KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Exploit code that could be used for remote code execution on VMware vCenter Server vulnerable to CVE-2021-22005 has been released today and attackers are already using it.
Publicly disclosed earlier this week when VMware also addressed it, the bug comes with a critical severity rating of 9.8 and a strong recommendation to install the available patch.
The vulnerability affects machines running vCenter Server versions 6.7, and 7.0. Given the severity of the issue, VMware urges administrators to act immediately under the assumption that an adversary is already on the network, ready to take advantage.
Exposed vCenter servers are currently being targeted from various countries over multiple ports, threat intelligence company Bad Packets shared with BleepingComputer today; VMware confirmed this in an update to their security advisory for CVE-2021-22005, an arbitrary file upload vulnerability:
“VMware has confirmed reports that CVE-2021-22005 is being exploited in the wild”
Data recorded by Bad Packets shows attacks starting to hit their VMware honeypots at 16:21 (GMT) originating from Canada, the U.S., Romania, the Netherlands, China, and Singapore.
Signs of these attacks coming were seen shortly after VMware disclosed the security issue and released a patch. Just hours later, Bad Packets saw scanning activity targeting CVE-2021-22005.
Also Read: PDPA Breach Penalty Singapore: How Can Businesses Prevent
Troy Mursch, chief research officer at Bad Packets, told BleepingComputer that the attacks he saw against the company honeypots used code based on an incomplete exploit released earlier today by Vietnamese security researcher Jang.
Jang published technical notes for CVE-2021-22005 based on the workaround and the patch from VMware. The details are enough for experienced developers to create a working exploit that allows remote code execution with root privileges, the researcher told BleepingComputer.
At the end of the post, Jang also provides a link to his PoC version for CVE-2021-22005. It is not a fully functional variant, though, intentionally so to prevent less skilled threat actors from using it in attacks directly.
The researcher told us that in its current form the code does no harm because it is missing the important part leading to remote code execution.
An adversary would have to put in some effort to turn it into a full-fledged exploit but they should be able to create an exploit that is 100% reliable.
Penetration tester and Synack Envoy Nicolas Krassas tested the code and confirmed that it needs some modifications to work properly. But it does prove that CVE-2021-22005 can be used to create a backdoor on a vulnerable system.
Jang built a fully functional exploit and tested it in a controlled environment. He said that it works just fine, obtaining remote code execution before detection can catch it.
Currently, search engines for internet-connected devices show thousands of VMware vCenter Server instances exposed to the public internet. Shodan retrieved more than 5,000 machines while a rough search on Censys shows around 6,800.
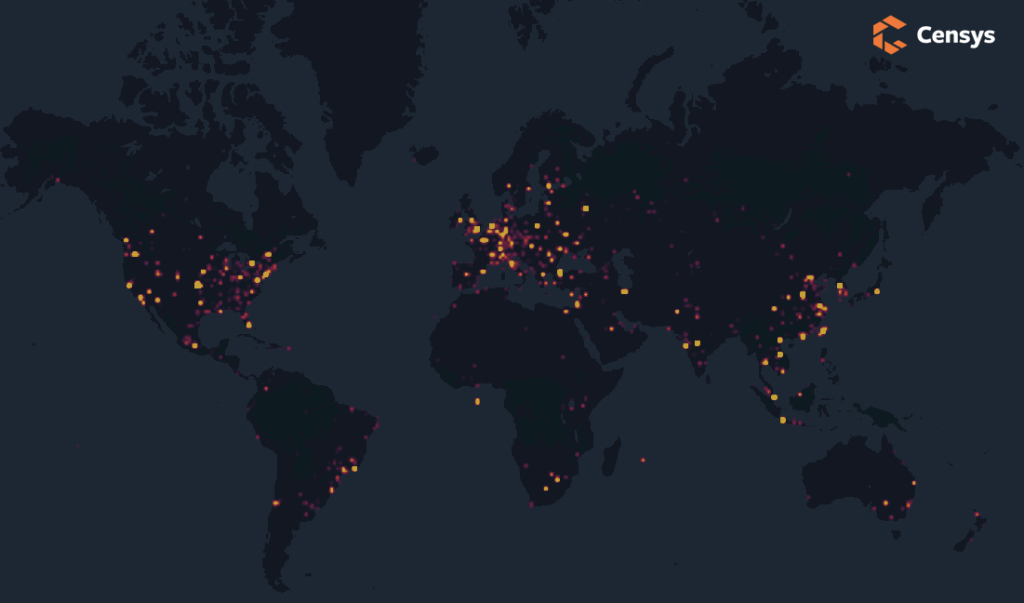
Not all servers are vulnerable to CVE-2021-22005, though. Censys notes that 3,264 of these internet-facing hosts are “are potentially vulnerable” and 436 are patched.
Still the number of potential targets is quite high and given the threat actors’ early interest in scanning for vulnerable machines it is easy to conclude that attacks were imminent.
Talking to BleepingComputer about his incomplete exploit, Jang said that an average-skilled adversary should need about an hour to build a working, reliable version. He strongly advises administrators to patch their systems to defend against attacks leveraging CVE-2021-22005.
Also Read: Data Protection Authority GDPR: Everything You Need To Know
The U.S. Cybersecurity and Infrastructure Seurity Agency (CISA) urges critical infrastructrure organizations with vulnerable vCenter deployments to apply the updates or the termporary workaround from VMware.
A post from Censys explains that a remote code execution exploit is not difficult to create based on the technical details already published in the public space:
“The cURL-based exploit in blog post does not demonstrate direct code execution, although a savvy reader can use the information in this post to achieve this goal with some knowledge of the Linux operating system. Censys has decided to release this detail, given that opportunistic scanning is already taking place, and VMware’s workaround mentions the specific vulnerable endpoint.”
The researcher also published a video to demonstrate how an attacker could exploit the vulnerability:https://www.youtube.com/embed/WVJ8RDR7Xzs
Update [September 24, 2021 – 17:41 EST]: Shortly after publishing, BleepingComputer learned that hackers have started to exploit CVE-2021-22005 using code released by security researcher Jang. We have updated the article with information about the attacks.