KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







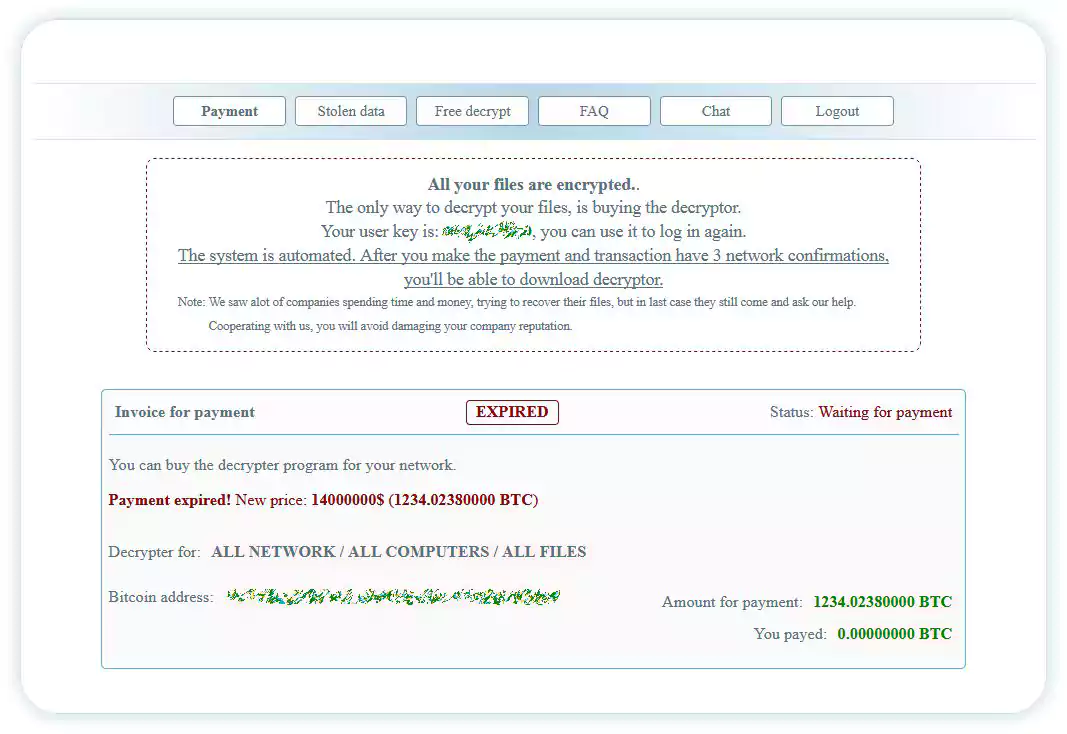
Multinational energy company Enel Group has been hit by a ransomware attack for the second time this year. This time by Netwalker, who is asking a $14 million ransom for the decryption key and to not release several terabytes of stolen data.
Enel is one of the largest players in the European energy sector, with more than 61 million customers in 40 countries. As of August 10, it ranks 87 in Fortune Global 500, with a revenue of almost $90 billion in 2019.
In early June, Enel’s internal network was attacked by Snake ransomware, also referred to as EKANS, but the attempt was caught before the malware could spread.
On Octber 19th, a researcher shared a Netwalker ransom note with BleepingComputer that appeared to be from an attack on Enel Group.
