KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Popular musical instrument marketplace Reverb has suffered a data breach after an unsecured database containing customer information was exposed online.
Reverb is the largest online marketplace devoted to selling new, used, and vintage musical instruments and equipment.
Today, Reverb customers began receiving data breach notifications stating that customer information was exposed, including customers’ names, addresses, phone numbers, and email addresses.
Also Read: PDPA Singapore Guidelines: 16 Key Concepts For Your Business
While Reverb’s notification does not explain how they exposed the data, security researcher Bob Diachenko sheds some light on what happened.
Diachenko says he discovered an unsecured Elasticsearch server publicly exposed on the Internet that contained more than 5.6 million records.
Each record contained information about a particular listing on Reverb.com, including the full name, email address, phone number, mailing address, PayPal email, and listing/order information.
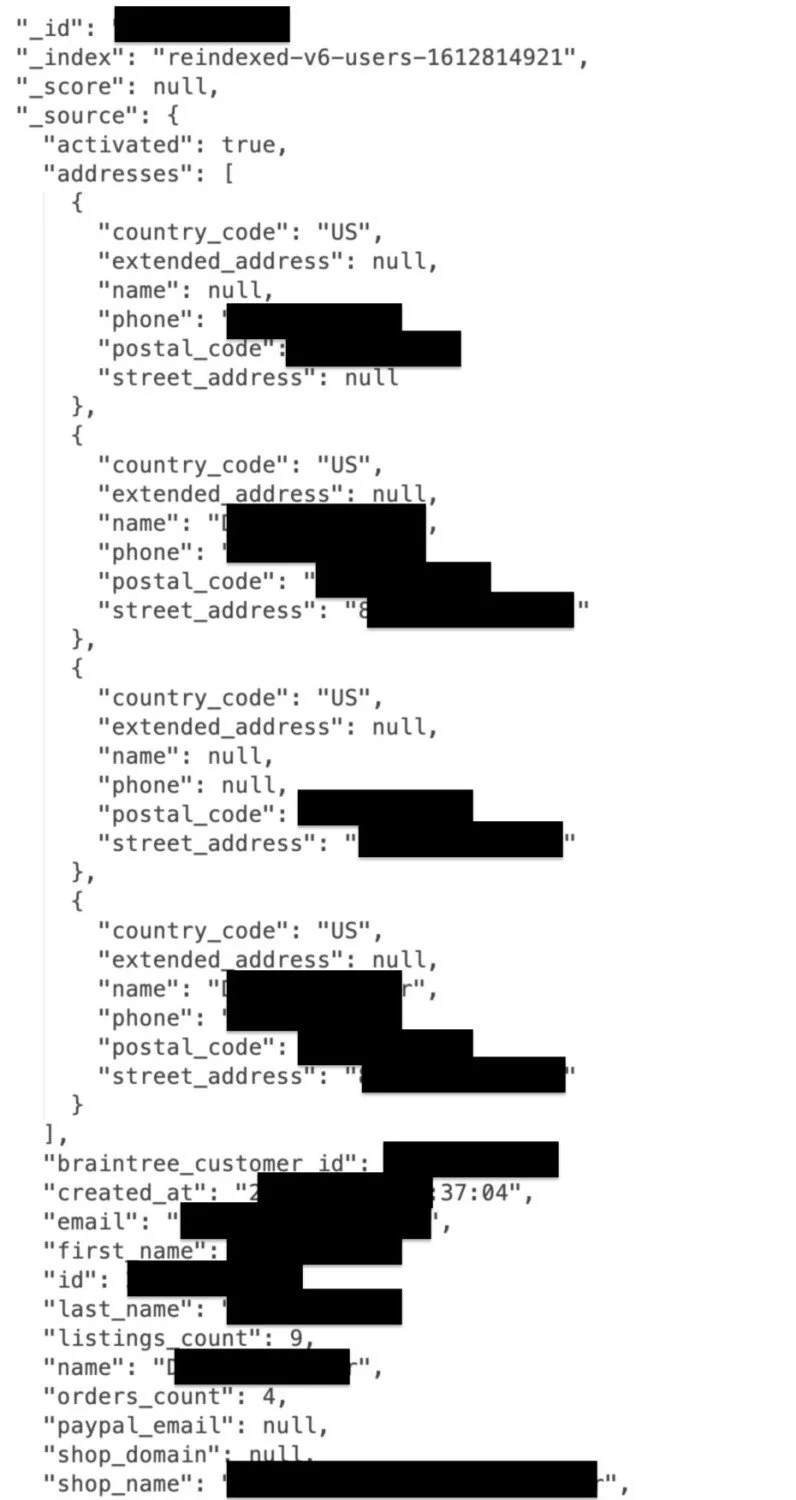
When Diachenko finds an unsecured database, he always notifies the company to secure the database. After analyzing the data, he noticed many users with @reverb.com email addresses and matched orders in the database with those on the site.
“To confirm my thought, I ran a quick check and was able to find several high-profiled sellers details, including Bill Ward of Black Sabbath, Jimmy Chamberlin of the Smashing Pumpkins, Alessandro Cortini of Nine Inch Nails and more,” explained a report by Diachenko.
Diachenko told BleepingComputer that by the time he confirmed the database belonged to Reverb, the site had already secured the database.
Also Read: Data Protection Officer Singapore | 10 FAQs
While the database was likely unsecured for only a short period, if a security researcher could find the database, so could a threat actor.
With this in mind, it is safer to assume that your data was exposed and be on the lookout for possible phishing emails using this information.
As your passwords were not exposed in this breach, Reverb is not resetting them. However, Reverb recommends users routinely reset their passwords for better security.