KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







An advanced hacking group believed to be working for the Russian government has compromised the internal network of a think tank in the U.S. three times.
Incident responders from cybersecurity company Volexity investigating the attacks between late 2019 and July 2020 named the threat actor Dark Halo, a versatile adversary capable to quickly switch to different tactics and techniques to carry out long-term, stealthy operations.
In one attack, Dark Halo leveraged a newly disclosed vulnerability for the Microsoft Exchange server that allowed them to bypass multi-factor authentication (MFA) defenses against unauthorized email access.
In another, the actor used a trojanized update for the SolarWinds’ network and applications monitoring platform Orion that enabled the breach of cybersecurity company FireEye and several U.S. government networks.
When investigating the first incident, Volexity discovered that the attacker used “multiple tools, backdoors, and malware implants that had allowed the attacker to remain undetected for several years.”
Dark Halo primarily used living-off-the-land utilities in weekly operations, aiming to extract emails from select individuals (executives, policy experts, IT staff). The attacker deployed malware and tools only when they had no choice.
“Dark Halo did use malware and red-teaming tools but largely only for specific one-time tasks as a fallback mechanism when other avenues of access were cut off”
– Volexity
After being kicked out of the victim’s network the first time, Dark Halo found their way back by exploiting a remote code execution vulnerability in the on-premise Microsoft Exchange server.
The flaw, tracked as CVE-2020-0688, had received a patch on February 11 and technical details about it were published two weeks later. By early March, Volexity had observed advanced hackers attempting and even successfully exploiting the vulnerability.
Also Read: MAS Technology Risk Management Guidelines
After getting in, Dark Halo was able to log into a victim’s email account via Outlook Web App (OWA) using only the stolen username and password, despite the protection of Duo’s multi-factor authentication system.
MFA is a second authentication challenge defending against unauthorized access using the legitimate username and password combination.
The log from the Duo authentication server showed no login attempt for that account, so the MFA challenge was not presented at login. Logs from the Exchange server confirmed that the attacker had obtained access only by providing the correct username and password.
Investigating further, Volexity discovered that Dark Halo had not relied on a vulnerability but used a “novel technique” that took advantage of the normal MFA flow.
Analyzing the memory of the OWA server, the researchers discovered that the attacker had gained access to the protected email account by providing a cookie for the Duo MFA session called “duo-sid.”
Generating the cookie was possible after compromising the OWA server and stealing the secret key integrating Duo with OWA, known as akey, a user-generated string unknown to Duo and essential for the multi-factor authentication to work,
In its documentation, Duo advises admins to treat the akey like a password and store it “in a secure manner with limited access,” and to transfer it only over secure channels.
Volexity says that the akey allowed the attacker to derive a pre-computed value and place it in the duo-sid cookie so that the Duo server accepted it as valid.
“This allowed the attacker with knowledge of a user account and password to then completely bypass the MFA set on the account”
– Volexity
The researchers emphasize that this trick was not a vulnerability in the Duo authentication system. The hackers were operating with administrator privileges on the network, so they had access to the secret keys and data.
Also Read: How To Check Data Breach And How Can We Prevent It
Determined in their path to steal email messages of interest, Dark Halo breached the organization for the third time in July 2020.
By the time Volexity started to investigate the incident, the customer had rebooted compromised machines multiple times, obliterating any forensic evidence present in the volatile memory.
The researchers could not determine how exactly the hackers got in but suspected that the SolarWinds server had somehow played an important part.
Once FireEye released details about the malware planted in the Orion update, Volexity saw the technical overlap with this breach, enabling the researchers to attribute the Dark Halo intrusions to the same actor that compromised SolarWinds.
It appears that the attacker got what they wanted, exporting the messages of interest to password-protected archives on the victim’s OWA server and then transferring the data over simple HTTP requests.
Volexity provides additional technical details observed during this attack, including command-line actions for reconnaissance and lateral movement, tools, and infrastructure.
After FireEye disclosed the breach on their network and announced that an attacker (tacked as UNC2452) likely acting on behalf of a government had accessed certain tools used for red-team operations, news broke of the SolarWinds Orion supply-chain attack impacting high-profile organizations in the private and government sector.
