KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Microsoft announced today that it resumed the rollout of VBA macro auto-blocking in downloaded Office documents after temporarily rolling it back earlier this month following user feedback.
The change comes after the company improved its user and admin support documentation to make it easier to understand the available options when a macro is blocked.
“Based on our review of customer feedback, we’ve made updates to both our end user and our admin documentation to make clearer what options you have for different scenarios,” Microsoft explained in a new update in the Microsoft 365 message center.
“For example, what to do if your users have files on SharePoint or files on a network share.”
Also Read: February 2022 PDPC Incidents and Undertaking
End users can find more information on the next steps after macros are blocked in a downloaded Office document on the A potentially dangerous macro has been blocked support page. IT admins can find dedicated documentation on the Macros from the Internet will be blocked by default in Office page.
“If you ever enabled or disabled the Block macros from running in Office files from the Internet policy, your organization will not be affected by this change,” Microsoft added.
Microsoft Office users who want automatic Office macro auto-blocking enabled and don’t want to wait for the rollout to reach their systems can read our easy-to-follow tutorial on how to auto-block macros in Microsoft Office docs from the Internet using group policies.
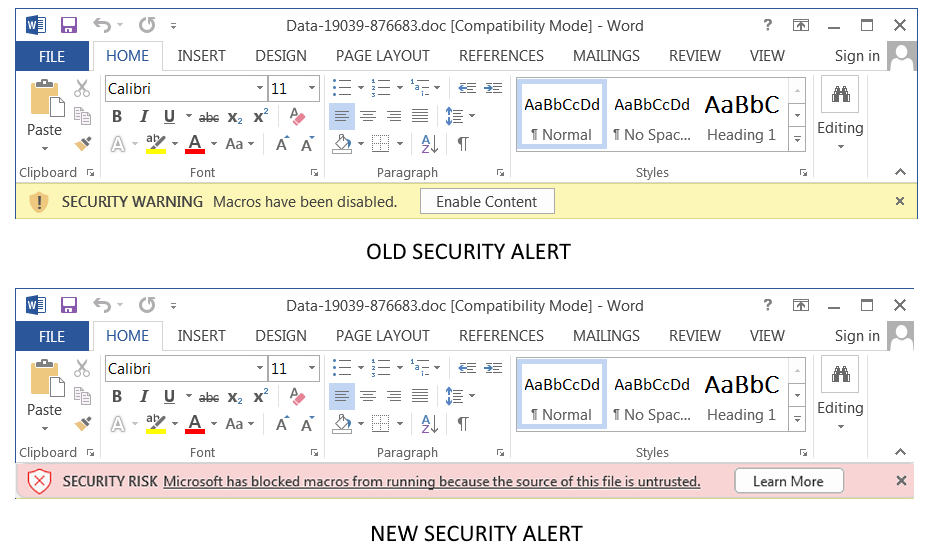
This announcement comes after Redmond backtracked on a decision made earlier this year to make it harder to enable Office VBA macros in docs downloaded from the Internet in several Microsoft Office apps (Access, Excel, PowerPoint, Visio, and Word) for customers in the Current Channel (Preview).
The new feature meant that a popular distribution method for malware would effectively be killed since VBA macros embedded in malicious Office documents have been, for a very long time, one of the easiest methods for threat actors to push various malware families in phishing attacks.
Also Read: PDPA compliance and progressive HR practices: Why this tandem makes sense
The company announced in February 2022 that Microsoft Office would automatically block VBA macros in all downloaded documents after a rollout stage between April and June.
However, as BleepingComputer first reported in early July, soon after the new feature went live for customers last month, Microsoft suddenly and without any real explanation said that this change would be rolled back.
While Microsoft revealed alerted admins in an M365 message center update, it didn’t make a public announcement and updated the original notification several days later to say it was just a temporary rollback.
Redmond pinned this rollback on negative user feedback. Although Microsoft didn’t share more info, users have reported they didn’t know how to re-enable macros after they were automatically blocked because they couldn’t find the Unblock button. In contrast, others found it burdensome to unblock each downloaded Office document multiple times daily.