KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







NVIDIA has released a security update for a wide range of graphics card models, addressing four high-severity and six medium-severity vulnerabilities in its GPU drivers.
The security update fixes vulnerabilities that can lead to denial of service, information disclosure, elevation of privileges, code execution, etc.
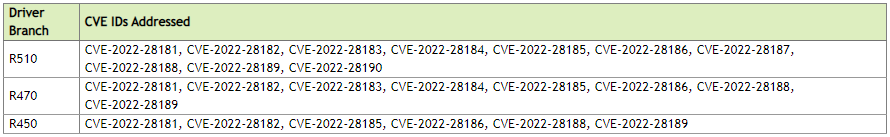
The updates have been made available for Tesla, RTX/Quadro, NVS, Studio, and GeForce software products, covering driver branches R450, R470, and R510.
Also Read: Protecting Data Online in the New Normal
Interestingly, apart from the current and recent product lines that are actively supported, NVIDIA’s latest release also covers GTX 600 and GTX 700 Kepler-series cards, whose support ended in October 2021.
The GPU maker previously promised to continue providing critical security updates for these products until September 2024, and this driver update honors that promise.
The four high-severity flaws fixed this month are:
These vulnerabilities require low privileges and no user interaction, so they could be incorporated into malware, allowing attackers to execute commands with higher privileges.
The first two are exploitable over the network, while the other two are exploited with local access, which could still be helpful for a malware infecting a system with low privileges.
Cisco Talos, which discovered CVE-2022-28181 and CVE-2022-28182, has also published a post today detailing how they triggered the memory corruption flaws by supplying a malformed compute shader.
Also Read: The Top 4W’s of Ethical Hacking
As threat actors can use a malicious shader in the browser by WebAssembly and WebGL, Talos warns that threat actors may be able to trigger this remotely.
“A specially-crafted executable/shader file can lead to memory corruption. This vulnerability potentially could be triggered from guest machines running virtualization environments (i.e. VMware, qemu, VirtualBox etc.) in order to perform guest-to-host escape. Theoretically this vulnerability could be also triggered from web browser using webGL and webassembly,” explains Talos regarding CVE-2022-28181.
For more details on all of the fixes and every software and hardware product covered this month, check out NVIDIA’s security bulletin.
All users are advised to apply the released security updates as soon as possible. Users can download the latest driver for their GPU model from NVIDIA’s download central section, where they can select the specific product and OS they are using.
The updates can also be applied through NVIDIA’s GeForce Experience suite.
However, if you don’t specifically need the software to save gaming profiles or use its streaming features, we recommend against using it as it introduces unnecessary security risks and the use of resources.