KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






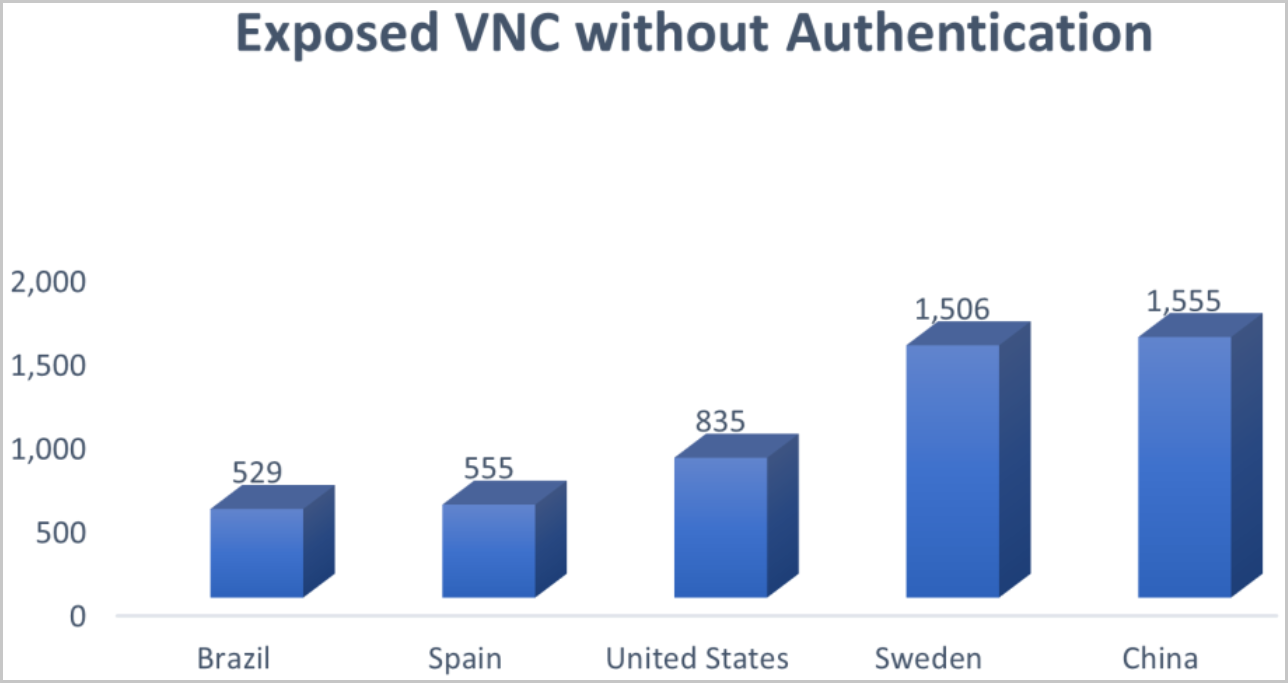
Researchers have discovered at least 9,000 exposed VNC (virtual network computing) endpoints that can be accessed and used without authentication, allowing threat actors easy access to internal networks.
VNC (virtual network computing) is a platform-independent system meant to help users connect to systems that require monitoring and adjustments, offering control of a remote computer via RFB (remote frame buffer protocol) over a network connection.
If these endpoints aren’t properly secured with a password, which is often the result of negligence, error, or a decision taken for convenience, they can serve as entry points for unauthorized users, including threat actors with malicious intentions.
Depending on what systems lie behind the exposed VNCs, like, for example, water treatment facilities, the implications of abusing access could be devastating for entire communities.
Also Read: How to secure data on cloud: best practices from 3 case studies
Security weakness hunters at Cyble scanned the web for internet-facing VNC instances with no password and found over 9,000 accessible servers.
.png)
Most of the exposed instances are located in China and Sweden, while the United States, Spain, and Brazil followed in the top 5 with significant volumes of unprotected VNCs.
