KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The threat actors behind the Exorcist 2.0 ransomware are using malicious advertising to redirect victims to fake software crack sites that distribute their malware.
According to security researcher Nao_Sec, PopCash malvertising is redirecting users from legitimate sites to a fake software crack site.
This crack site, shown below, pretends to offer download links for the programs that break copyright protection on commercial software so that it can be used for free.
For example, in the image below, the site pretends to offer a ‘Windows 10 Activator 2020’ that will allow you to activate Windows 10 for free.
Also Read: 8 Simple Ways To Improve Your Website Protection
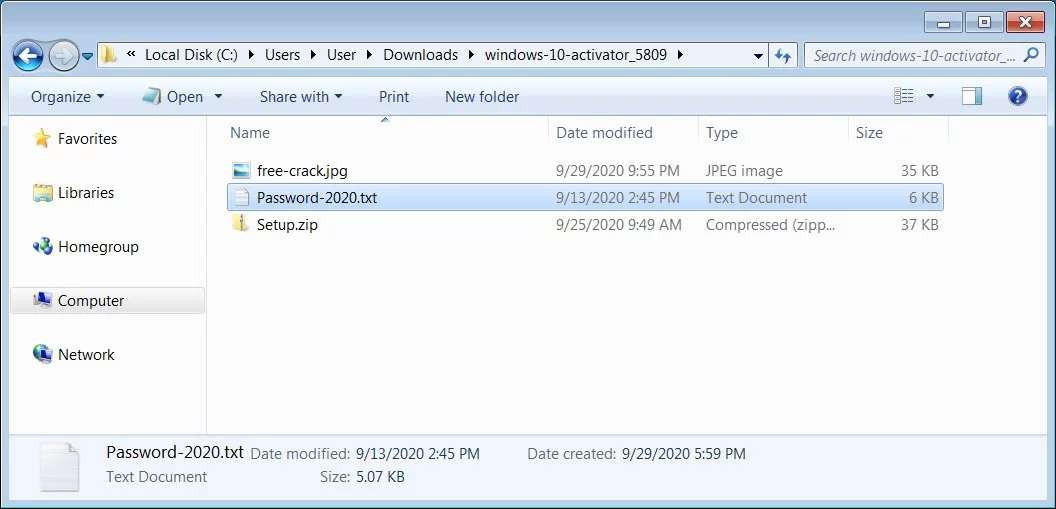
The downloaded archive contains another password-protected zip file and a text file that contains the archive’s password.
By password-protecting the archive, it allows the download to occur without being detected by Google Safe Browsing, Microsoft SmartScreen, or installed security software.
If the setup program is run, though, users will find that their files become encrypted instead of installing free Windows 10 activator, as shown below.
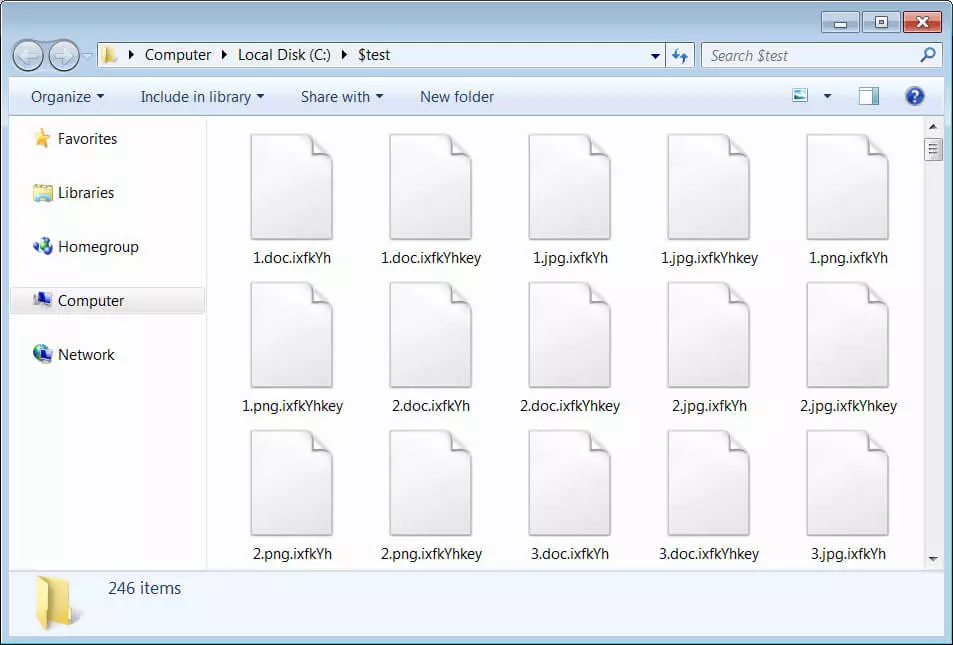
Included in encrypted folders will be ransom notes that contain unique links to a Tor payment site where a victim can get information on how to pay a ransom.
