KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A banking trojan named Bizarro that originates from Brazil has crossed the borders and started to target customers of 70 banks in Europe and South America.
Once landed on a Windows system, the malware can force users into entering banking credentials and uses social engineering to steal two-factor authentication codes.
Bizarro is under constant development as its author keeps expanding the list of supporting banks and they modify it to improve anti-analysis protections.
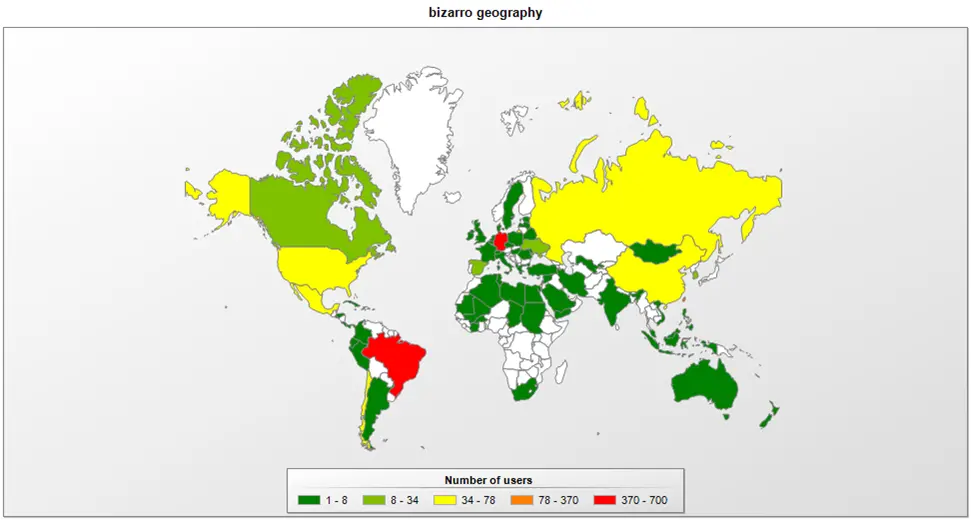
Statistics from cybersecurity company Kaspersky shows that Bizarro’s targets are now customers of banks in Europe (Germany, Spain, Portugal, France, Italy) and South America (Chile, Argentina, Brazil).
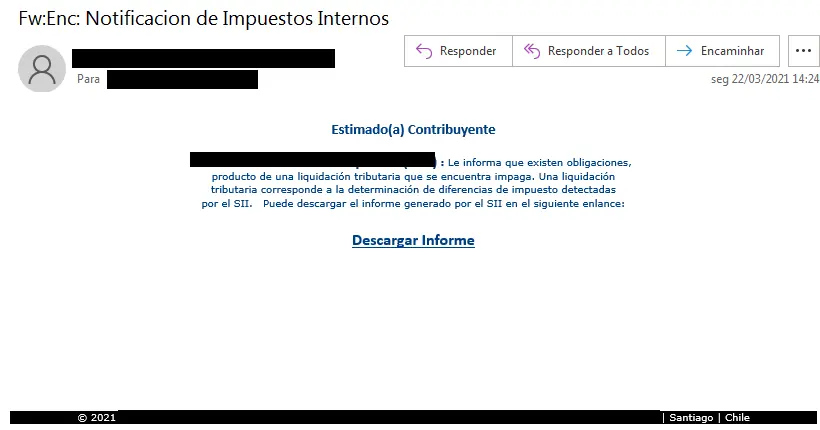
The malware spreads through phishing emails that are typically disguised as official tax-related messages informing of outstanding obligations.
The download link in the message retrieves Bizarro as an MSI package. After being launched, the malware downloads from hacked WordPress, Amazon, and Azure servers a ZIP archive with malicious components needed for the attack.
Also Read: Got Hacked? Here Are 5 Ways to Handle Data Breaches
After it starts, Bizarro will terminate any existing sessions with online banking services by killing all browser processes. This forces the user to re-enter the bank account credentials, allowing the malware to collect them.
The malware can also disable the auto-complete function in a web browser to capture login credentials when the victim types them manually.
Kaspersky researchers note that Bizarro’s core component is its backdoor functionality, which supports over 100 commands, most of them “used to display fake pop-up messages to users.”
The component becomes active only after the malware enumerates all windows to check for a connection to one of the supported banking sites.
Bizarro can receive the following types of commands from its command and control server:
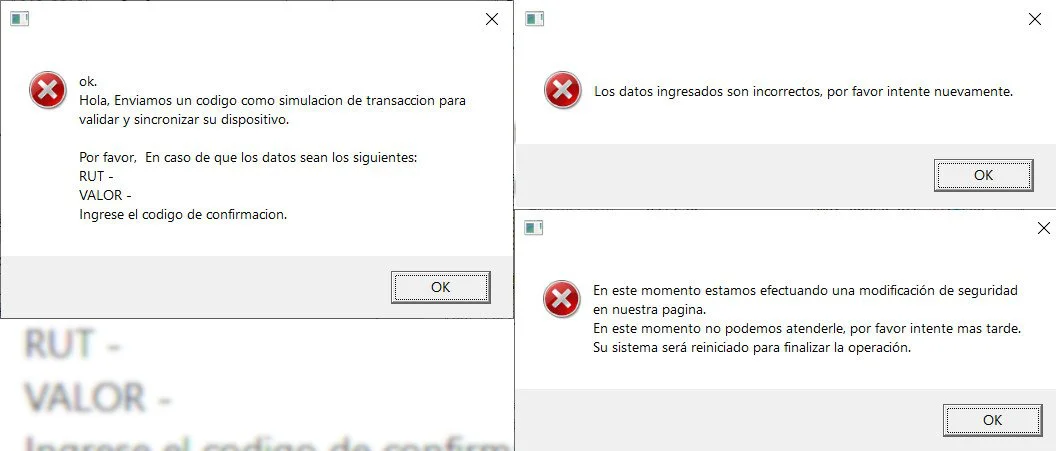
Using specific commands for the backdoor component, Bizarro’s operators can trick users into providing the bank account login information by showing them message boxes or windows asking for login data or two-factor authentication codes.