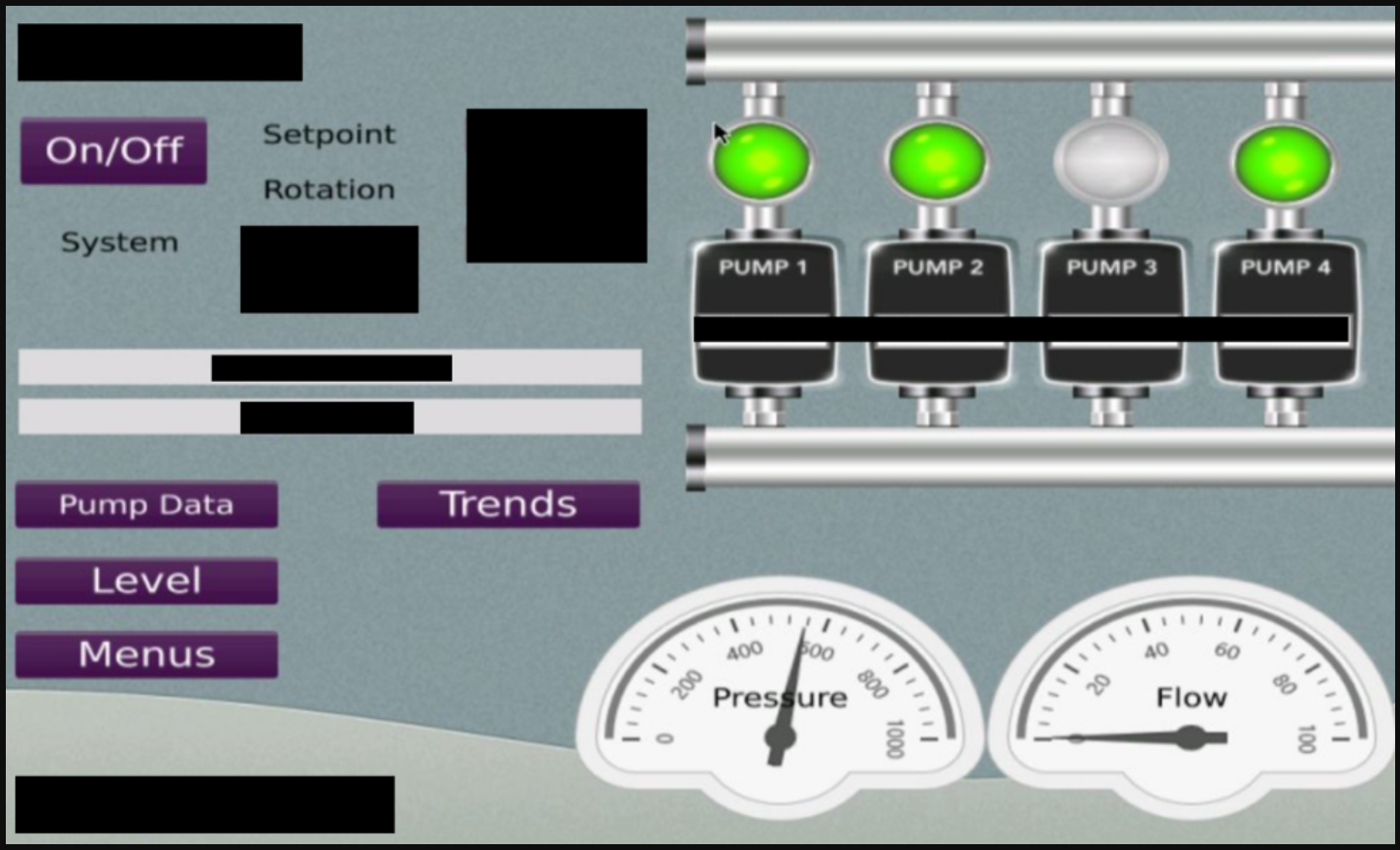
To make matters worse, Cybcle found some of these exposed VNC instances to be for industrial control systems, which should never be exposed to the Internet.
“During the course of the investigation, researchers were able to narrow down multiple Human Machine Interface (HMI) systems, Supervisory Control And Data Acquisition Systems (SCADA), Workstations, etc., connected via VNC and exposed over the internet,” details Cyble in the report.
In one of the explored cases, the exposed VNC access led to an HMI for controlling pumps on a remote SCADA system in an unnamed manufacturing unit.
Also Read: Personal data protection in the MCST context: 3 Case studies
To see how often attackers target VNC servers, Cyble used its cyber-intelligence tools to monitor for attacks on port 5900, the default port for VNC. Cyble found that there were over six million requests over one month.
Most attempts to access VNC servers originated from the Netherlands, Russia, and the United States.
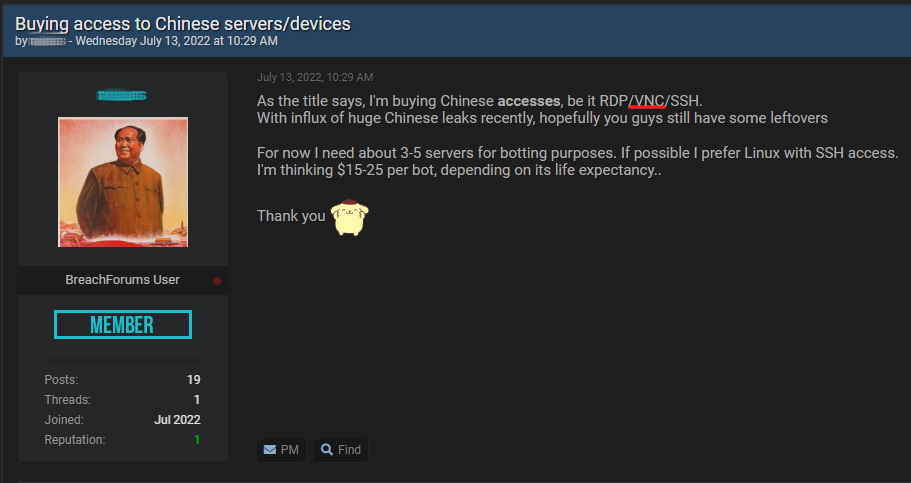
Demand for accessing critical networks via exposed or cracked VNCs is high on hacker forums, as this kind of access can, under certain circumstances, be used for deeper network infiltration.