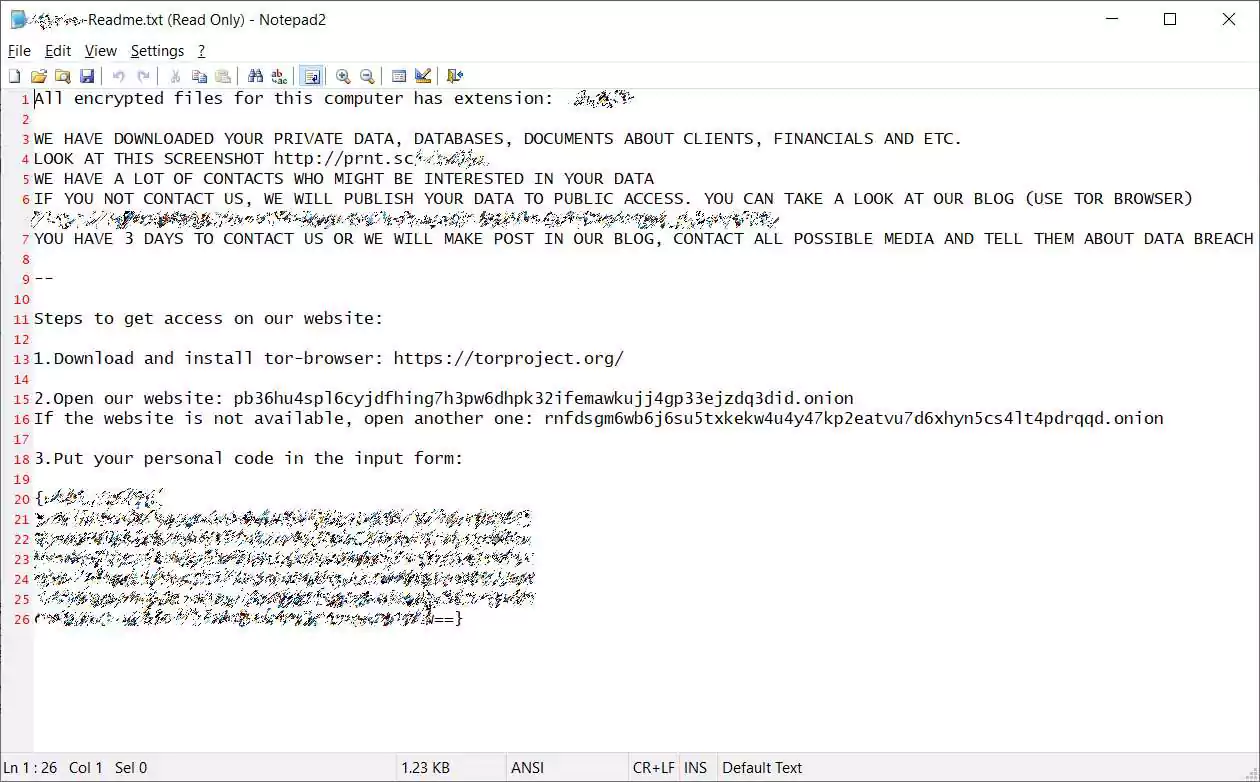
Included in the ransom note, was a link to a http://prnt.sc/ URL that showed data stolen from the attack. Based on the names of the employees in the folders, it was determined that the attack was on Enel Group.
Also Read: How Bank Disclosure Of Customer Information Work For Security
BleepingComputer emailed Enel Group last week regarding the attack but never heard back.
A few days later, Netwalker confirmed that the victim was Enel Group after they added a message to their support chat, stating “Hello Enel. Dont be afraid to write us.”
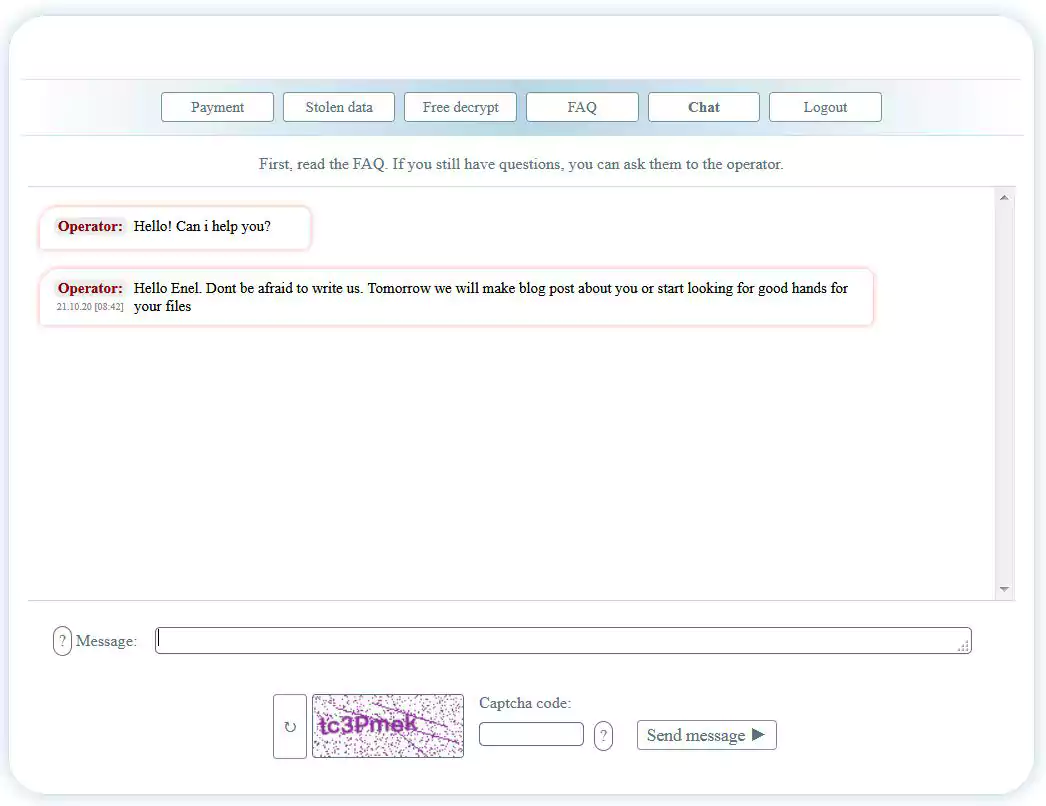
Typically, if the company does not engage the ransom operator in any way, the ransom doubles after a while. It appears that this is what happened with Enel, too, as the private chat provided by the attacker has no conversation from the company.
