KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Researchers have discovered 27 vulnerabilities in Eltima SDK, a library used by numerous cloud providers to remotely mount a local USB device.
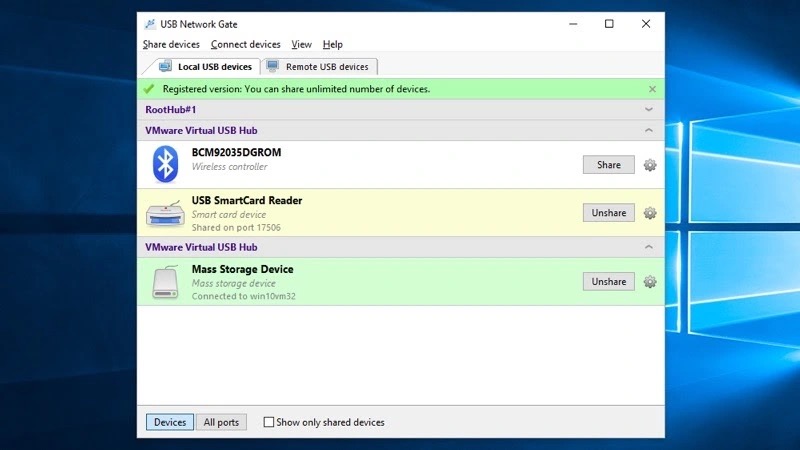
Due to the pandemic and the rising trend of working from home, organizations have begun to rely heavily on cloud-based services. This necessity also increased cloud providers utilizing Eltima’s SDK that allow employees to mount local USB mass storage devices for use on their cloud-based virtual desktops.
Also Read: Top 10 Best Freelance Testing Websites That Will Pay You
However, as cloud desktop providers, including Amazon Workspaces, rely on tools like Eltima, SentinelOne warned that millions of users worldwide have become exposed to the discovered vulnerabilities.
The implications of exploiting the flaws are significant as they could allow remote threat actors to gain elevated access on a cloud desktop to run code in kernel mode.
“These vulnerabilities allow attackers to escalate privileges enabling them to disable security products, overwrite system components, corrupt the operating system, or perform malicious operations unimpeded,” explained a new report by Sentinel Labs.
This elevated access could allow malware to steal credentials that threat actors can use to breach an organization’s internal network.
In total, there are 27 vulnerabilities discovered by SentinelOne, with the CVE IDs listed below:
CVE-2021-42972, CVE-2021-42973, CVE-2021-42976, CVE-2021-42977, CVE-2021-42979, CVE-2021-42980, CVE-2021-42983, CVE-2021-42986, CVE-2021-42987, CVE-2021-42988, CVE-2021-42990, CVE-2021-42993, CVE-2021-42994, CVE-2021-42996, CVE-2021-43000, CVE-2021-43002, CVE-2021-43003, CVE-2021-43006, CVE-2021-43637, CVE-2021-43638, CVE-2021-42681, CVE-2021-42682, CVE-2021-42683, CVE-2021-42685, CVE-2021-42686, CVE-2021-42687, CVE-2021-42688These vulnerabilities have been responsibly disclosed to Eltima, who has already released fixes for affected versions. However, it is now up to cloud services to upgrade their software to utilize the updated Eltima SDK.
Also Read: PDP Act (Personal Data Protection Act) Laws and Regulation
According to SentinelOne, the affected software and cloud platforms are:
It is important to note that Sentinel Labs hasn’t looked into all possible products that could incorporate the vulnerable Eltima SDK, so there could be more products affected by the set of flaws.
Also, some services are vulnerable on the client-side, others on the server-side, and a few on both, depending on code-sharing policies.
Sentinel Labs clarifies that it has seen no evidence that threat actors have exploited these vulnerabilities. Still, now that a technical report has been released, we will likely see exploitation in the future.
Out of an abundance of caution, admins should revoke privileged credentials before applying the security updates, and logs should be scrutinized for signs of suspicious activity.
Most vendors have patched the flaws and pushed them through automatic updates. However, some require end-user action to apply the security updates, like upgrading the client app to the latest available version.
Below is a list of fixes released by different vendors: