KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Argentinian e-commerce giant Mercado Libre has confirmed “unauthorized access” to a part of its source code this week.
Mercado additionally says data of around 300,000 of its users was accessed by threat actors.
The company’s announcement follows a poll by the data extortion group, Lapsus$ in which they threatened to leak data allegedly stolen from Mercado and other prominent companies.
In a press release and a Form 8-K filing seen by BleepingComputer today, MercadoLibre confirmed that a part of its source code had been subject to unauthorized access.
Also Read: What is Pentest Report? Here’s A Walk-through
Additionally, data of MercadoLibre’s 300,000 users was accessed according to its initial analysis. At this time, it does not appear that Mercado’s IT infrastructure was affected or that sensitive information has been compromised.
It is not clear at this time if the information of these 300,000 Mercado users was stored in one of the source code repos—a practice BleepingComputer has come across before when reporting on some data breach cases.
The company says it has activated security protocols and a thorough analysis is in progress.
“We have not found any evidence that our infrastructure systems have been compromised or that any users’ passwords, account balances, investments, financial information, or credit card information were obtained. We are taking strict measures to prevent further incidents,” says Mercado.
Headquartered in Buenos Aires, MercadoLibre makes up Latin America’s largest e-commerce and payments ecosystem.
The company boasts a user base of around 140 million unique active users and is present across eighteen countries including Argentina, Brazil, Mexico, Colombia, Chile, Venezuela, and Peru.
The American arm of the company, Mercado Libre, Inc. operates online marketplaces including mercadolibre.com.
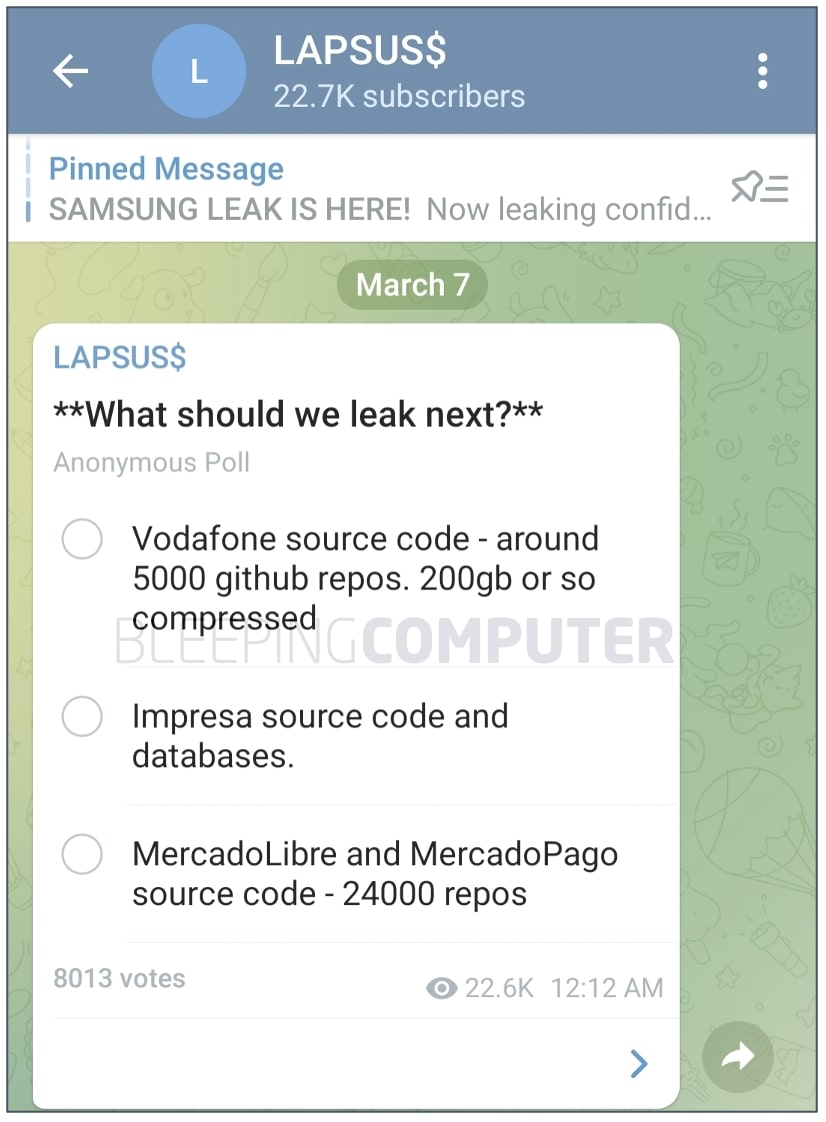
Data extortion group Lapsus$ claims to have accessed 24,000 source code repositories of both MercadoLibre and Mercado Pago, as seen by BleepingComputer.
A Telegram channel run by Lapsus$ published a poll on March 7th, mockingly asking users to vote for the company whose data Lapsus$ should leak next.
Also Read: The PDPA Data Breach August 2020: A Recap of 8 Alarming Cases
The list of alleged victims also includes Impresa and Vodafone. Lapsus$ states the poll will close on March 13th, 2022 at 00:00.
The development resembles Lapsus$’s last week’s leak of 190 GB-large archives that the group claimed contained “confidential Samsung source code.” The same week, Samsung confirmed that threat actors had indeed breached its network and stolen confidential information, including source code present in Galaxy smartphones.
Extortion groups like Lapsus$ breach victims but as opposed to encrypting confidential files like a ransomware operator would, these actors steal and hold on to victims’ proprietary data, and publish it should their extortion demands be not met.
Earlier this month, Lapsus$ claimed responsibility for a data breach at the American chipmaker giant, NVIDIA. The breach resulted in the theft of more than 71,000 NVIDIA employee credentials, with some credentials leaked online.