The attacker used this channel to announce that they would initiate the first step towards leaking the stolen data. This means publishing proof that they have the goods, an attempt to pressure the company into paying the ransom, which is now $14 million (1234.02380000 BTC).
Also Read: Data Protection Framework: Practical Guidance For Businesses
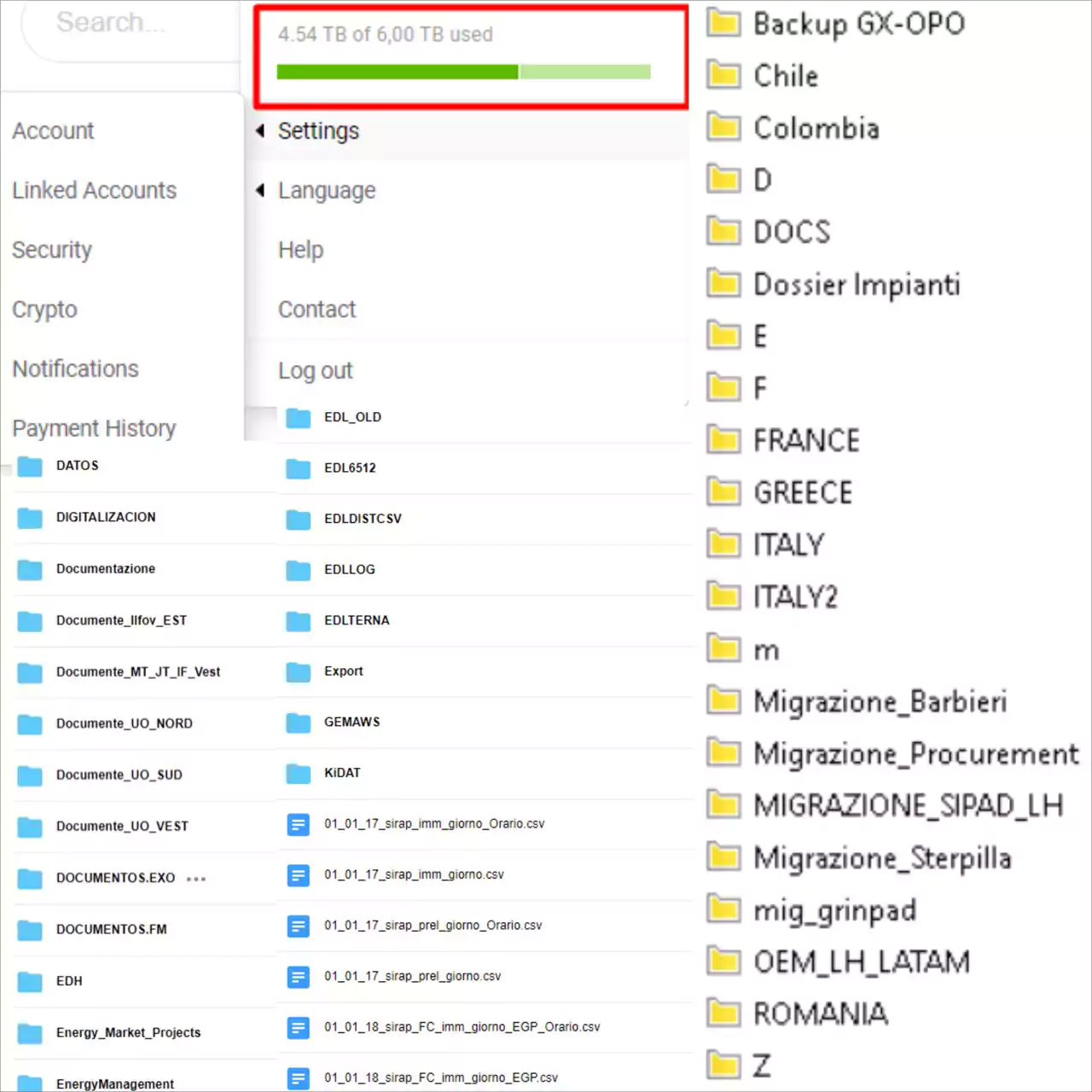
Today, the Netwalker ransomware gang added Enel Group to their data leak site and shared screenshots of unencrypted files from the company during this month’s cyberattack.
