KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





An ongoing phishing campaign is impersonating Michael Page consultants to push Ursnif data-stealing malware capable of harvesting credentials and sensitive data from infected computers.
Michael Page is a world-leading employment agency focused on recruiting at the qualified professional and management level for permanent, temporary, contract, or interim positions.
The agency is part of the British-based PageGroup recruitment business with operations in the Americas, UK, Continental Europe, Asia-Pacific, and Africa.
“We are continuing to experience a global phishing campaign where our employees are being impersonated,” Michael Page UK said.
“We are confident that no PageGroup system has been compromised,” the parent company added, confirming that the attackers haven’t breached the recruitment consultancy’s servers and are only spoofing employees in the phishing emails sent to random targets.
“These phishing emails are being generated from publicly available information not linked to our business and are being then sent on to random email recipients,” PageGroup revealed.
PageGroup urges those who have received one of these phishing emails or any email coming from Michael Page that looks suspicious “not to reply or click” on any of the embedded links.
Also Read: What Do 4 Messaging Apps Get From You? Read The iOS Privacy App Labels
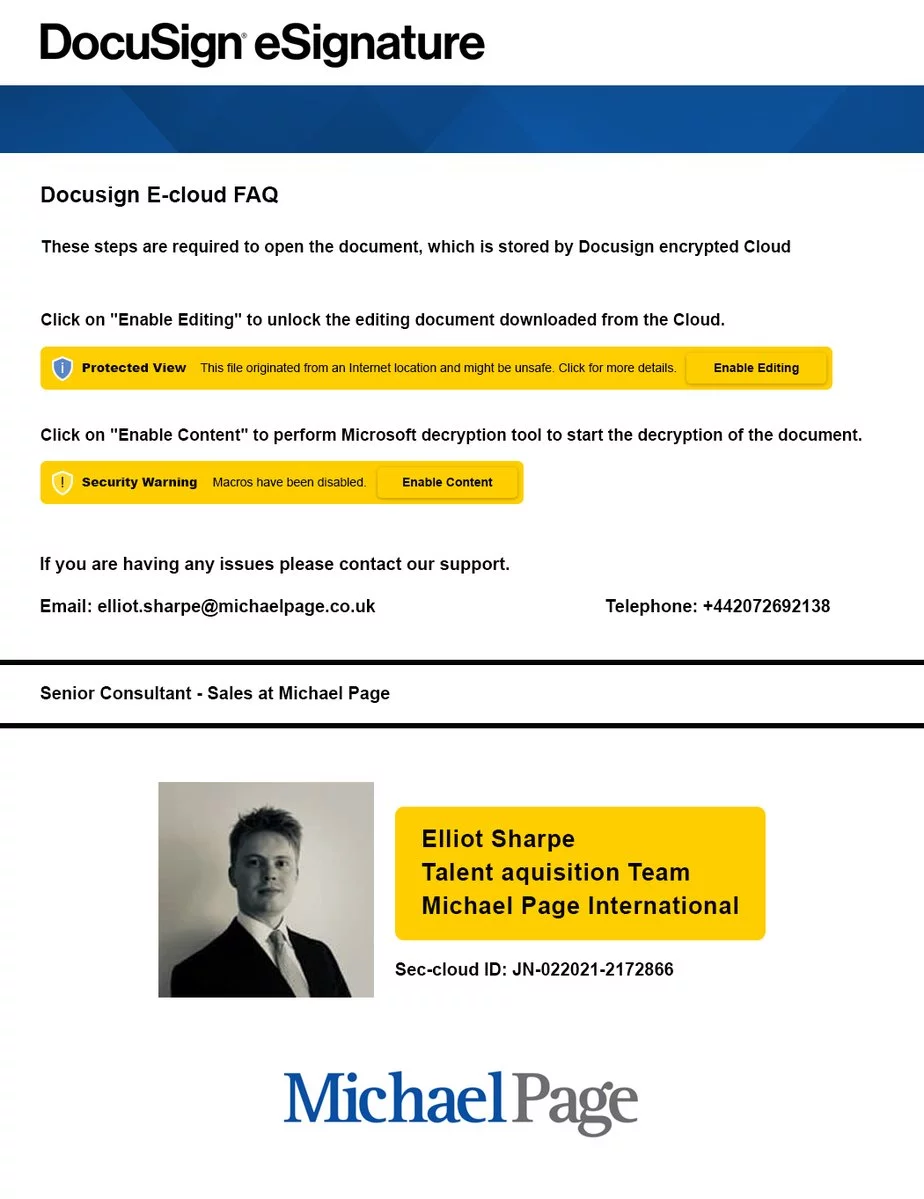
In phishing emails sent as part of this campaign seen by BleepingComputer, attackers posing as Michael Page UK headhunters are luring targets with executive positions.
These emails use embedded links to redirect potential victims to phishing landing pages featuring GeoIP and antibot checks, according to a security researcher known as TheAnalyst.
The victims are then asked to download archives containing malicious macro-enabled Microsoft Excel spreadsheets (XSLM) and featuring DocuSign branding, asking the targets to enable editing to decrypt and open the document.
Once the victims enable macros, they are shown a decoy document with information on a fake management position, while the Ursnif malware payload is downloaded and installed on their computer in the background.
Also Read: The 5 Benefits Of Outsourcing Data Protection Officer Service
Ursnif (also known as Gozi v2.0, Gozi ISFB, ISFB, and Pandemyia) is an information-stealing trojan and an offspring of the original Gozi banking trojan (Gozi CRM) whose source code accidentally leaked online in 2010.
Since then, malware developers have used the code to build other banking trojan strains, such as GozNym.
Once it infects a computer, Ursnif starts recording the victims’ keystrokes, the sites they visit, harvests clipboard content, and collects all this info into log files and sent back to its operators’ servers.
Using this stolen info, the attackers can steal their victims’ login credentials and other sensitive data to further compromise their accounts or networks.