KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







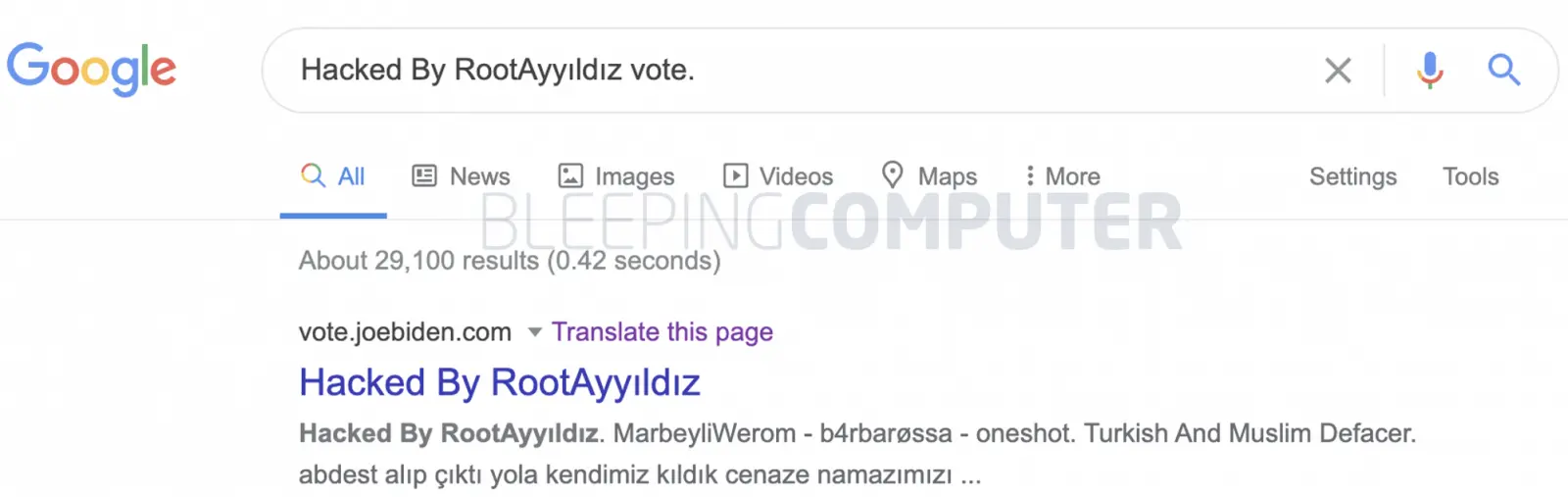
This week, the Vote Joe site set up by the Biden-Harris Presidential campaign had been hacked and defaced by a Turkish hacker called RootAyyildiz.
Based on the evidence and the archived snapshots of the site, it appears the breach and defacement had lasted for over 24 hours.
Up until November 9th or so, days after the 2020 U.S. Presidential Election, the vote.joebiden.com site would redirect to iwillvote.com, according to the Internet Archive’s Wayback Machine.
However, this week the Vote Joe site had been taken over, defaced, and started showing a message in Turkish, put forth by the attackers.
Although the Vote Joe site has now been taken offline, BleepingComputer observed Google continues to cache a defaced copy at the time of writing.
Also Read: Key PDPA Amendments 2019/2020 You Should Know
As per the note left by the hackers on the hacked site, “RootAyyildiz” has claimed responsibility for the hack.
Alongside, there is also mention of other usernames and aliases such as “MarbeyliWerom,” “b4rbarøssa”, “oneshot,” and “Turkish And Muslim Defacer.”

An English translation of the message explicitly states that the hackers behind the breach are not a “group,” despite multiple aliases listed in the note.
“RootAyyildiz is not a Group or an Organization, but a Vatan Lover who Fights alone,” reads the translation.
Vatan and Watan are words for “motherland” or “homeland” in Arabic, Turkish, Urdu, and similar languages.
The defacement is a Turkish message warning “US-backed so-called political parties like chp hdp good party” to stop trying to influence politics in Turkey.
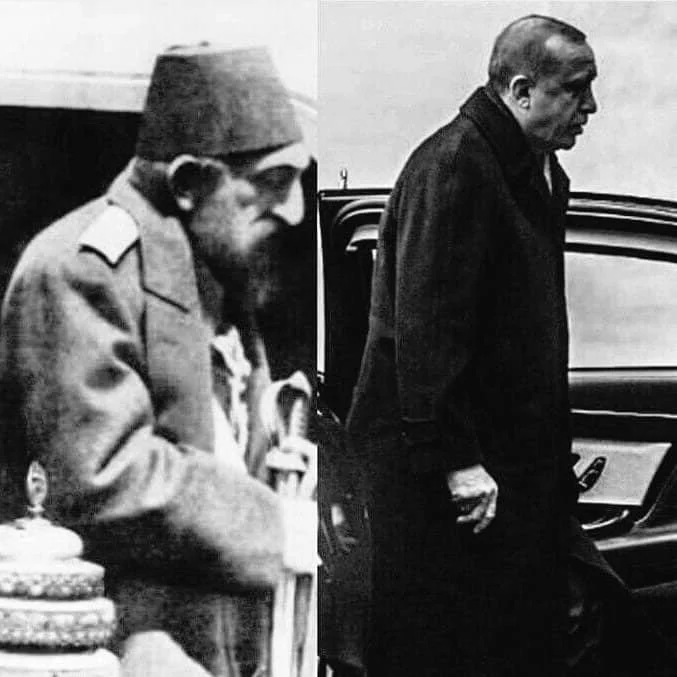
The note further contains a photo of the 34th Sultan of the Ottoman Empire, Abdul Hamid II.
Also Read: The 5 Benefits Of Outsourcing Data Protection Officer Service
A fine print below the photo is likely a reference to the failed Turkish coup d’état of July 15, 2016.
“We; We are the ones who stopped the tanks with their bare hands on the night of July 15. We are those who killed death that night. We have been waiting for Archers Hill for 15 centuries! We are the guardians of that golden banner that will never miss its shadow on us.”
At the time of writing, BleepingComputer observed the vote.joebiden.com domain was no longer accessible.
While it is unknown what security flaw had led to the site’s defacement, this isn’t the first instance of a Presidential campaign web service being vulnerable.
Earlier this month, a website set up hastily by the Trump campaign for people to report “rejected votes” was leaking voter data and was reportedly vulnerable to SQL Injection.
In September 2020, US Presidential apps designed by both Trump and Biden campaigns were riddled with security and user tracking flaws.