KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






The PyPI repository has removed a Python package called ‘mitmproxy2’ that was an identical copy of the official “mitmproxy” library, but with an “artificially introduced” code execution vulnerability.
The official ‘mitmproxy’ Python library is a free and open-source interactive HTTPS proxy with over 40,000 weekly downloads.
Yesterday, Maximilian Hils, who is one of the developers behind the ‘mitmproxy’ Python library drew everyone’s attention towards a counterfeit ‘mitmproxy2’ package uploaded to PyPI.
‘mitmproxy2’ is essentially “the same as regular mitmproxy but with an artificial RCE vulnerability included.”
The more popular you get, the more shit you attract: Someone uploaded “mitmproxy2” to @PyPI, which is the same as regular mitmproxy but with an artificial RCE vulnerability included.— Maximilian Hils (@maximilianhils) October 11, 2021
Hils’ main concern, as he describes to BleepingComputer, was that some software developers might mistake ‘mitmproxy2’ as a newer version” of ‘mitmproxy’ and inadvertently introduce insecure code in their apps.
Also Read: How Does Ransomware Work? Examples and Defense Tips
Hils found this copycat package in what he calls a “happy little accident” while looking into an unrelated PyPI warehouse issue.
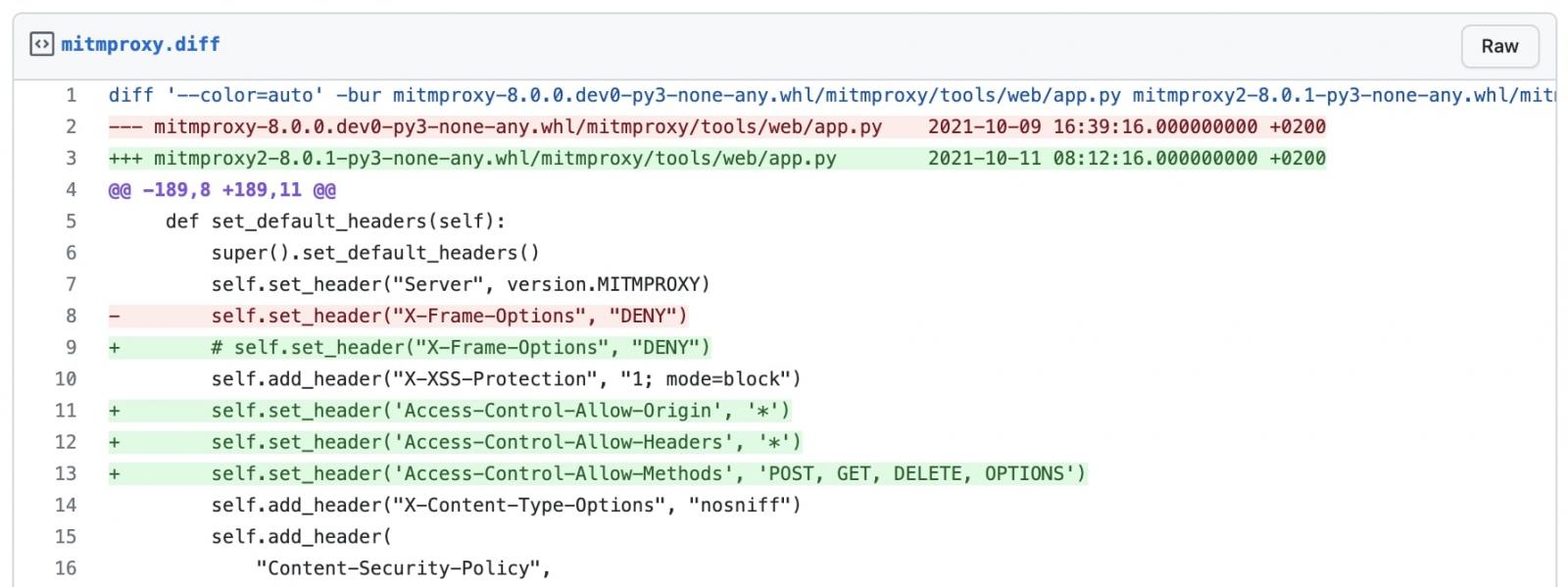
On analyzing the differences between ‘mitmproxy2’ and his ‘mitmproxy,’ something important stood out. The former had all safeguards removed from the API:
“When you run mitmproxy’s web interface, we expose an HTTP API for that. If you remove all safeguards from that API, everyone on the same network can execute code on your machine with a single HTTP request,” Hils told BleepingComputer in an email interview.
It isn’t clear either if the user who published the copycat ‘mitmproxy2’ package did so with willful malicious intent or just out of insecure coding practices.
“To be clear, this really isn’t the most malicious thing an attacker could do. It would be much more straightforward to just add some malicious code that gets executed on install right away.”
“The problem is of course if you upload that to PyPI as ‘mitmproxy2’ with a version number that indicates it’s newer/a successor, people will inevitably download that not knowing about the changes.”
