KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







OpenSea users are being targeted in an ongoing and aggressive Discord phishing attack to steal cryptocurrency funds and NFTs.
Over the past week, threat actors have been lurking in OpenSea’s Discord server, pretending to be official support representatives for the site.
These fake support reps provide private “support” to OpenSea users needing help, which invariably leads to the loss of cryptocurrency and NFT collectibles stored in the victim’s MetaMask wallets.
Also Read: Top 3 Common Data Protection Mistakes, Revealed
When an OpenSea user needs support, they can request help at OpenSea’s help center or via the site’s Discord server.
When a user joins the Discord server and posts a request for help, scammers lurking on the server start sending private messages to the user. These messages include an invite to an ‘OpenSea Support’ server to receive support, as shown below.
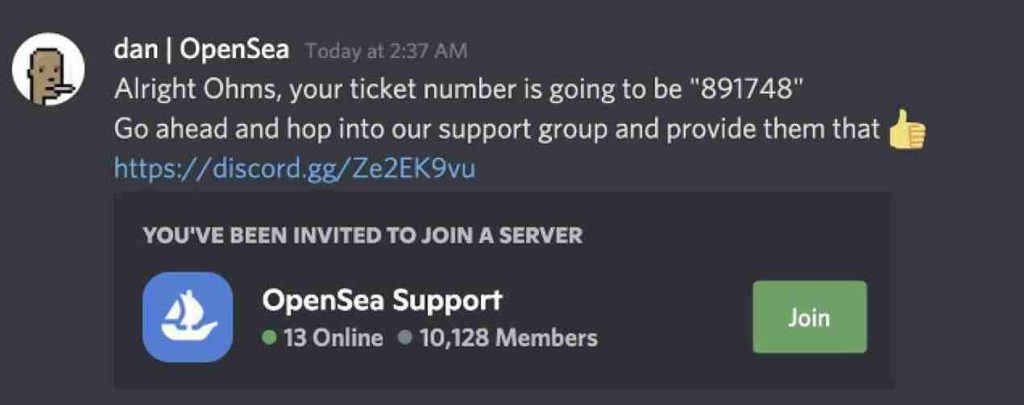
Artist Jeff Nicholas, who fell victim to this scam, told BleepingComputer that after joining the fake OpenSea support server, the scammers asked him to open a screen share so that they provide support and guidance in fixing the problem.
“Lots of grooming, “working through the issue” pulling you in. Then ask you to screenshare so they can see wha you are seeing,” Nicholas told BleepingComputer.com.
As part of this process, the fake support member states tells the victim that they need to resynch their MetaMask Chrome extension with the MetaMask mobile app.
“Say you need to resync you MM and at this point your sort of sucked in to fixing this thing whatever it is. Pull up QR code and it immediately says “synced” (because they scanned it). So then they basicly have your seed phrase (without actually having it),” explained Nicholas.
To synch your mobile MetaMask wallet with your Chrome extension, it is possible to go to Settings > Advanced > Sync with mobile. You will be prompted to enter your password on this page, and a QR code will be displayed.
Also Read: The Financial Cost of Ransomware Attack
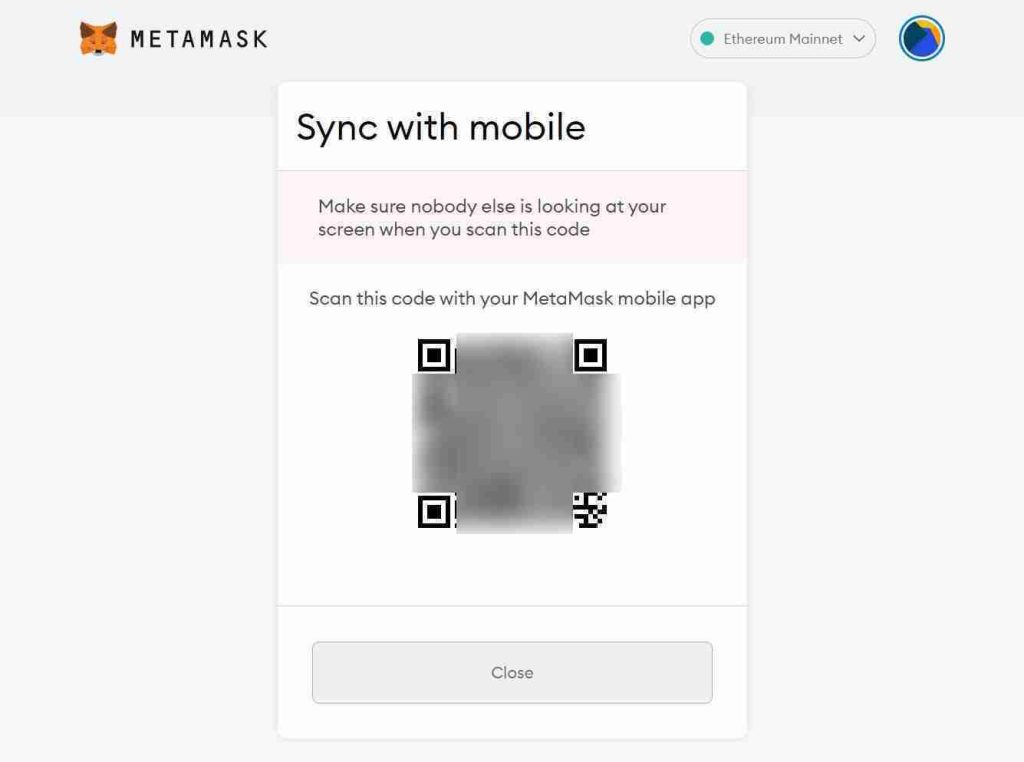
The mobile MetaMask app can scan this QR code to synch and import your Chrome wallet automatically. However, anyone who sees this QR code, including the fake support reps, can create a screenshot and then use that image to synch your wallet into their mobile apps.
When the fake support representatives scanned the QR code on their mobile app, they now had full access to the cryptocurrency and any NFT collectibles stored within it. The threat actors then transfer the victims to their wallets.
OpenSea is aware of the attacks and recommends that users only open support requests through their help center.
“Saddened to hear an OpenSea user was the victim of a significant phishing attack last night,” tweeted OpenSea’s Head of Product Nate Chastain.
“The scammer masquerades as an OpenSea employee and has the user scan a QR code granting wallet access.”
“Please be vigilant and direct support requests through our Help Center/ZenDesk.”
However, some users feel that OpenSea shares some responsibility for these attacks as they have been referring users to their Discord server for support.
BleepingComputer has contacted OpenSea with questions about these attacks and the proper way to request support but has not heard back,
For now, it is strongly advised that OpenSea users avoid Discord or Twitter for support and only open tickets through the site’s help center.
Sadly, these types of scams are becoming all too common.
In May, TrustWallet and MetaMask users were targeted by Twitter phishing attacks that attempted to steal wallets using fake technical support forms.
After accessing these forms and submitting their recovery phrases, the threat actors transferred the funds from the victim’s wallets.
Also Read: Top 3 Common Data Protection Mistakes, Revealed
The general rule is never to share your wallet’s recovery keys, password phrases, QR codes used for synchronizing to prevent your wallets from being stolen by these types of scams.