KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Cruise line operator Carnival Corporation has disclosed that one of their brands suffered a ransomware attack over the past weekend.
Carnival Corporation is the largest cruise operator in the world with over 150,000 employees and 13 million guests annually. The cruise line operates under the brands Carnival Cruise Line, Costa, P&O Australia, P&O Cruises, Princess Cruises, Holland American Line, AIDA, Cunard, and their ultra-luxury cruise line Seabourn.
In an 8-K form filed with the Securities and Exchange Commission (SEC), Carnival Corporation has disclosed that one of its brands suffered a ransomware attack on August 15th, 2020.
“On August 15, 2020, Carnival Corporation and Carnival plc (together, the “Company,” “we,” “us,” or “our”) detected a ransomware attack that accessed and encrypted a portion of one brand’s information technology systems. The unauthorized access also included the download of certain of our data files,” the cruise line operator stated in their filing.
As part of the attack, Carnival states data was likely stolen and could lead to claims from those affected by the potential data breach.
“Nonetheless, we expect that the security event included unauthorized access to personal data of guests and employees, which may result in potential claims from guests, employees, shareholders, or regulatory agencies,”
The filing does not indicate the ransomware operation that compromised their network, and there are close to twenty different gangs that steal and leak unencrypted files as part of their attacks.
This ransomware attack comes on the heels of a data breach announced in March 2020 that led to the exposure of customers’ personal information, including possible payment information.
BleepingComputer contacted Carnival with further questions about the attack, but they are not providing any additional information.
“We are not planning to discuss anything beyond the 8K filing at this point since it is early in the investigation process,” Carnival told BleepingComputer.
Do you have first-hand information about this attack or another ransomware attack? If you have information to share, contact us securely on Signal at +1 (646) 961-3731, via email at [email protected], or using our tips form.
Also read: Top 25 Data Protection Statistics That You Must Be Informed
According to cybersecurity intelligence firm Bad Packets, Carnival utilizes vulnerable edge gateway devices that allow an attacker to gain access to a corporate network.
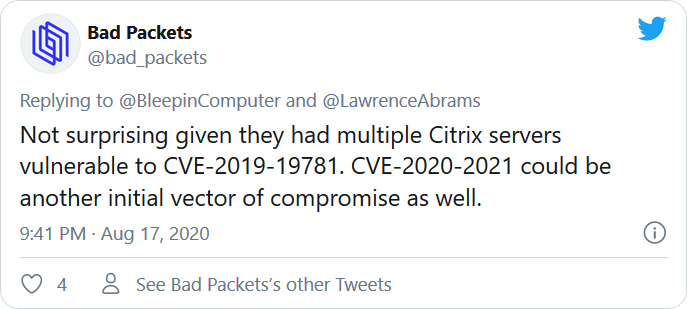
The CVE-2019-19781 vulnerability is for Citrix ADC (NetScaler) devices that, when exploited, allow a hacker to gain access to the company’s internal network. Patches for this vulnerability were released in January 2020.
The other vulnerability, CVE-2020-2021, exists in Palo Alto Networks firewalls and allows unauthenticated network-based attackers to bypass authentication. This vulnerability was patched at the end of June 2020.
Either of these vulnerabilities can be abused by ransomware operators to gain access to a corporate network silently. Once the attackers gain access, they spread laterally to other computers and harvest network credentials.
When they gain control over an administrator account and the Windows domain controller, the attackers deploy the ransom
While it is not known if either of these vulnerabilities were used in Carnival’s attack, they are commonly abused by ransomware operators in these types of attacks.
Update 8/17/2020 18:15: Updated to include information about vulnerable devices.
Also read: Completed DPIA Example: 7 Simple Helpful Steps To Create