KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Microsoft is rolling out a fix for a known issue that caused MS Access runtime applications not to open after installing July 2022’s Patch Tuesday Office/Access security updates.
Based on user complaints on Microsoft’s official community website and Reddit, the KB5002112 and KB5002121 updates are the ones triggering this issue for MS Access 2016 and MS Access 2013, respectively.
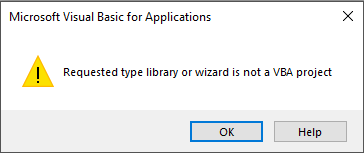
Microsoft says that for Office installation affected by this issue, users may receive a “Requested type library or wizard is not a VBA project” when opening an ACCDE/MDE file or a “Can’t complete the output operation” error when attempting to export to text or Excel files.
“This issue was introduced in the July 12 Patch Tuesday update across all supported versions of Access,” the company further explained.
Also Read: January 2022 PDPC Incidents and Undertaking
In an update to the initial advisory, Redmond says a fix is already available for customers using retail versions of Office 2016, 2019, and 2021, and for Microsoft 365 Apps Current Channel.
The fix is also rolling out to all other affected Access versions, with estimated arrival times between July 25 and August 9.
“For Click-to-run versions (all channels except Office 2013 and Office 2016 MSI), you can get the new update when it is available by choosing File/Account/Office Updates/Update Now,” Microsoft added.
“If you have Access to the original database that was used to create the ACCDE/MDE, and users are on a single version of Office, you can re-create the ACCDE/MDE file using the same version of Office that users are on.”
| Office Product | Issue Introduced | Fix available |
|---|---|---|
| Office 2016 Retail | Version 2206, Build 15330.20246 | Version 2206, Build 15330.20264 |
| Office 2019 Retail | Version 2206, Build 15330.20246 | Version 2206, Build 15330.20264 |
| Office 2021 Retail | Version 2206, Build 15330.20246 | Version 2206, Build 15330.20264 |
| Microsoft 365 Apps Current Channel | Version 2206, Build 15330.20246 | Version 2206, Build 15330.20264 |
Access users who cannot re-create their ACCDE/MDE files to mitigate the issue and don’t want to wait until the fix rollouts to their systems can remove the offending updates to resolve the problems.
Also Read: Vulnerability assessment Singapore: The complete checklist
However, it’s important to note that uninstalling this month’s cumulative updates will also remove security updates addressing a Microsoft Office security feature bypass vulnerability (CVE-2022-33632) addressed as part of the July 2022 Patch Tuesday.
This is because of Microsoft’s choice to bundle all security fixes within a single package. Removing Patch Tuesday updates will also remove fixes for any patched security flaws.
Therefore, uninstalling the buggy updates to address this MS Access issue should be the last resort option and only be done if absolutely necessary.
If you uninstall the July updates, you should also ensure that they won’t be reinstalled to trigger the Access launch problems again.
You will have to download and run the “Show or hide updates” troubleshooter from here, click on ‘Next,’ select the update you want to hide, and restart your computer when prompted.