“Adversaries may abuse VNC to perform malicious actions as the logged-on user such as opening documents, downloading files, and running arbitrary commands,” a Cyble researcher told Bleeping Computer during a private discussion.
“An adversary could use VNC to remotely control and monitor a system to collect data and information to pivot to other systems within the network.”
In other cases, security enthusiasts offer instructions on how users can scan and locate these exposed instances on their own.
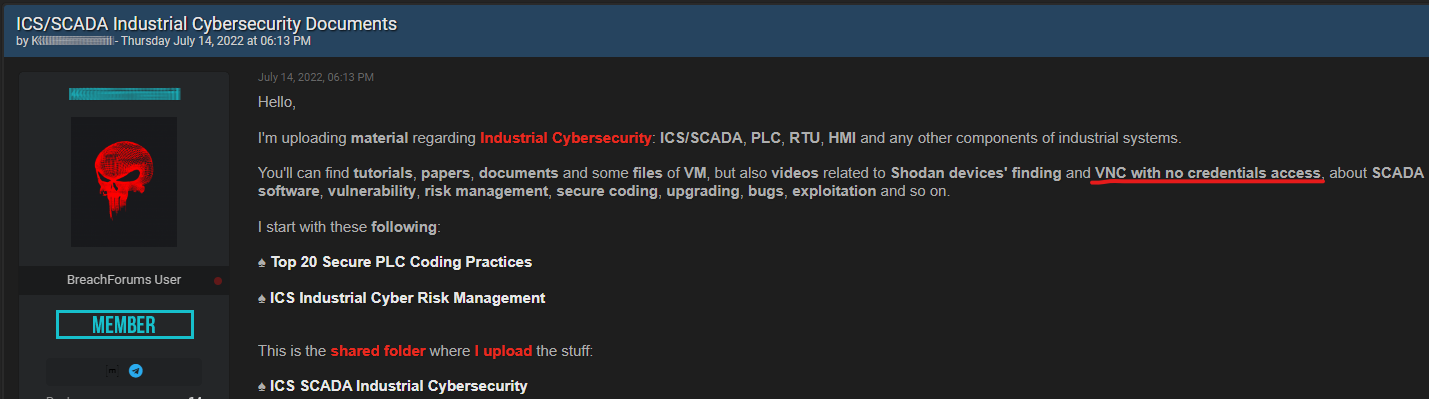
A darknet forum post seen by Bleeping Computer features a long list of exposed VNC instances with very weak or no passwords.
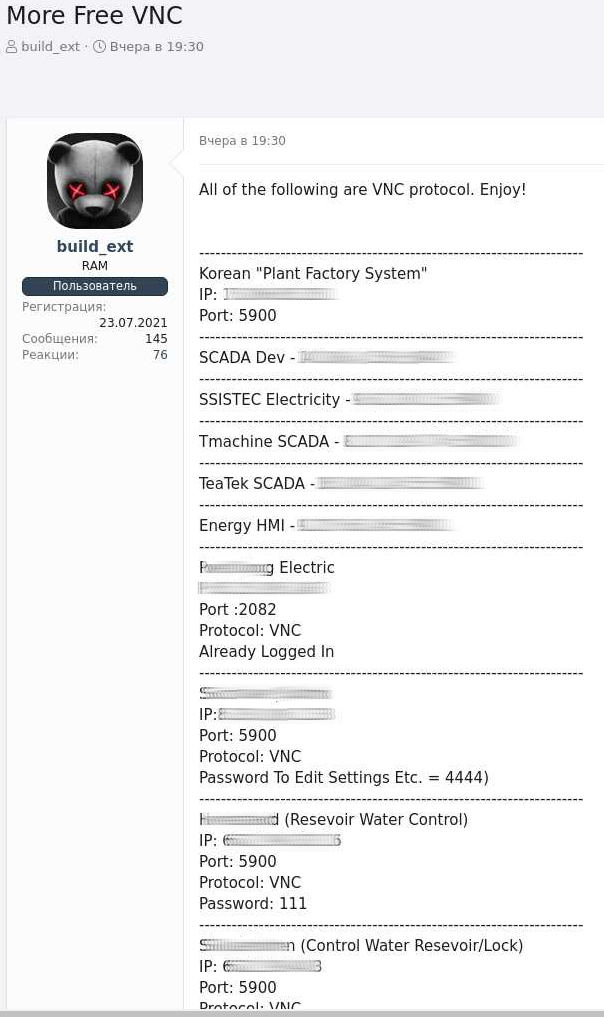
The case of weak passwords raises another concern around VNC security, as Cyble’s investigation only focused on instances that had the authentication layer completely disabled.
If poorly secured servers whose passwords are easy to crack were included in the investigation, the number of potentially vulnerable instances would be much more significant.
On that front, it is essential to remember that many VNC products do not support passwords longer than eight characters, so they are inherently insecure even when the sessions and passwords are encrypted.
VNC admins are advised to never expose servers directly to the Internet, and if they must be remotely accessible, at least place them behind a VPN to secure access to the servers.
Even then, admins should always add a password to instances to restrict access to the VNC servers.