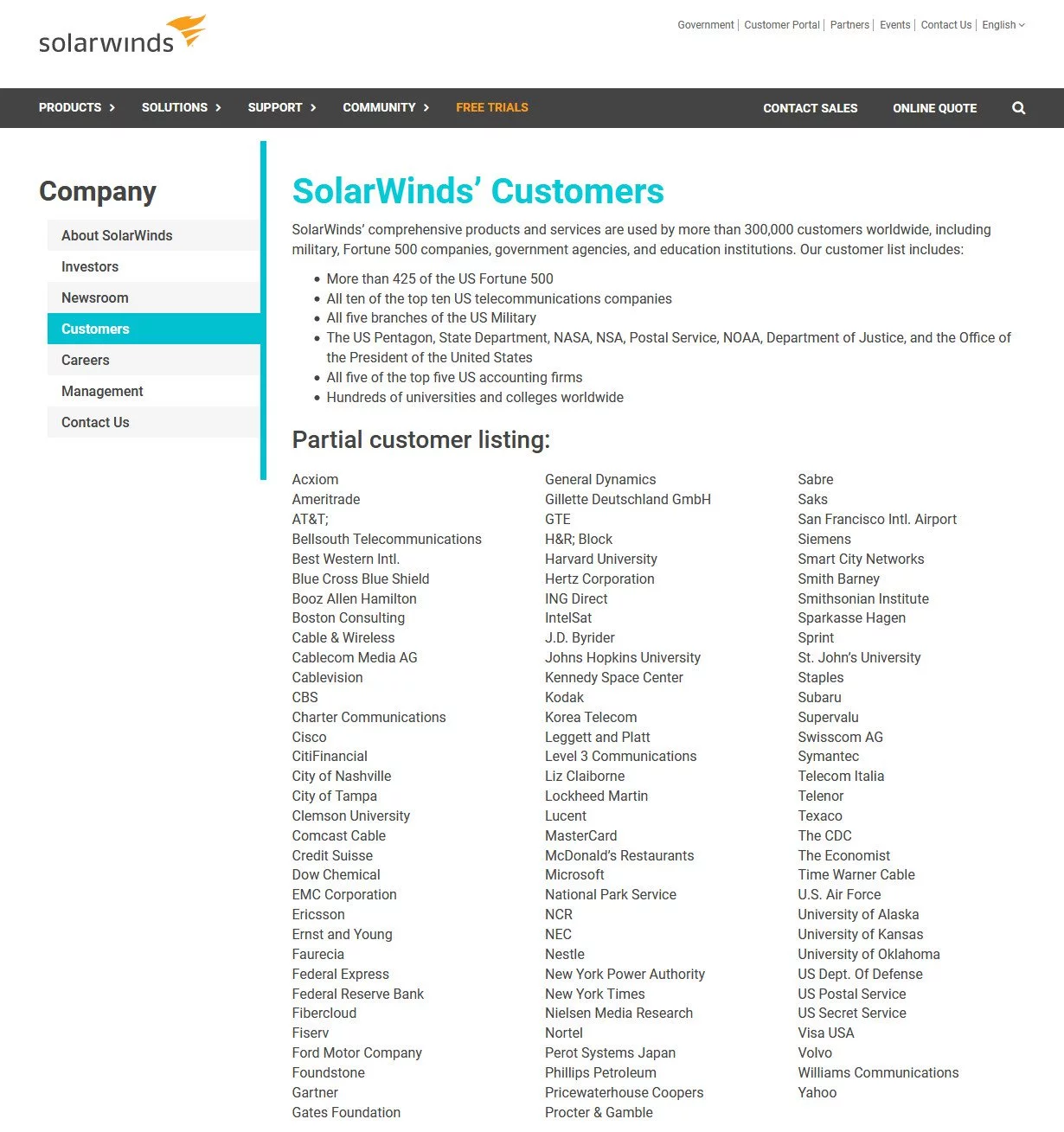
On its website, SolarWinds advertised a select customer base that included at least 425 organizations in the U.S. Fortune top 500; top ten telecommunications companies in the country; all branches of the U.S. Military; the Pentagon; NASA; NSA; the Postal Service, the Department of Justice; and the Office of the President of the United States.
The total number of victims remains unknown, but media reports mention eight organizations besides cybersecurity company FireEye that was the first to disclose the breach: the U.S. Treasury and Commerce departments, the Department of Homeland Security, the State Department, the National Institutes of Health, the Pentagon, and the National Institutes of Health [1, 2, 3, 4, 5].
It is unclear how many victims the hackers breached through the Orion supply-chain attack, but the number of entities that installed the poisoned version of the software is “fewer than 18,000,” the company said.
Media reports cite unofficial sources pinning the attack on APT29 (Cozy Bear) – the hacking division of Russia’s foreign intelligence service, the SVR.