KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







An Iranian hacking group has been observed camouflaging destructive attacks against Israeli targets as ransomware attacks while maintaining access to victims’ networks for months in what looks like an extensive espionage campaign.
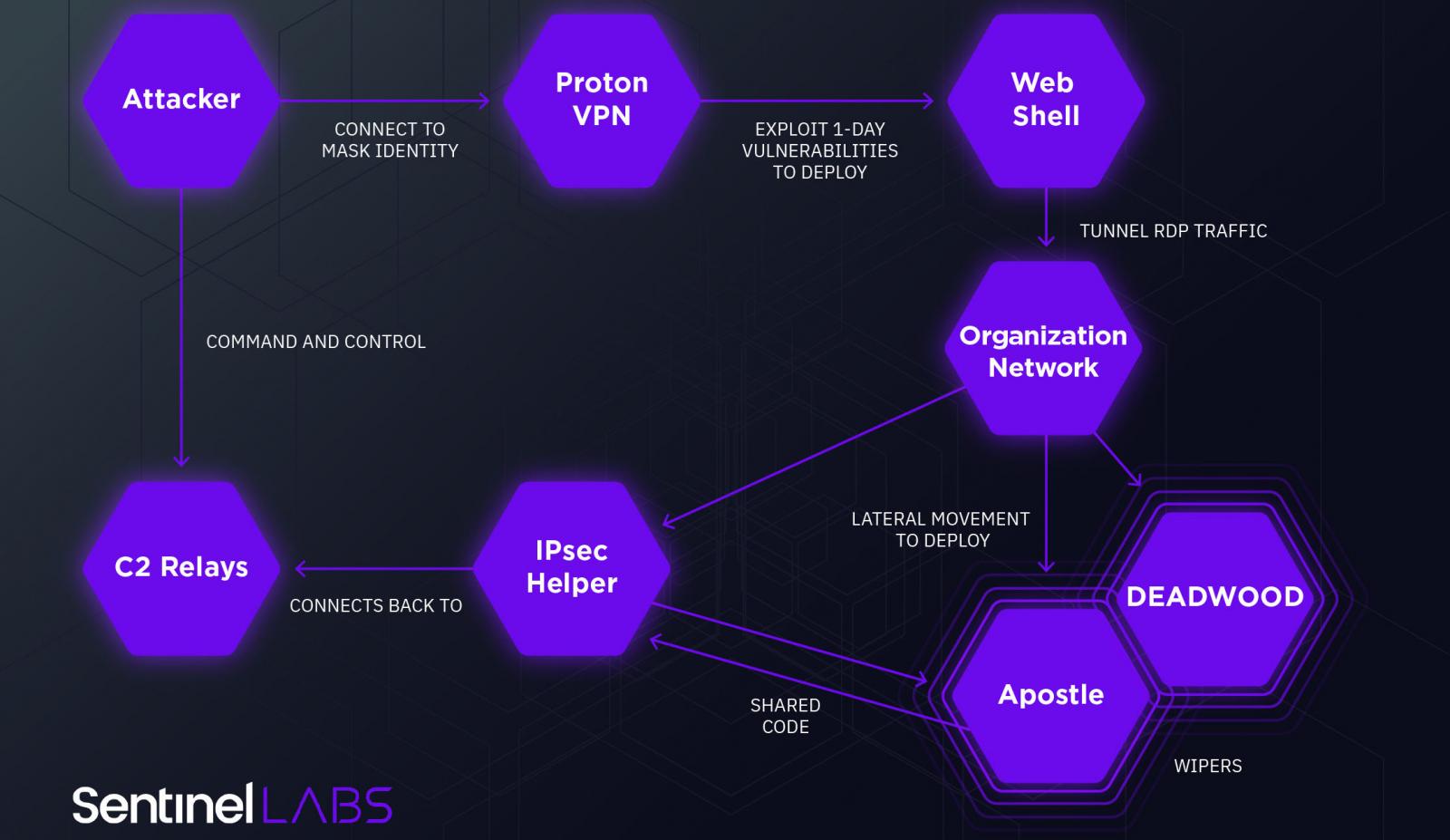
The threat actor, tracked as Agrius by SentinelLabs researchers, has targeted Israel starting with December 2020.
“Initially engaged in espionage activity, Agrius deployed a set of destructive wiper attacks against Israeli targets, masquerading the activity as ransomware attacks,” said Amitai Ben Shushan Ehrlich, Threat Intelligence Researcher at SentinelOne.
At first, the group deployed a wiper malware known as DEADWOOD (or Detbosit) designed to destroy data on infected devices and previously used in attacks against Saudi Arabian targets in 2019.
Agrius has slowly transitioned into using a new wiper malware dubbed ‘Apostle,’ which, although broken in its first variants, has gradually replaced DEADWOOD and was upgraded into a fully-featured ransomware strain.
The attackers have used multiple attack vectors, including SQL injection, FortiOS CVE-2018-13379 exploits, and exploits targeting various 1-day web app vulnerabilities.
“We believe the implementation of the encryption functionality is there to mask its actual intention: destroying victim data,” the researcher added.
Also Read: PDPA Singapore Guidelines: 16 Key Concepts for Your Business
“This thesis is supported by an early version of Apostle that the attacker’s internally named ‘wiper-action.’ This early version was deployed in an attempt to wipe data but failed to do so possibly due to a logic flaw in the malware.
“The flawed execution led to the deployment of the DEADWOOD wiper. This, of course, did not prevent the attackers from asking for a ransom.”
The Iranian hackers have also developed their own custom .NET malware named ‘IPsec Helper’ designed to provide the threat actor with basic backdoor capabilities to help deliver additional malware on compromised hosts and exfiltrate data.
A complete list of all commands supported by the IPsec Helper backdoor is available in SentinelOne’s full report.
Agrius is not the first threat group linked to Iran that deploys destructive wiper malware against Middle-Eastern targets.
The suspected Iranian-backed APT33 hacking group is believed to have been behind multiple attacks that used the Shamoon wiper against targets from the Middle East and Europe [1, 2].
Data-wiping malware dubbed ZeroCleare by IBM researchers and developed by Iran-backed threat actors tracked as APT34 (aka Oilrig, ITG13) and Hive0081 (aka xHunt) was also spotted in attacks targeting organizations from the energy and industrial sector in the Middle East.
The Cybersecurity and Infrastructure Security Agency (CISA) also warned in June 2019 of an increase in Iranian-backed cyberattacks utilizing destructive wiper tools against US industry and government agencies.
State-sponsored actors have historically used wiper attacks to cover up other campaigns, including cyber-espionage efforts.
Another Iranian-backed hacking group known as Fox Kitten has also been linked to the Pay2Key ransomware operation that targets organizations from Israel and Brazilin since November, hinting at a more extensive Iranian coordinated campaign.
Also Read: Data Protection Officer Singapore | 10 FAQs
“The usage of ransomware as a disruptive tool is usually hard to prove, as it is difficult to determine a threat actor’s intentions,” the SentinelOne researcher concluded.
“Analysis of the Apostle malware provides a rare insight into such attacks, drawing a clear line between what began as a wiper malware to a fully operational ransomware.”