KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







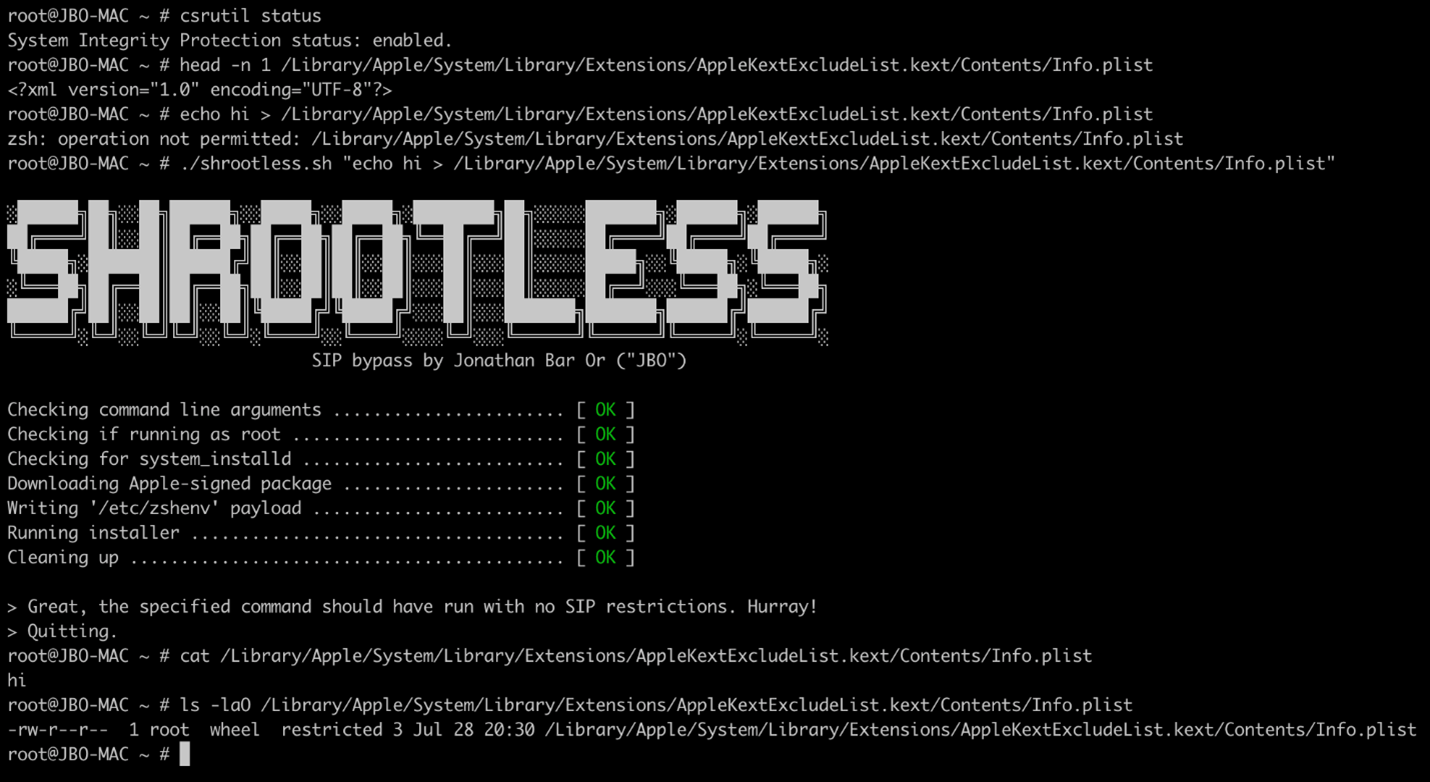
Attackers could use a new macOS vulnerability discovered by Microsoft to bypass System Integrity Protection (SIP) and perform arbitrary operations, elevate privileges to root, and install rootkits on vulnerable devices.
The Microsoft 365 Defender Research Team reported the vulnerability dubbed Shrootless (now tracked as CVE-2021-30892) to Apple by via the Microsoft Security Vulnerability Research (MSVR).
SIP (also known as rootless) is a macOS security technology that blocks potentially malicious software from modifying protected folders and files by restricting the root user account and limiting the actions it can perform on protected parts of the OS.
Also Read: Vulnerability Management For Cybersecurity Dummies
By design, SIP only allows processes signed by Apple or those with special entitlements (i.e., Apple software updates and Apple installers) to modify these protected parts of macOS.
The Shrootless security issue was discovered by Microsoft’s researchers after noticing that the system_installd daemon had the com.apple.rootless.install.inheritable entitlement which allowed any child process to fully bypass SIP filesystem restrictions.
“We found that the vulnerability lies in how Apple-signed packages with post-install scripts are installed. A malicious actor could create a specially crafted file that would hijack the installation process,” explained Jonathan Bar Or, a principal security researcher at Microsoft.
“After bypassing SIP’s restrictions, the attacker could then install a malicious kernel driver (rootkit), overwrite system files, or install persistent, undetectable malware, among others.”
Apple issued a fix to address the security flaw with the security updates released two days ago, on October 26.
“A malicious application may be able to modify protected parts of the file system,” Apple said in the security advisory.
Apple addressed the inherited permissions issue behind the Shrootless bug was with additional restrictions.
“We want to thank the Apple product security team for their professionalism and responsiveness in fixing the issue,” Jonathan Bar Or added.
Also Read: Compliance With Singapore Privacy Obligations; Made Easier!
Last week, Microsoft also reported finding new variants of macOS WizardUpdate malware (also tracked as UpdateAgent or Vigram), updated to use new evasion and persistence tactics.
This trojan deploys second-stage malware payloads, including Adload, a malware strain active since late 2017 and known for being able to slip through Apple’s YARA signature-based XProtect built-in antivirus to infect Macs.
In June, Redmond’s security researchers also discovered critical firmware vulnerabilities in some NETGEAR router models that attackers could use to breach and move laterally within enterprise networks.