KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






The U.K. National Cyber Security Centre (NCSC) today issued an alert highlighting the risks behind the recently addressed CVE2020-16952 remote code execution (RCE) vulnerability in Microsoft SharePoint Server.
NCSC, the cybersecurity arm of the UK’s GCHQ intelligence service, urges organizations to make sure that all Microsoft SharePoint products in their environments are patched against CVE-2020-16952 to block takeover attempts.
“The NCSC strongly advises that organisations refer to the Microsoft guidance referenced in this alert and ensure the necessary updates are installed in affected SharePoint products,” the alert says.
The server-side include (SSI) vulnerability was reported by information security specialist Steven Seeley of Qihoo 360 Vulcan Team who found that it affects Microsoft SharePoint Enterprise Server 2016, Microsoft SharePoint Foundation 2013 Service Pack 1, and Microsoft SharePoint Server 2019.
Also Read: How Bank Disclosure Of Customer Information Work For Security
Seeley also provides a proof-of-concept exploit designed to demonstrate how the vulnerability can be used to execute arbitrary code remotely.
CVE-2020-16952 makes it possible for attackers to remotely execute code following successful exploitation in the context of the local Administrator.
Authentication is also required to exploit the vulnerability, with the authenticated attacker needing page creation privileges (a default SharePoint permission) — more info on the inner workings of CVE-2020-16952 provided by cyber-security firm Rapid7 can be found here.
“CVE-2020-16952 poses higher risk for multi-tenant environments — i.e., multiple organizations using the same SharePoint and/or Active Directory environment,” according to Rapid7 researchers.
To defend against attacks designed to exploit this vulnerability, IT admins are advised to apply the October 2020 SharePoint security updates.
Details on how to secure vulnerable Microsoft SharePoint instances can be found in KB4486676 for SharePoint 2019, in KB4486677 for SharePoint 2016, and in the KB4486694 advisory for SharePoint 2013.
While there are no reports of this vulnerability being leveraged in the wild yet, the risk of this happening is high given that a proof-of-concept exploit is already available.
Also Read: Data Protection Framework: Practical Guidance For Businesses
An exploit module is also being developed for the open-source Metasploit penetration testing framework and already successfully tested with SharePoint 2019 on Windows Server 2016.
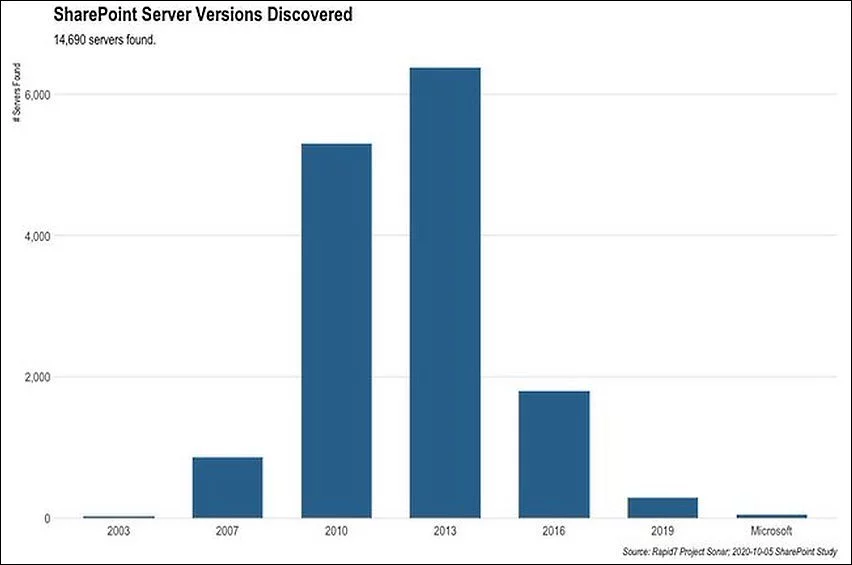
After Microsoft issued CVE-2020-16952 security updates for all supported SharePoint products (SharePoint 2013, 2016, and 2019) as part of the October 2020 Patch Tuesday, Rapid7 used data collected until October 5 and discovered roughly 15,000 SharePoint services on 443/tcp reachable services.
Most of these Internet-exposed SharePoint instances were found to run SharePoint 2010 and 2013, with around ~5,300 SharePoint 2010 servers and ~6,400 SharePoint 2013 servers.
Given that SharePoint servers are used in enterprise environments they are also an extremely attractive target for threat actors seeking to find and attack high-value targets.
The NCSC says that it “has previously seen a large number of exploitations of SharePoint vulnerabilities, such as CVE-2019-0604, against UK organizations.”
Together with CVE-2015-1641, the two vulnerabilities are present on the list of most exploited vulnerabilities since 2016 shared in a joint advisory by the US Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI).
They are both being used to drop malware such as China Chopper, Toshliph, and UWarrior on the enterprise networks running SharePoint services left unpatched for years on end.
Earlier this week, US Cyber Command also warned Microsoft customers to immediately patch their systems against the CVE-2020-16898 remote code execution bug, also known as ‘Bad Neighbor’, found in the Windows TCP/IP stack.