KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Microsoft says a threat actor gained access to cloud tenants hosting Microsoft Exchange servers in credential stuffing attacks, with the end goal of deploying malicious OAuth applications and sending phishing emails.
“The investigation revealed that the threat actor launched credential stuffing attacks against high-risk accounts that didn’t have multi-factor authentication (MFA) enabled and leveraged the unsecured administrator accounts to gain initial access,” the Microsoft 365 Defender Research Team revealed.
“The unauthorized access to the cloud tenant enabled the actor to create a malicious OAuth application that added a malicious inbound connector in the email server.”
Also Read: July 2022 PDPC incidents and undertaking
The attacker then used this inbound connector and transport rules designed to help evade detection to deliver phishing emails through the compromised Exchange servers.
The threat actors deleted the malicious inbound connector and all the transport rules between spam campaigns as an additional defense evasion measure.
In contrast, the OAuth application remained dormant for months between attacks until it was used again to add new connectors and rules before the next wave of attacks.
These email campaigns were triggered from Amazon SES and Mail Chimp email infrastructure commonly used to send marketing emails in bulk.
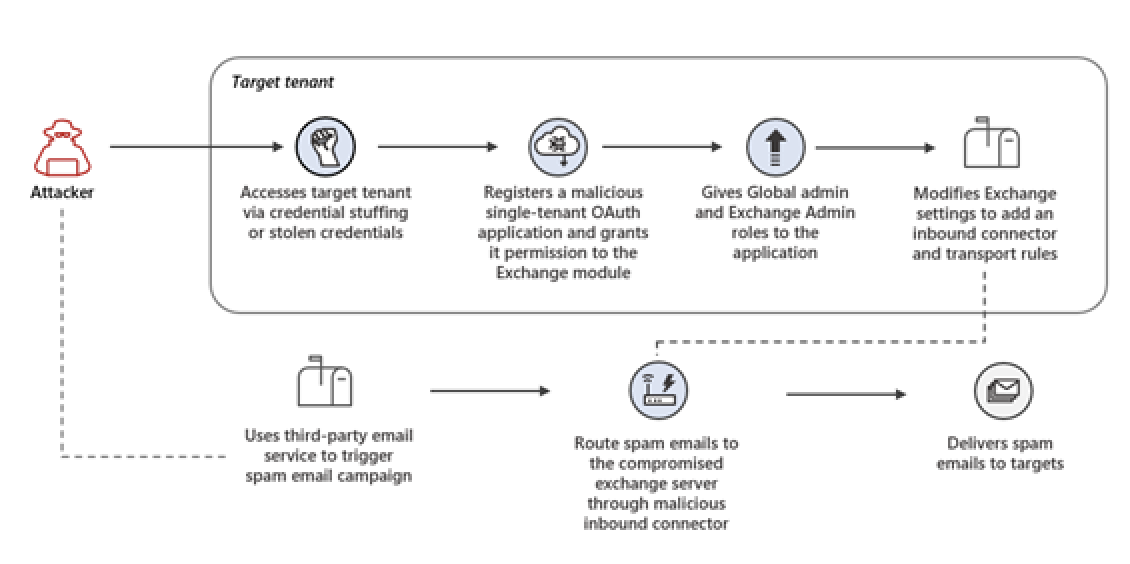
The attacker used a network of single-tenant applications as an identity platform throughout the attack.
Also Read: Penetration testing vs vulnerability assessment: which one do you need?
After detecting the attack, Redmond took down all apps linked to this network, sent alerts, and recommended remediation measures to all affected customers.
Microsoft says this threat actor was linked to campaigns pushing phishing emails for many years.
The attacker was also seen sending high volumes of spam emails within short timeframes through other means “such as connecting to mail servers from rogue IP addresses or sending directly from legitimate cloud-based bulk email sending infrastructure.”
“The actor’s motive was to propagate deceptive sweepstakes spam emails designed to trick recipients into providing credit card details and signing up for recurring subscriptions under the guise of winning a valuable prize,” Microsoft further revealed.
“While the scheme possibly led to unwanted charges for targets, there was no evidence of overt security threats such as credential phishing or malware distribution.”