KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A recent wave of phishing attacks aiming to steal payment card info and credentials for Netflix streaming service starts with redirecting to a functioning CAPTCHA page to bypass email security controls.
The actor behind these attempts used a “failed payment” theme to engage potential victims into the redirect chain leading to the phishing page.
The fraudulent emails were sent at the beginning of the month and purported to be a notification from the Netflix support service about issues with verifying the billing address and payment details.
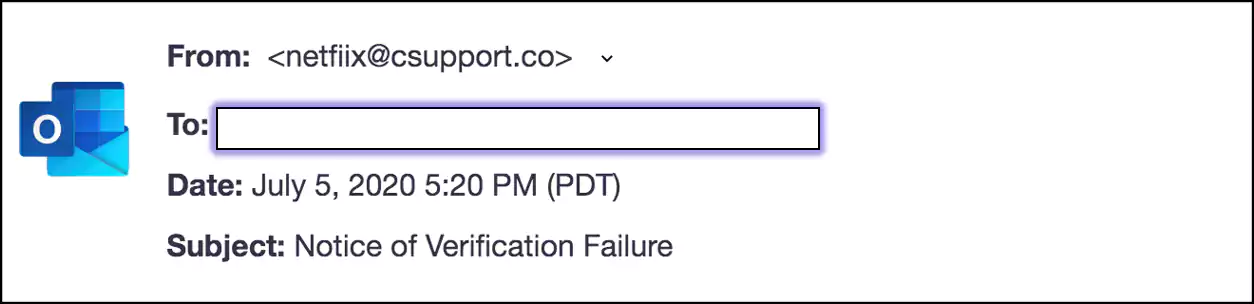
Looking at the sender’s address ([email protected]), it is clear that the attacker made an effort to make it look legitimate by trying to impersonate Netflix’s customer support.
Researchers at Armorblox, a company fighting targeted email attacks, analyzed the redirection chain. It all starts with a link in the message that takes to the phishing page.
However, some security solutions fail to detect the page as a threat because it is hidden behind a functional CAPTCHA challenge-response test.
Apart from preventing defense systems from reaching the malicious page, the CAPTCHA also gives a sense of legitimacy to the communication. The URL has been taken down.
Also read: How to Write an Effective Privacy Statement for Websites
The phishing page is a good impersonation of the original Netflix login portal but all the links just reload the same page. Also, the domain loading it, despite being legitimate, is a clear indication of a fake.
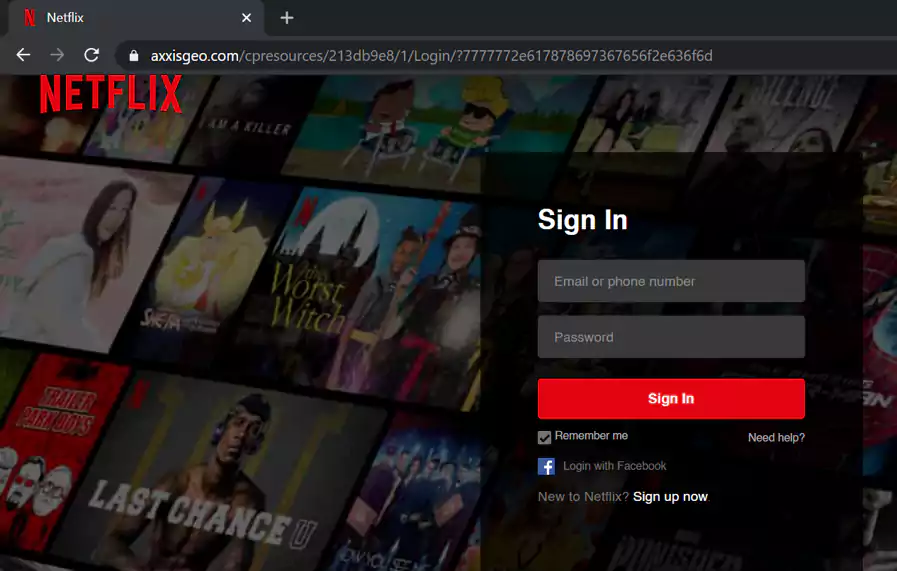
After typing in the credentials, another page loads, asking for a billing address and then for payment details (card number, expiration date, CVV, account number).
While these phishing attacks are not complex and humans could spot them if they pay attention to some details, they manage to easily bypass email security solutions.
By using a working CAPTCHA and hosting the pat phishing page on hacked legitimate websites, the actor is able to dodge filters for known bad domains and push the fraud without triggering the alarm.
Victims falling for these tricks may not learn about the fraud until it’s too late as the phishing flow ends with a “success” message. Being cautious when asked to provide sensitive details and checking the domain loading the page should help users spot phishing attempts.
Also read: 6 Simple Tips on Cyber Safety at Home