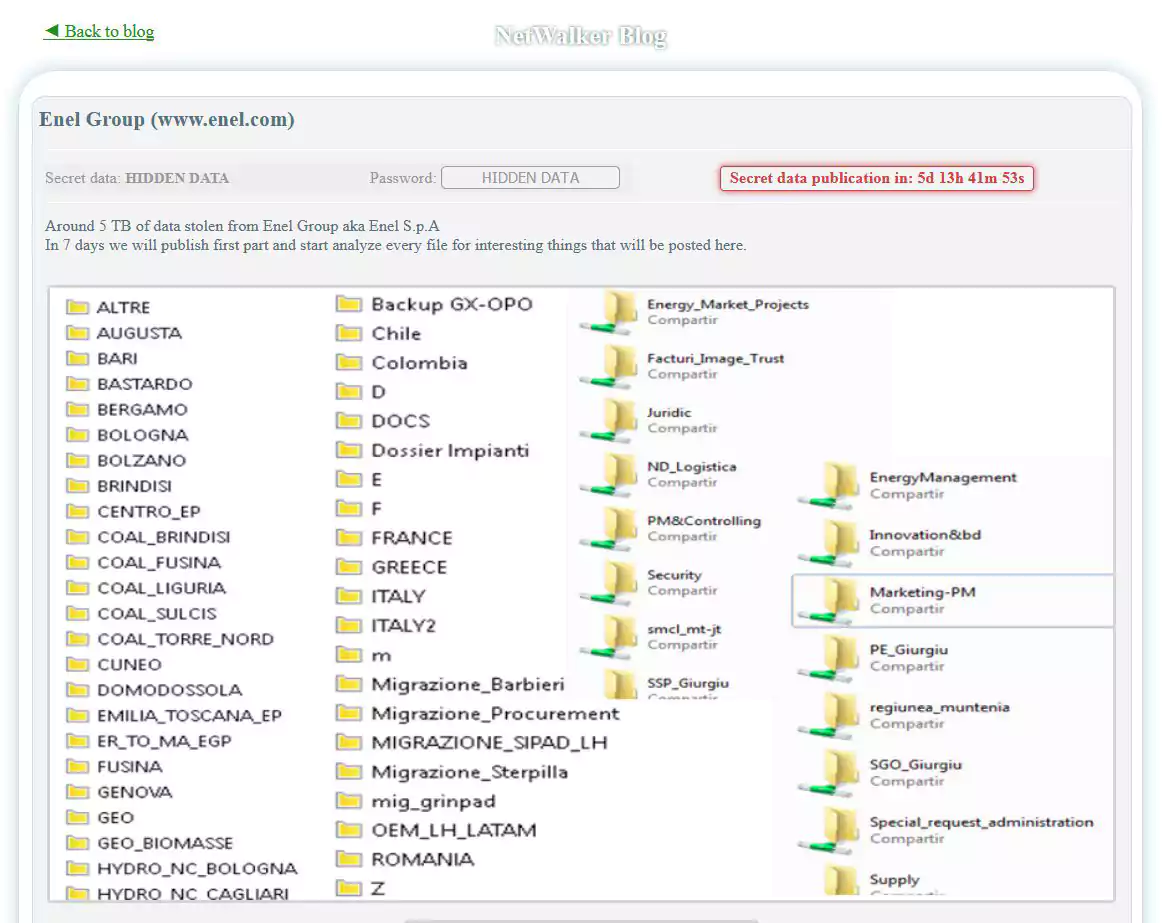
According to Netwalker, they stole about 5 terabytes of data from Enel and are ready to make public a piece of it in a week. They also said they would “analyze every file for interesting things” and publish it on their leak site.
This tactic is meant to add pressure and force payment from the victim company. In many cases, this works to the advantage of the attacker.