KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Hacker crews are picking sides as the Russian invasion into Ukraine continues, issuing bans and threats for supporters of the opposite side.
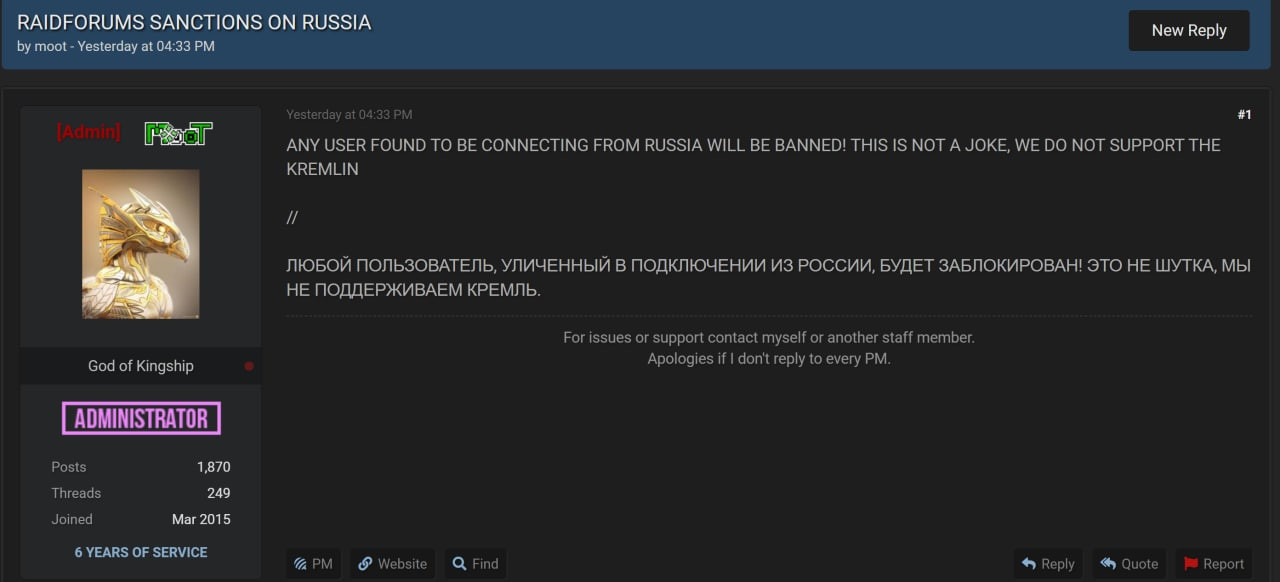
This week, an administrator of the database sharing and marketplace Raidforums announced that it would close its door on users connecting from Russia, clearly expressing their position against Kremlin’s actions.
Earlier today, the Conti ransomware group stated their “full support of Russian government” and threatened with cyberattacks against anyone launching attacks against Russia.
Also Read: Free 8 Steps Checklist for Companies to Prevent Data Breach
Hackers, state-backed or not, have already launched cyberattacks, most of them against Ukrainian targets [1, 2, 3], with some targets in Russia also being hit [1].
With the Russian aggression continuing, the hacker community started to get more involved and express their stance in the conflict.
Following the political model of the U.S. and the EU, Raidforums published a notification yesterday saying that it would impose its own sanctions by banning any user connecting from Russia.
One member of the Raidforums community published a more abrasive message as a warning to “Russians.” The user posted a database with emails and hashed passwords for the FSB.ru domain of Russia’s main security agency, the Federal Security Service (FSB).
In the sample data shared on the forum as proof of provenance there are email addresses for FSB offices (directorates) in various regions.
