KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







CISA officials said that, so far, there is no evidence of US federal civilian agencies compromised during ongoing attacks targeting Microsoft Exchange servers.
This statement is based on information collected by federal agencies following an emergency directive issued by the US Cybersecurity and Infrastructure Security Agency (CISA) one week ago.
The directive ordered the agencies to urgently update or disconnect their Microsoft Exchange on-premises servers and check their networks for indicators of compromise.
“At this point in time, there are no federal civilian agencies that are confirmed to be compromised by this campaign,” Eric Goldstein, CISA executive assistant director for cybersecurity, said in a testimony before the Homeland Security Subcommittee.
Goldstein added that most Exchange servers have already been patched across federal agencies’ networks after CISA’s directive.
Also Read: In Case You Didn’t Know, ISO 27001 Requires Penetration Testing
“We have seen outstanding responses to that directive and now the vast majority of Microsoft Exchange Servers have been mitigated across the federal civilian executive branch.”
CISA is in the “early days of the investigation of exploitation of Microsoft Exchange servers,” according to Goldstein, and is still analyzing forensic results provided by individual agencies.
Last week, Microsoft and multiple cybersecurity firms had disclosed ongoing attacks coordinated by several state-backed hacking groups.
These indiscriminate attacks currently target organizations from multiple industry sectors worldwide, attempting to steal sensitive information from unpatched and Internet-exposed on-premises Exchange servers.
Microsoft initially reported that the Microsoft Exchange vulnerabilities (dubbed ProxyLogon) were actively exploited by a Chinese APT group named Hafnium.
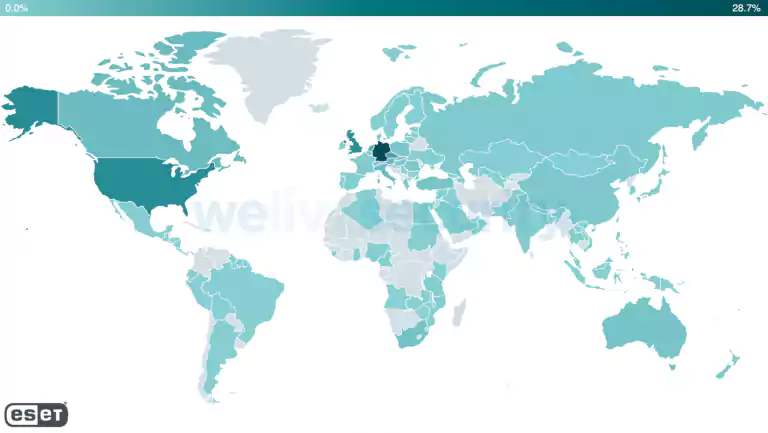
Adding to that, during the last week, Slovak internet security firm ESET shared info on at least ten other APT groups actively abusing these bugs.
According to ESET’s (incomplete) telemetry, web shells have already been deployed by state hackers on more than 5,000 Exchange servers from over 115 countries.
Yesterday, a Vietnamese security researcher publicly shared a (mostly) working ProxyLogon proof-of-concept exploit (the PoC has now been removed from the GitHub repository where it was published).
While the release of a PoC exploit will not immediately result in a flood of new attackers joining in, it could lower the bar for those without the needed skills to create their own exploits from scratch.
Also Read: 4 Considerations In The PDPA Singapore Checklist: The Specifics
The Dutch Institute for Vulnerability Disclosure (DIVD) said Tuesday that it found 46,000 Exchange servers unpatched against the heavily abused ProxyLogon vulnerabilities after scanning 250,000 Exchange servers worldwide.