KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The dark web websites associated with the Netwalker ransomware operation have been seized by law enforcement from the USA and Bulgaria.
Netwalker is a Ransomware-as-a-Service (RaaS) operation that began operating in late 2019, where affiliates are enlisted to distribute the ransomware and infect victims in return for a 60-75% share of ransom payments.
This ransomware operation proved to be very profitable for the threat actors, with an August report estimating that they generated $25 million in just five months.
Today, the Netwalker ransomware Tor payment and data leak sites were seized by law enforcement and now display a seizure notice from the FBI and Bulgarian law enforcement.
Also Read: 15 Best Tools For Your Windows 10 Privacy Settings Setup
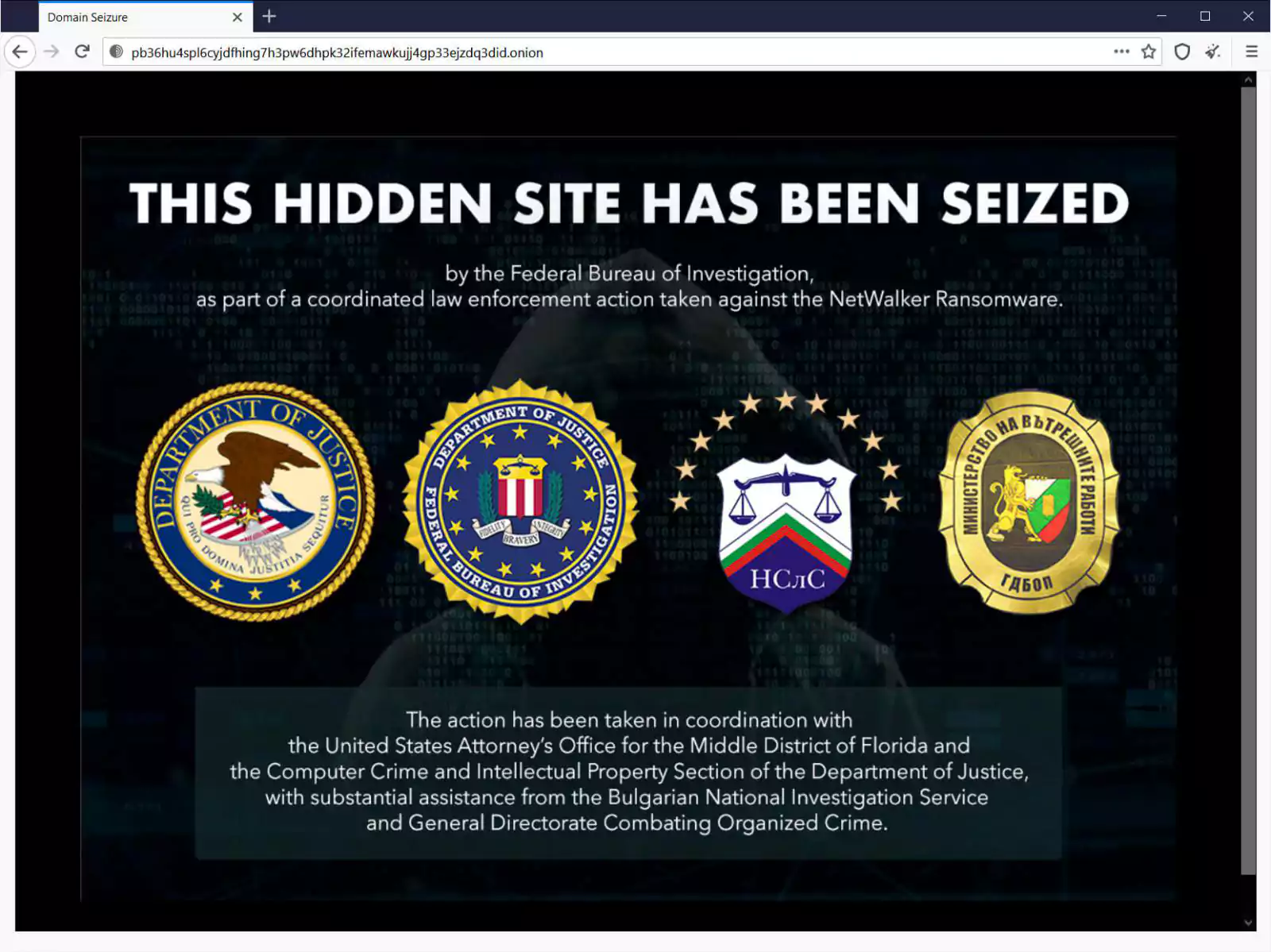
The seizure notice states that the takedown was conducted by the US DOJ, the FBI, Bulgarian National Investigation Service, and Bulgaria’s General Directorate Combating Organized Crime.
“This hidden site has been seized by the Federal Bureau of Investigation, as part of a coordinated law enforcement action taken against the NetWalker Ransomware.”
“The action has been taken in coordination with the United States Attorney’s Office for the Middle District of Florida and the Computer Crime and Intellectual Property Section of the Department of Justice, with substantial assistance from the Bulgarian National Investigation Service and General Directorate Combating Organized Crime,” the website seizure notice reads.
At this time, the FBI has not released any information on the takedown, so it is not clear if law enforcement was able to retrieve decryption keys as part of this operation or if arrests have been made.
With Netwalker being one of the most active ransomware families currently operating, access to decryption keys could allow many victims to recover their files for free.
The recovery of decryption keys would also be a massive win for law enforcement as ransomware operations have been remarkably resistant to disruption.
Also Read: How Formidable is Singapore Cybersecurity Masterplan 2020?
Some of the high-profile victims targeted by Netwalker include Equinix, Enel Group, the Argentian immigration agency, University of California San Francisco (UCSF), and K-Electric.
BleepingComputer has contacted the FBI with further questions.