Hils thanked PyPI volunteers for swiftly reacting to this report. Within four hours of Hils’ tweet ‘mitmproxy2’ was taken down.
Also Read: How to Choose a Penetration Testing Vendor
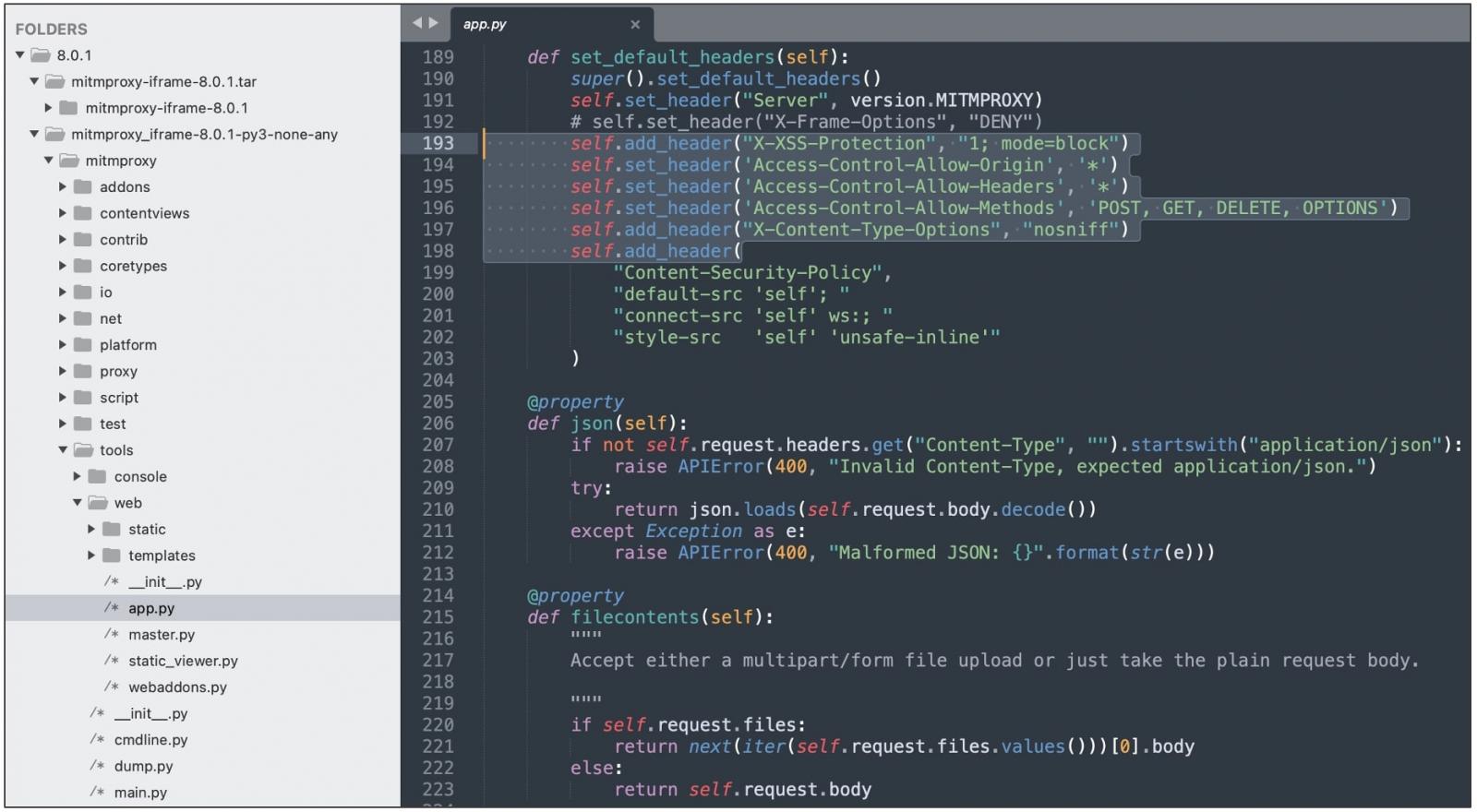
While analyzing ‘mitmproxy2’, BleepingComputer discovered another package ‘mitmproxy-iframe‘ had appeared on the PyPI registry, less than a day after ‘mitmproxy2’ was removed.
Once again, this package is an exact replica of the official mitmproxy, but with the aforementioned safeguards removed from the “app.py” file, as seen by BleepingComputer.
Interestingly, mitmproxy-iframe is also published by the same user who is behind ‘mitmproxy2’, now casting doubts on what the user’s intentions are:
Because anyone can publish packages to open-source ecosystems, security threats and attacks like malware injection, typosquatting, brandjacking, and dependency confusion have increased rapidly in recent times.
Unless concrete validations are put in place by open-source registries, these “whack-a-mole” situations are bound to repeat themselves.
BleepingComputer notified PyPI of the ‘mitmproxy-iframe’ package prior to publishing and the package was taken down.