itemised replicable steps/POC (Proof-of-concept)
Explanations
Common Vulnerability Scoring System (CVSS) risk rating
Vulnerability impact
Practical recommendations for remediation
Our Pentesting Certifications

Certified Ethical Hacker (CEH)

Offensive Security Certified Professional (OSCP)

Offensive Security Certified Professional (OSCP) Plus

CREST Certified Company

CREST Registered Penetration Tester (CRT)

CREST Certified Web Applications Tester (CCT App)

CREST Practitioner Security Analyst (CPSA)
CSRO License (Entity): Privacy Ninja Penetration Testing Service License No. CS/PTS/C-2022-0128R

Industries We Serve
How We've Helped Our Clients Identify Vulnerabilities
Web: Specialised Recruitment Agency
What we found:
CRITICAL:
SQL Injection – An attacker can gain access and dump the whole database containing critical data using malicious SQL commands in user input fields
Local File Inclusion (LFI) – A present on the server, the attacker can read sensitive files without any restriction. such as password file
HIGH:
Stored Cross-Site Scripting (XSS) – An authenticated user can embed malicious JavaScript code in a page, which will be executed whenever any user accesses that page.
Malicious File Upload – An attacker can upload malicious executable files like shell.php without any restriction, containing malicious content, which might lead to a remote code execution (RCE) attack
Broken Authorisation – An authenticated user can deactivate and delete job alerts of other users without any restriction.
Link Injection – Any authenticated user can embed malicious HTML tags such as hyperlink <a> tag in a page, which may redirect users to a malicious website controlled by the attacker.
And many more
Software as a service (SaaS)
What we found:
HIGH:
-
Stored Cross-Site Scripting (XSS) – An authenticated user can embed malicious JavaScript code in a page, which will be executed whenever any user accesses that page.
-
Malicious File Upload – An attacker can upload CSV (excel) files without any restriction, containing malicious content, which might lead to other cyber-attacks such as insecure redirection, user account takeover, etc.
-
Host Header Injection – An attacker can redirect the users to a malicious website controlled by the attacker and carry out various attacks such as session hijacking, malware download, etc.
-
HTML Injection – Any authenticated user can embed malicious HTML tags such as hyperlink <a> tag in a page, which may redirect users to a malicious website controlled by the attacker.
-
And many more
Mobile: Crypto loan and investment wallet app
What we found:
HIGH:
Fake user account creation with invalid mobile number – An attacker can create unlimited bogus/fake user accounts using automated scripts, due to which the backend database will be overloaded with fake user accounts.
Firebase database publicly exposed – An attacker can gain sensitive information about a user, such as email ID, username and token.
Lack of binary protection – An attacker can use an automated tool to reverse engineer the code and modify it using malware to perform some hidden functionality.
Application signed with a debug certificate – An attacker can debug the application activities/ communication and perform a Man-in-the-Middle attack.
SQL Injection – An attacker can supply SQL payloads in the user input field and dump the whole database containing all the user’s sensitive data.
And many more
Cryptocurrency token and wallet application
What we found:
HIGH:
Sensitive Information Disclosure – An attacker can access the user credentials or application data without any restriction and could use them for authentication bypass or social engineering attacks.
Business Logical Flaw – A user can create a wallet with wrong collection settings, which could lead to flaws in business logic while funding transactions.
Lack of binary protection – An attacker can use an automated tool to reverse engineer the code and modify it using malware to perform some hidden functionality.
Misconfiguration in Manifest/plist – An attacker can conduct a man-in-the-middle attack since application traffic is transmitted in clear text format.
Insecure Data Storage – An attacker can use the information stored in the app folder for further attacks, which may lead to user account takeover.
And many more
Network: MAS licensed remittance company
What we found:
CRITICAL:
Default admin login on routers and VoIPs – An attacker can steal sensitive data by sniffing the traffic going through the routers/ VoIPS and can implant its exploit to compromise all other systems present in the internal network.
Default admin login on biometric device – An attacker can add, modify, and delete user accounts and related details from biometric devices without anyone’s knowledge.
Microsoft SMB EternalBlue Remote Code Execution – An attacker can take full control over the server with SYSTEM privileges and steal sensitive data or credentials of other logged-in users.
HIGH:
Malicious File Upload – An attacker can upload malicious executable files on the web server, which can get executed at the back end whenever a user accesses or views that particular file
XMLRPC DOS Attack – An attacker can access the xmlrpc.php file without any authentication and conduct a DOS attack against the web server
Synology DiskStation Manager (Multiple Vulnerabilities) – An input validation error exists in the ‘externaldevices.cgi’ script that allows any administrative user to execute arbitrary commands with root privileges on the remote host.
Unsupported Windows OS – An attacker can conduct numerous exploits against outdated IIS servers such as RCE, DoS, Buffer Overflow, Command Injection, etc.
And many more
Network: MAS licensed remittance company
Our Clients
Client Testimonials





Request for your Network Penetration Testing Quote
Here’s what you’ll receive:
🔴 Pinpoint the ideal security assessment for your project to ensure you only pay for what you truly need.
🔴 Review tailored sample reports to know exactly what to expect, ensuring actionable and understandable insights.
🔴 Secure an unbeatable deal with our exclusive price beat guarantee, offering you top-quality assessments at the best price in the market.