Also Read: Digital Transformation – Do Or Die in 2020
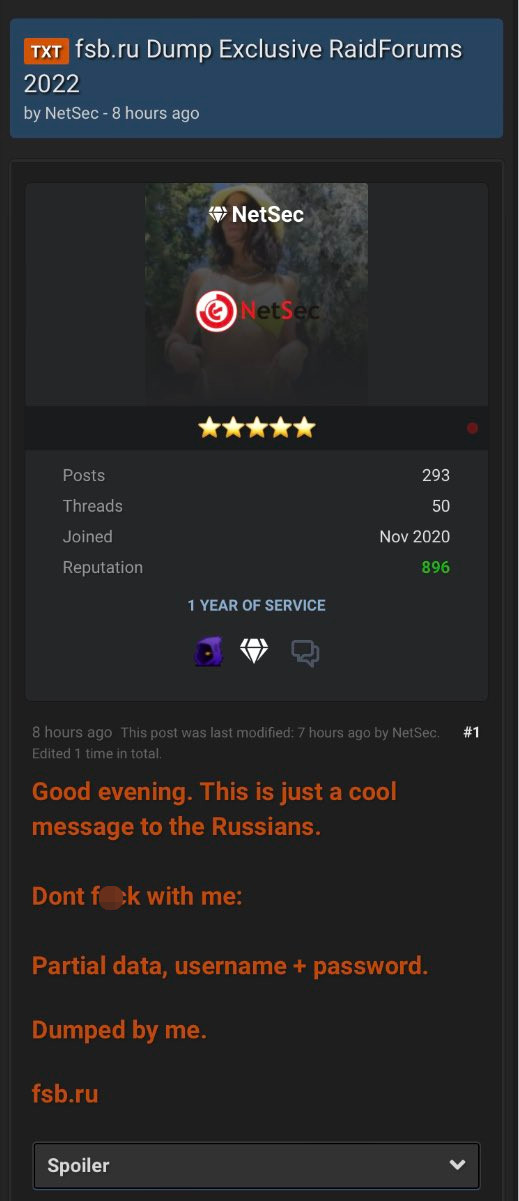
The same user has previously posted similar databases for .mil domains in the United States.
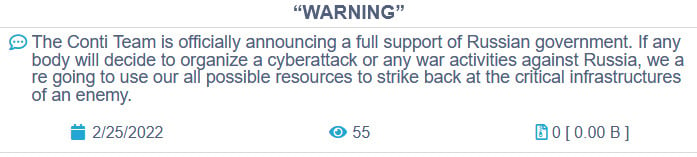
Today, the Conti ransomware gang issued a warning that they would respond to cyber activity against Russia using all their resources “to strike back at the critical infrastructures of an enemy.”
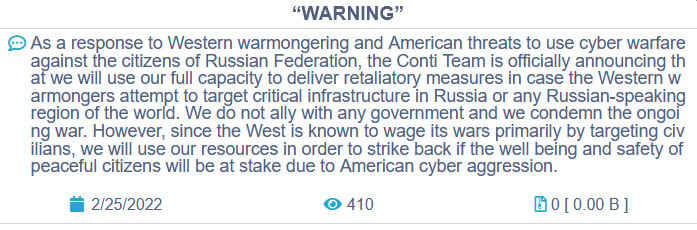
The gang changed their message about an hour later, saying that they “do not ally with any government and we condemn the ongoing war” but will respond to Western cyber aggression on Russian critical infrastructure.
Conti is one of the most active ransomware actors in the industrial sector, being responsible last year for breaching 63 companies operating industrial control systems (ICS), most of the in the manufacturing sector.
Conti also took control of BazarBackdoor, the stealthy malware developed by the TrickBot gang for compromising high-value targets.
