KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






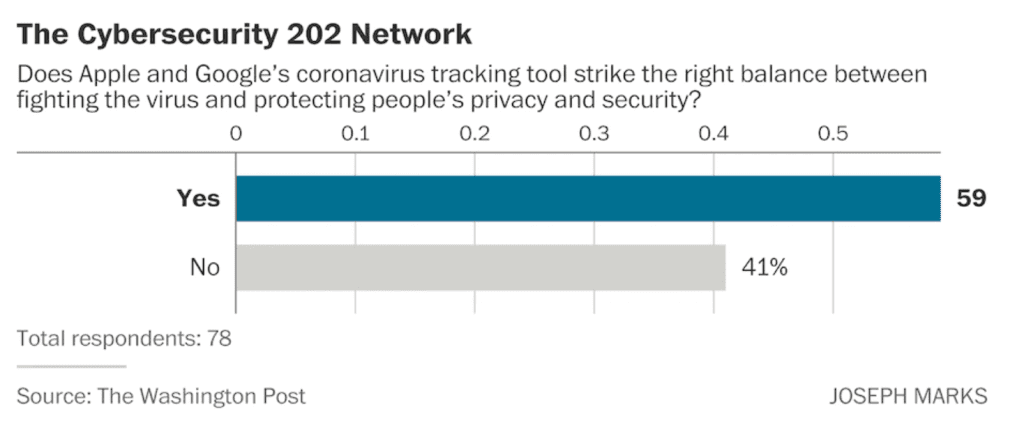
Apple and Google struck the right balance between protecting privacy and combating the coronavirus in a tool they released to help alert people who’ve been exposed to the disease, according to a majority of cybersecurity experts.
That assessment from 59 percent of The Network, a panel of more than 100 cybersecurity experts who participate in our ongoing informal survey, marks a vote of confidence for the system embraced by some state and national public health agencies but criticized by others for not providing enough information to help them slow the disease’s spread.
A number of states and at least 22 countries plan to build exposure notification apps using the technology.
“There is no perfect balance between fighting the virus and protecting privacy…[But] the capability offered by these companies represents a useful step,” said Sam Visner, director of the National Cybersecurity Federally Funded Research and Development Center, which is managed by the Mitre Corporation.
“While the Google and Apple approach has some risks, the limits on what is collected, along with a thoughtful approach on restricting how the data is processed and accessed, creates a net positive benefit,” McAfee Chief Technology Officer Steve Grobman said. The Network features experts from the U.S. government, private sector and the security research community. (You can see the full list of experts here.)
The Apple-Google system generally comes down on the privacy side of the ledger.
It isn’t an app itself but a framework that governments can use to build apps within narrow parameters that must be voluntary for users. Those apps use Bluetooth signals to record which phones are in proximity to each other and alert people if a phone they were near belongs to someone who self-reports testing positive for the virus.
The technology doesn’t collect any data about where those meetings took place or share any data with the government. All the data is also anonymized and stored on the phones themselves rather than on Apple or Google’s servers.

“There’s little question that we’ll need to use technology-enabled contact tracing to deal with covid-19. However, there’s also very little question that the government will try to use the data for other purposes,” said Jake Williams, a former NSA hacker who founded the company Rendition InfoSec. “I think the privacy protections built into the contact tracing tool by Apple and Google…probably are sufficient to stop the most egregious wholesale abuses.”
Jeff Moss, founder and CEO of DEF CON Communications, called the app “the best of a bad situation…when you trust tech monopolies more than your own government.”
Peter Swire, professor of law and ethics at the Georgia Institute of Technology, praised the system’s “relatively cautious approach to data collection,” which he noted “contrast[s] to the rush for data after 9/11,” which led to a sweeping expansion of U.S. intelligence capabilities.
“We haven’t yet grappled with the implications of these private companies taking on roles that have traditionally been done by government,” said Suzanne Spaulding, who led Department of Homeland Security cybersecurity operations during the Obama administration. “We have constitutional safeguards that apply to the government that don’t apply to the private sector. On the flip side, government has certain protections against liability that companies don’t.”

That’s a fear widely shared among public health officials. A University of Oxford study found about 60 percent of a population would need to opt in to such apps to make them effective at slowing disease spread. But only about 40 percent of Americans say they are willing and able to opt in, a recent Washington Post-University of Maryland poll found.
“The app is promising, but only if there is widespread adoption, especially among groups disproportionately infected,” said Lance Hoffman, who founded the Cybersecurity and Privacy Research Institute at George Washington University.
He urged public health agencies and small businesses to consider incentive programs to increase app downloads. “How about a $5 discount on your haircut if you show that the app is downloaded and enabled?” he suggested
A Google spokeswoman declined to comment on The Network survey but shared a broad statement that “adoption of these apps relies on user trust so privacy-preserving technology is complementary to public health goals.”
The companies consulted hundreds of public health agencies, government officials, privacy experts and academics before settling on its final model, she said.
Apple did not respond to a request for comment.

“While I’m typically a huge supporter of privacy-preserving technologies, I believe that, in this case, [the] Google/Apple approach [has] gone too far and fundamentally undermined the ability of public health authorities to perform contact tracing,” said Ashkan Soltani, a former chief technologist for the Federal Trade Commission.
Former NSA General Counsel Stewart Baker was even more critical. “In its extreme effort to protect privacy, the app sacrifices efficacy,” he said. “Contact tracing that doesn’t provide location data makes it much harder to identify the site of outbreaks and super spreader events.”
“Contact tracing is corporate surveillance by another name,” said Sascha Meinrath, a Penn State professor and founding director of X-Lab, a think tank focusing on the intersection of technologies and public policy. “Without clear consumer protections, coronavirus tracking is becoming a Faustian bargain whereby unsuspecting consumers are being subjected to immensely invasive tracking without any measurable public health benefit.”
Kiersten Todt, president of Liberty Group Ventures who led an Obama-era cybersecurity commission, said she was more concerned about Google, whose revenue comes largely from targeted ads based on users’ online activity, than Apple, whose business model is based on selling laptops, phones and other devices.
“Google’s business model relies on revenue generation from the collection of data,” she said. “Therefore, without appropriate federal — or even state — policies on data protection and privacy, it is difficult to trust Google’s intended use of the data collected through this tool.”
“I think the protests have highlighted how these sorts of voluntary/mandatory tracking systems can be abused,” said Dave Aitel, a former NSA computer scientist who is now CEO of the cybersecurity company Immunity, referring to recent law enforcement surveillance of protests following the police killing of George Floyd.
“New technology like this that could be repurposed sooner or later to track protesters and their contacts is a real threat to human rights and civil liberties,” Luta Security founder Katie Moussouris said.
Finally, some respondents worried the system simply won’t be effective because Bluetooth isn’t precise enough to tell whether people are genuinely close enough to each other to spread dangerous microbes or sitting on opposite sides of an office wall.
“We don’t know that this kind of tool will work given how hard it is to calculate proximity with Bluetooth,” said Jennifer Granick, surveillance and cybersecurity counsel at the American Civil Liberties Union’s Speech, Privacy and Technology Project.
“Why compromise privacy for a tool that is not the best way to suppress the spread of covid?” said Ashley Deeks, a former State Department official and professor at the University of Virginia Law School.