Using specific commands for the backdoor component, Bizarro’s operators can trick users into providing sensitive information by showing them custom message boxes or windows.
The messages vary from fake notifications requesting the details again or asking to enter a confirmation code to a bogus error informing that the system needs a restart to complete a security-related operation.
Another social engineering trick in Bizarro’s hat is displaying JPEG images containing a target bank’s logo and instructions for the victim.
Some of these messages may block access to the entire screen and hide the taskbar, making it more difficult to start Task Manager.
Most of the images try to convince the victim that their system is compromised or needs an update, or that security and performance components for the browser need to be installed.
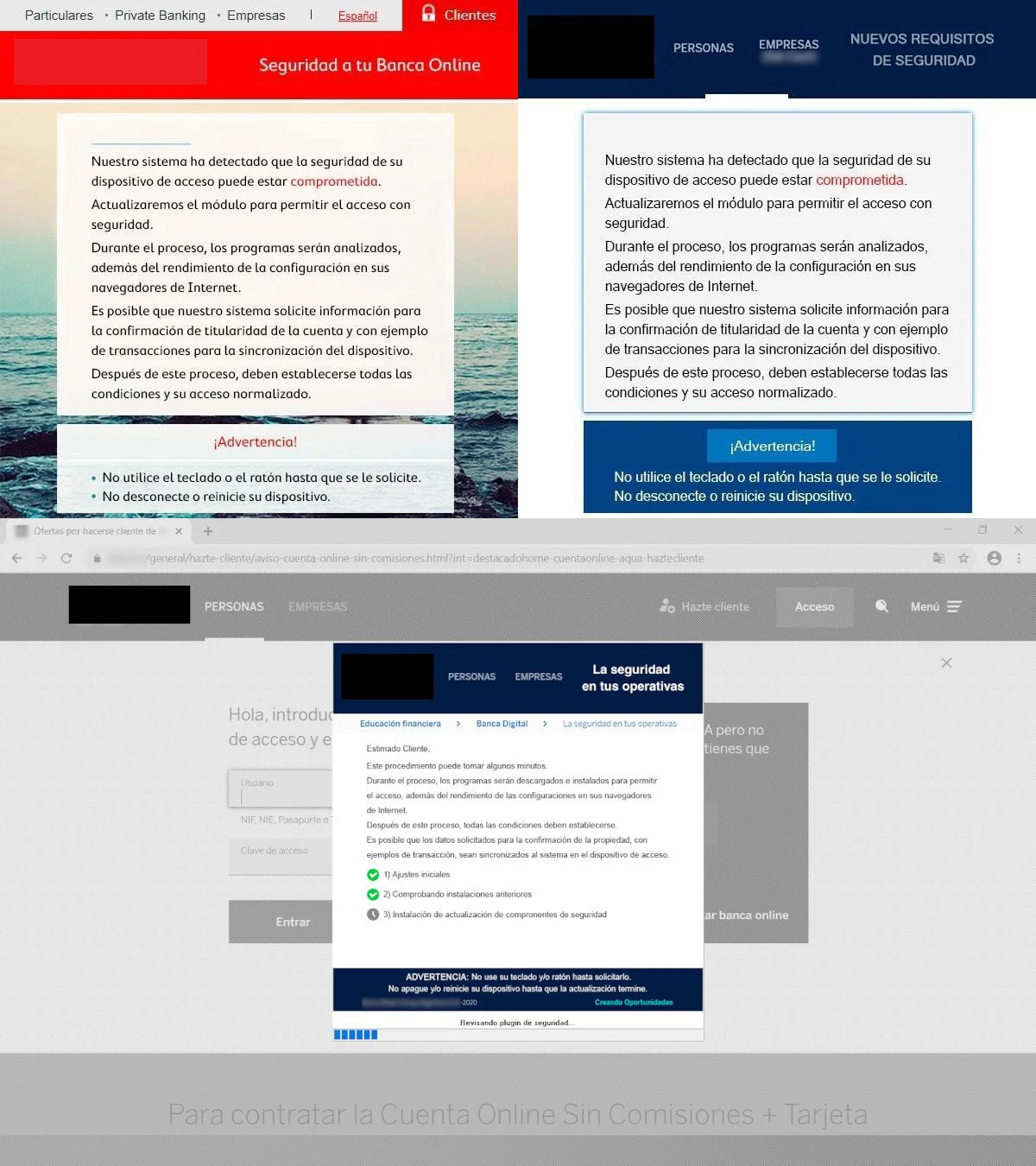
The social engineering component expands to trick victims into installing on their phones a fraudulent banking app, which enables the collection of credentials and sensitive codes from mobile devices.
Based on the commands supported by the trojan, an attack scenario on a compromised computer starts with the victim accessing a banking website.
The keylogging function in the malware captures the account password and then fake messages are shown to collect the two-factor authentication code.
Cybercriminals can buy some time to prepare a fraudulent transaction by showing a fake alert from the bank that blocks access to the screen.
Also Read: Compliance Course Singapore: Spotlight on the 3 Offerings

Kaspersky says that Bizarro is not the only banking trojan in South America that expands to Europe. Other malware has followed the same path recently, namely Guildma (a.k.a. Astaroth), Amalvado, Javali, Melcoz, and Grandoreiro. All of them were created, developed, and spread in Brazil and have expanded outside Latin America.