KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Ireland’s Health Service Executive (HSE), the country’s publicly funded healthcare system, has shut down all IT systems after its network was breached in a ransomware attack.
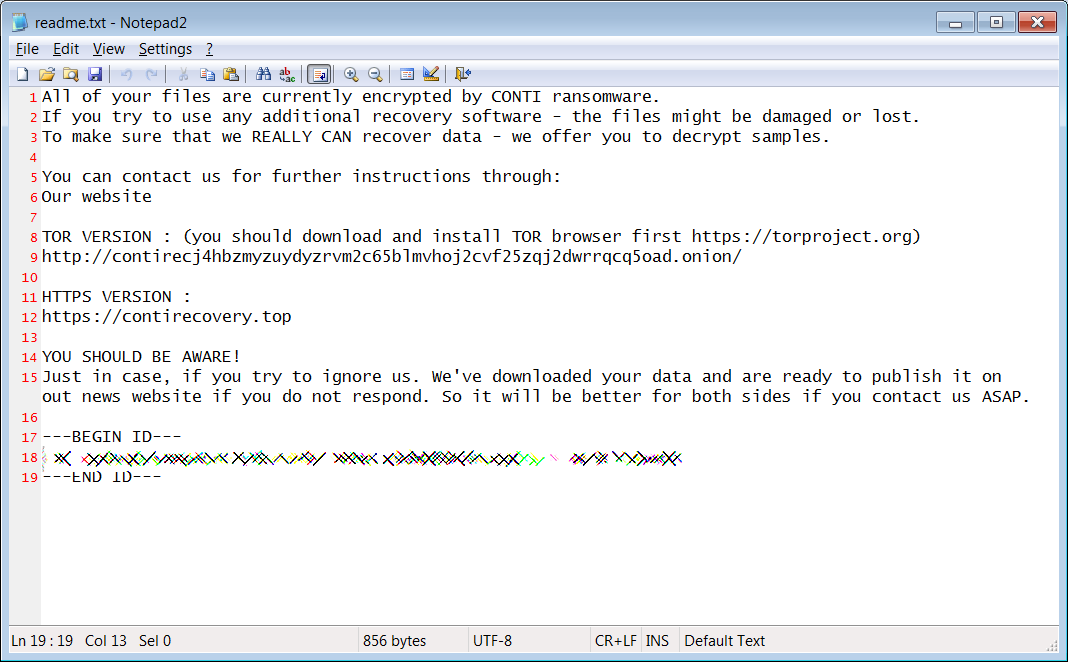
HSE Chief Executive Paul Reid told NewstalkFM that this is a “Conti human-operated ransomware attack that seeks to get access to data.”
This ransomware gang also hit the Scottish Environment Protection Agency (SEPA) on Christmas Eve, later publishing roughly 1.2 GB of stolen data on their dark web leak site.
Conti ransomware was first spotted in isolated attacks at the end of December 2019. It shares code with the notorious Ryuk Ransomware, whose TrickBot-powered distribution channels it took over after Ryuk activity dwindled in July 2020.
Conti operators are known for breaching enterprise networks and spreading laterally until gaining access to domain admin credentials which allow them to deploy the ransomware payloads filelessly, using reflective DLL injection techniques.
Conti operates as a private Ransomware-as-a-Service (RaaS) that recruits hackers to deploy the ransomware in exchange for large shares of any paid ransom.
A sample of the ransomware used in the HSE attack and shared with BleepingComputer appends the .FEEDC extension to encrypted files.
Also Read: PDPA Singapore Guidelines: 16 Key Concepts For Your Business
“There is a significant ransomware attack on the HSE IT systems,” the Irish national health service said.
“This has caused some disruption to our services. But most healthcare appointments will go ahead as planned.
“We have taken the precaution of shutting down all our IT systems in order to protect them from this attack and to allow us fully assess the situation with our own security partners.”
HSE Ireland also added that the country’s National Ambulance Service and emergency departments (EDs) operate normally, with no direct impact from the ransomware attack on ambulance dispatch and call handling.
Even though most hospital appointments are not affected, some hospitals are affected by service disruptions, including the Rotunda Maternity Hospital and the Cork University Hospital, where some appointments have been canceled (more info here.)
While COVID-19 vaccine appointments are not impacted and scheduled COVID-19 tests are going ahead as planned, the HSE will not be able to refer people for COVID-19 tests until systems are brought back online.
Reid also told RTÉ earlier today that the threat actors behind this “very sophisticated attack” haven’t yet made a ransom demand.
He added that HSE’s security teams are currently investigating the incident to fully understand the effects of the incident.
“We apologize for inconvenience caused to patients and to the public and will give further information as it becomes available,” the HSE said.
In March, US hospital and healthcare services provider Universal Health Services (UHS) said that a Ryuk ransomware attack suffered in September 2020 had an estimated impact of $67 million.
The US government also warned the healthcare industry in October 2020 that a hacking group is targeting hospitals and healthcare providers in Ryuk ransomware attacks.
Also Read: Data Protection Officer Singapore | 10 FAQs
The ransomware attack on Ireland’s HSE comes one week after Colonial Pipeline, the largest US fuel pipeline, shut down operations after the DarkSide ransomware gang breached its network.