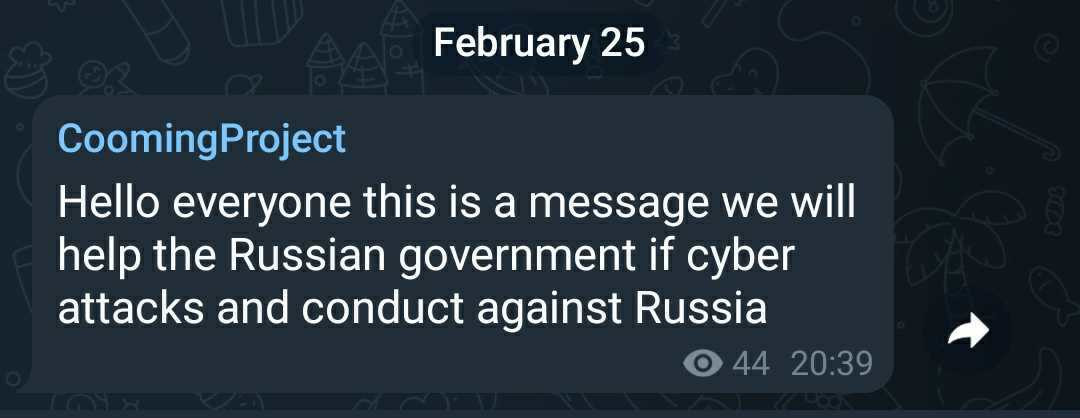
CoomingProject, another, less known, ransomware group also announced their support for the Russian government if cyberattacks are aimed at the country.
It appears that the Ukrainian side is also trying to engage its hacker force to defend critical infrastructure from coordinated cyberattacks and to carry out cyberespionage operations on Russian activity.
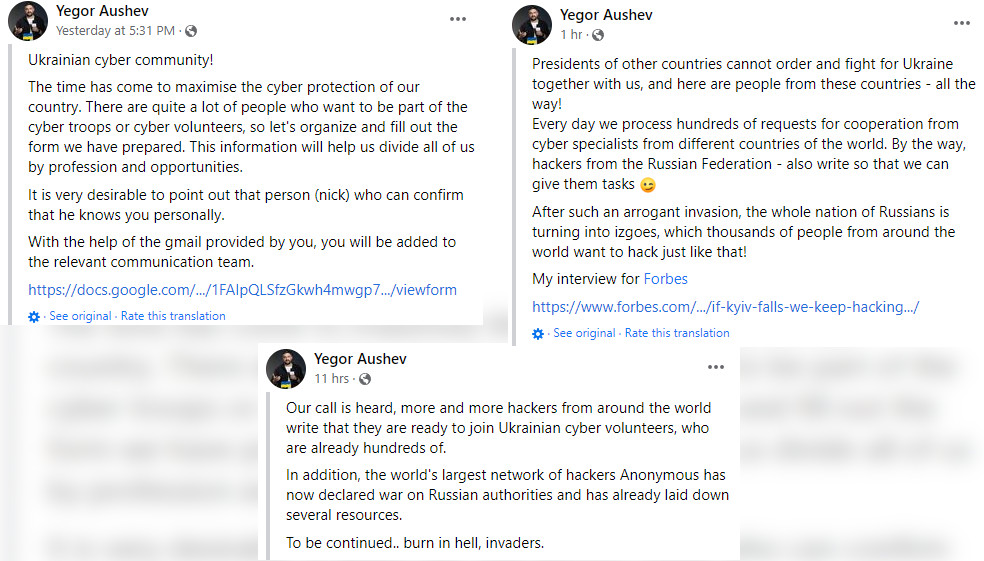
Reuters details that a message for the Ukrainian underground hacker community posted at the request of the Defense Ministry called the cybercommunity to enroll in a mission to defend the country.
The call to action was published through Yegor Aushev, the founder of Cyber Unit Technologies, who yesterday shared an application form for volunteer hackers to sign up declaring their skills for a better organization of tasks.
In one post, Aushev claims that even hackers around the world, including from Russia, have responded to his call, who will be grouped into teams for offensive and defensive action.
It is clear that modern warfare has entered a new age as physical armed forces are now openly supported by cyber activity carried not just by individuals with formal training but also self-taught hackers on both sides of the law.