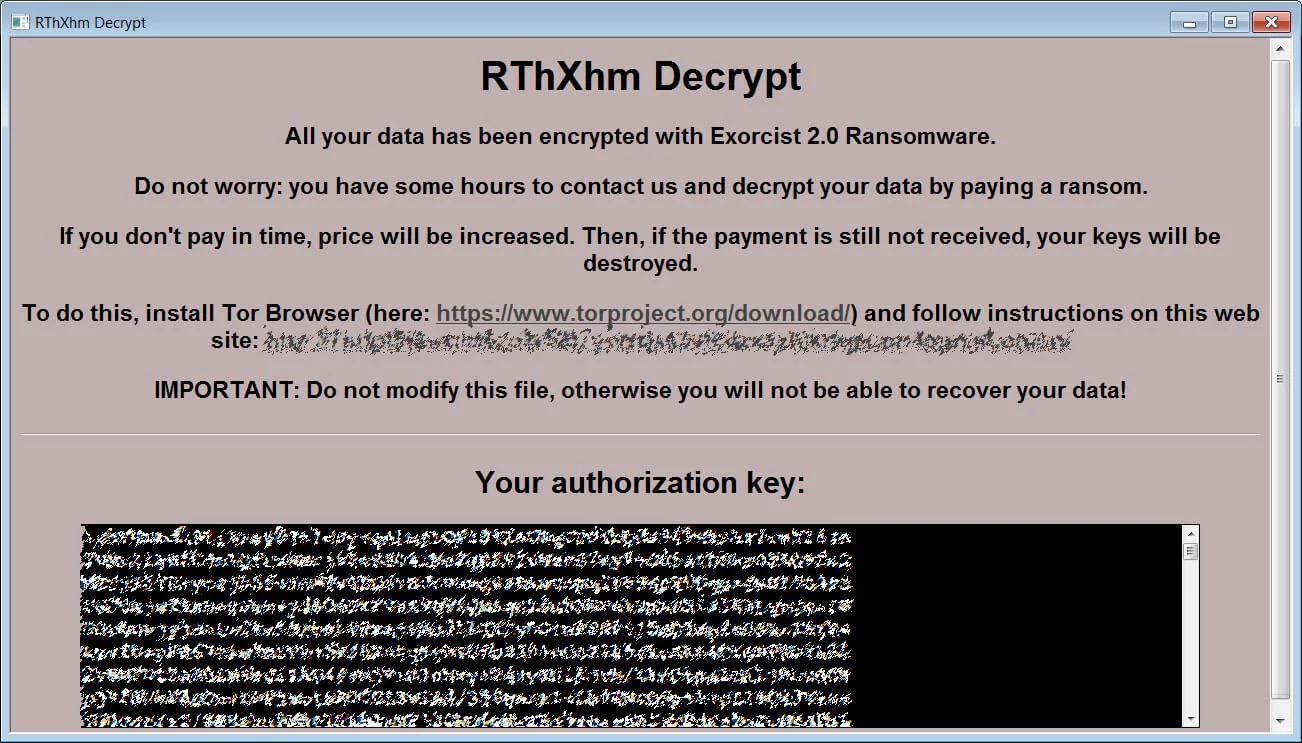
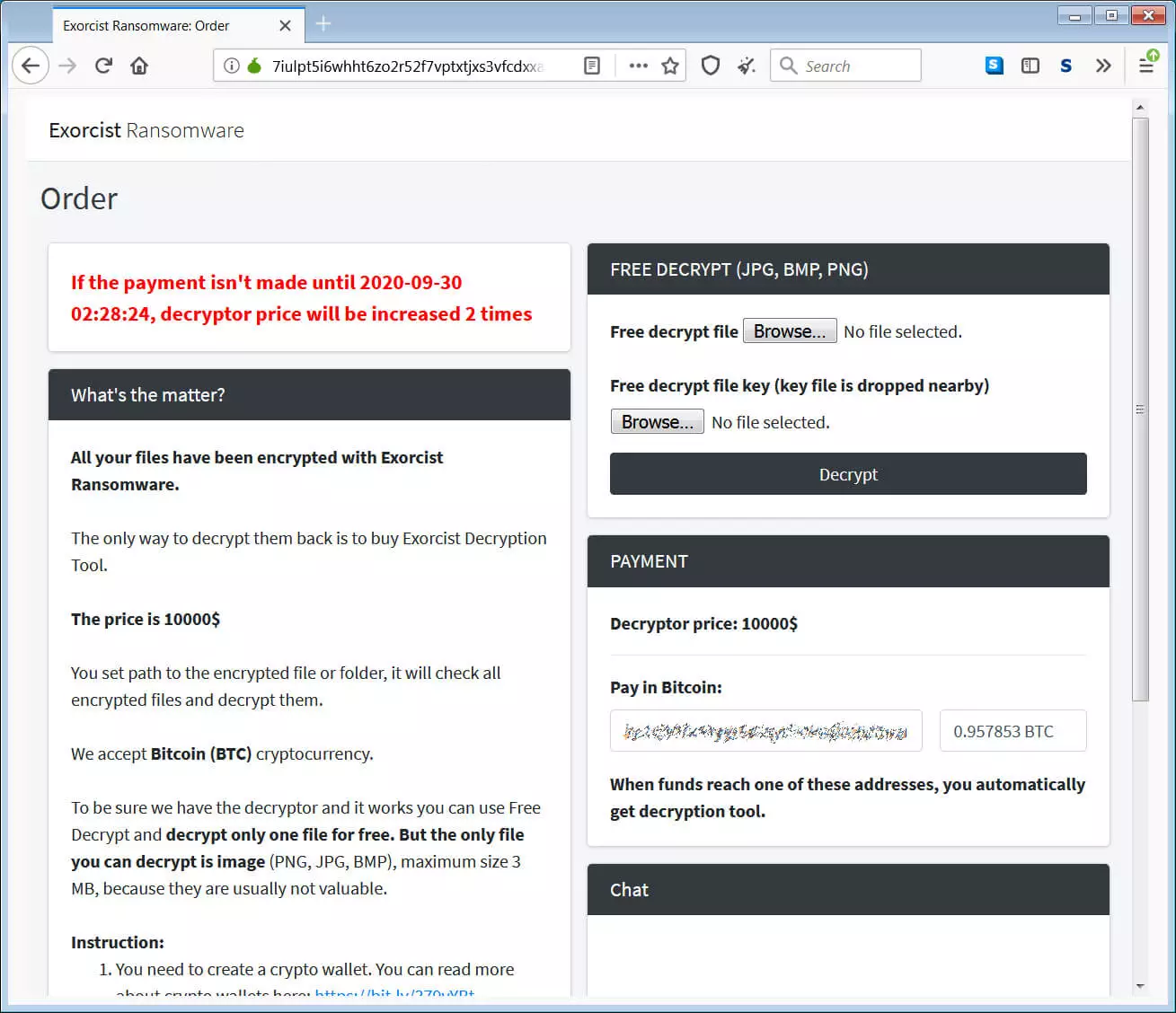
When visiting the Excorcist Tor payment site, victims can get free decryption of one file, a way to chat with the threat actors, and the ransom amount that they need to pay.
From Excorcist ransom notes seen by BleepingComputer, we have seen ransom demands as low as $250 to as higher $10,000. We are sure there are much higher amounts being demanded, depending on the number of files encrypted or other criteria.
Using fake software cracks to distribute the malware is the same tactic used by the STOP Ransomware actors, which led STOP to be the most widespread currently active ransomware.
If Exorcist 2.0 continues to use fake software cracks as their distribution method, we can expect to see a similar rise in victims.

Established in 2018, Privacy Ninja is a Singapore-based IT security company specialising in data protection and cybersecurity solutions for businesses. We offer services like vulnerability assessments, penetration testing, and outsourced Data Protection Officer support, helping organisations comply with regulations and safeguard their data.
Singapore
7 Temasek Boulevard,
#12-07, Suntec Tower One,
Singapore 038987
Latest resources sent to your inbox weekly
© 2025 Privacy Ninja. All rights reserved
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!

Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!
