KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Threat actors have revived an old and relatively inactive ransomware family known as TellYouThePass, deploying it in attacks against Windows and Linux devices targeting a critical remote code execution bug in the Apache Log4j library.
KnownSec 404 Team’s Heige first reported these attacks on Twitter on Monday after observing that the ransomware was dropped on old Windows systems using exploits abusing the flaw tracked as CVE-2021-44228 and known as Log4Shell.
Heige’s report was confirmed by the Sangfor Threat Intelligence Team, who successfully captured one of the TellYouThePass ransomware samples deployed in attacks using Log4Shell exploits mostly impacting Chinese targets, according to Curated Intelligence.
Also Read: Personal Data Protection Act Singapore: Is Your Business Compliant?
As they further discovered (findings that CronUP’s Germán Fernández also confirmed), the ransomware has a Linux version that harvests SSH keys and moves laterally throughout victims’ networks.
“It is worth noting that this is not the first time that Tellyouthepass ransomware has used high-risk vulnerabilities to launch attacks,” Sangfor researchers said. “As early as last year, it had used Eternal Blue vulnerabilities to attack multiple organizational units.”
Other security researchers [1, 2] have also analyzed one of the ransomware samples deployed in these attacks and tagged it as “likely belonging” to the TellYouThePass family.
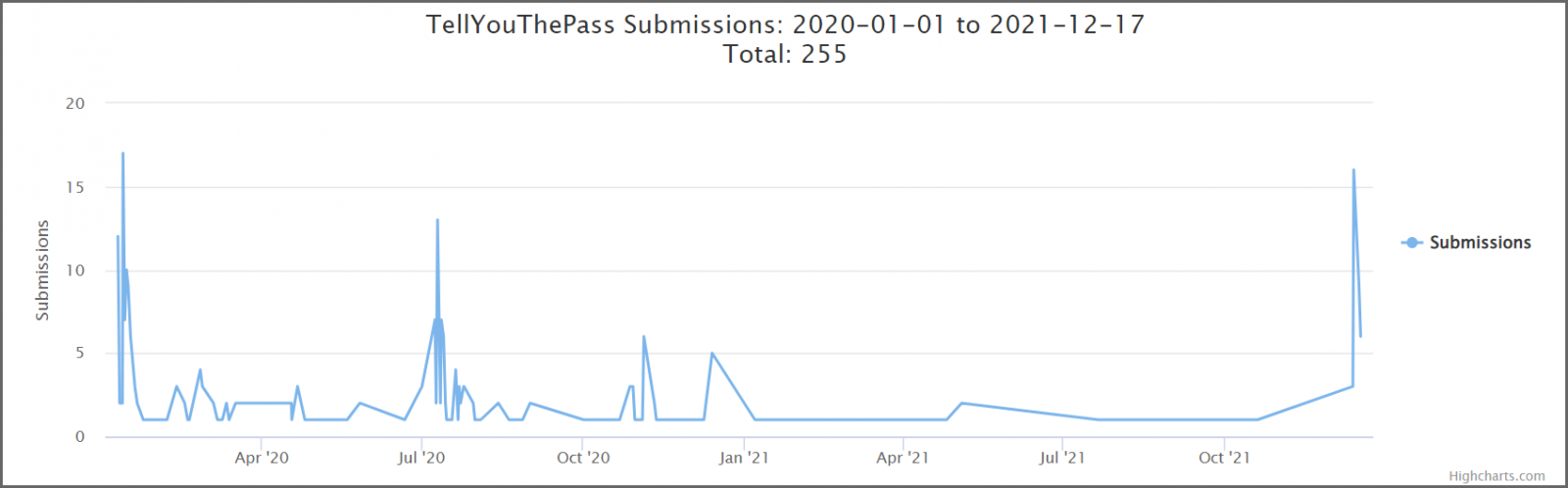
According to submission stats to the ID Ransomware service, TellYouThePass ransomware has seen a massive and sudden spike in activity after Log4Shell proof-of-concept exploits were released online.
TellYouThePass is not the first ransomware strain deployed in Log4Shell attacks since financially-motivated attackers began injecting Monero miners on compromised systems and state-backed hackers started exploiting it to create footholds for follow-on activity.
BitDefender first reported they found a new ransomware family (tagged by some as a wiper) they dubbed Khonsari being installed directly via Log4Shell exploits.
The Microsoft 365 Defender Threat Intelligence Team also saw Khonsari ransomware payloads dropped on self-hosted Minecraft servers.
Also Read: The Financial Cost of Ransomware Attack
Last but not least, Conti ransomware operators have also added a Log4Shell exploit to their arsenal to move laterally through targets’ networks, gain access to VMware vCenter Server instances, and encrypt virtual machines.
In related news, CISA ordered Federal Civilian Executive Branch agencies today to patch their systems against the Log4Shell vulnerability within the next six days, until December 23.
The cybersecurity agency has also recently added the flaw to its Known Exploited Vulnerabilities Catalog, which also requires expedited action from federal agencies to mitigate the bug until December 24.