KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





The European Medicines Agency (EMA) today revealed that some of the stolen Pfizer/BioNTech vaccine candidate data was doctored by threat actors before being leaked online with the end goal of undermining the public’s trust in COVID-19 vaccines.
EMA is the decentralized agency that reviews and approves COVID-19 vaccines in the European Union, and the agency that evaluates, monitors, and supervises any new medicines introduced to the EU.
“The ongoing investigation of the cyberattack on EMA revealed that some of the unlawfully accessed documents related to COVID-19 medicines and vaccines have been leaked on the internet,” the agency disclosed today.
“This included internal/confidential email correspondence dating from November, relating to evaluation processes for COVID-19 vaccines.
“Some of the correspondence has been manipulated by the perpetrators prior to publication in a way which could undermine trust in vaccines.”
EMA revealed that the COVID-19 vaccine data stolen in December was leaked online in a previous update, on Tuesday.
Also Read: What Legislation Exists in Singapore Regarding Data Protection and Security?
BleepingComputer became aware of several threat actors leaking what they claimed to be the stolen EMA data on multiple hacker forums on December 31st.
Several sources in the cybersecurity intelligence community told BleepingComputer that the leaked data archives included email screenshots, EMA peer review comments, as well as Word, PDF, PowerPoint documents.
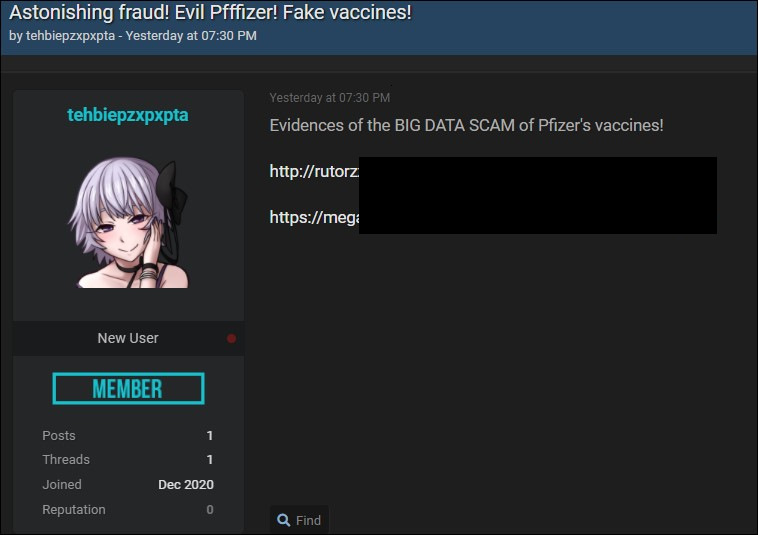
Below is a screenshot of one of the data leaks seen by BleepingComputer at the time, linking to archives containing the altered documents stolen during the EMA attack.
As the screenshot shows, the intent of the threat actor behind the leak was to highlight that the Pfizer COVID-19 vaccine was fake, confirming EMA’s disclosure that the leaked documents were manipulated with the purpose of weakening trust in the vaccines.
Following the December attack, the agency disclosed that it launched a joint investigation in collaboration with law enforcement and several other relevant entities.
Pfizer and BioNTech jointly disclosed that some COVID-19 documents relating to the regulatory submission stored on EMA’s servers were accessed by the threat actors behind the cyberattack.
EMA later revealed that the investigation shows that only a limited number of documents linked to the BNT162b2 COVID-19 vaccine candidate were accessed without authorization during the incident.
EMA also discovered that the data breach was limited to a single IT app, with the threat actors behind this attack primarily targeting data related to COVID-19 vaccines and medicines.
Also Read: Letter of Consent MOM: Getting the Details Right
An EMA spokesperson was not immediately available for comment when contacted by BleepingComputer earlier today.