KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Leading cybersecurity firm CrowdStrike was notified by Microsoft that threat actors had attempted to read the company’s emails through compromised by Microsoft Azure credentials.
Earlier this month, it was discovered that the SolarWinds network management company suffered a cyberattack where threat actors modified their software to install backdoors on customers’ networks via a supply chain attack.
Due to this attack, SolarWinds customers have been scrambling to analyze their networks to see if they were compromised in the supply chain attack.
After performing an analysis of their internal and production environment, CrowdStrike stated Thursday that they had found no signs that the SolarWinds breach impacted them.
Also Read: How To Prevent WhatsApp Hack: 7 Best Practices
While performing their investigation, CrowdStrike was told by Microsoft on December 15th that a compromised Microsoft Azure reseller’s account was used to try and read CrowdStrike’s emails.
“Specifically, they identified a reseller’s Microsoft Azure account used for managing CrowdStrike’s Microsoft Office licenses was observed making abnormal calls to Microsoft cloud APIs during a 17-hour period several months ago. There was an attempt to read email, which failed as confirmed by Microsoft. As part of our secure IT architecture, CrowdStrike does not use Office 365 email,” CrowdStrike CTO Michael Sentonas disclosed.
A source familiar with the investigation told Reuters that the compromised reseller account had attempted to enable Office 365 ‘Read’ privileges to access CrowdStrike’s email. As CrowdStrike does not use Office 365, the attack failed.
Microsoft senior director Jeff Jones told Reuters that this attack was made by the hackers stealing the credentials for the Microsoft reseller’s account rather than vulnerabilities in their products or cloud services.
“Our investigation of recent attacks has found incidents involving abuse of credentials to gain access, which can come in several forms,” Jones told Reuters. “We have not identified any vulnerabilities or compromise of Microsoft product or cloud services.”
In two articles published this month, Microsoft disclosed how stolen credentials and access tokens are being used to target Azure customers. It is strongly recommended that Azure administrators review these articles to learn more about these attacks and discover anomalous behavior in their tenants.
CrowdStrike has stated that they do not know of any attribution or connection between their attempted hack and the attackers behind the SolarWinds attack.
After learning of this attempted attack, CrowdStrike analyzed their Azure environment and found it was not compromised. However, during this analysis, they found it challenging to use Azure’s administrative tools to enumerate privileges assigned to third-party resellers and partners in their Azure tenant.
“We found it particularly challenging that many of the steps required to investigate are not documented, there was an inability to audit via API, and there is the requirement for global admin rights to view important information which we found to be excessive. Key information should be easily accessible,” Sentonas continued.
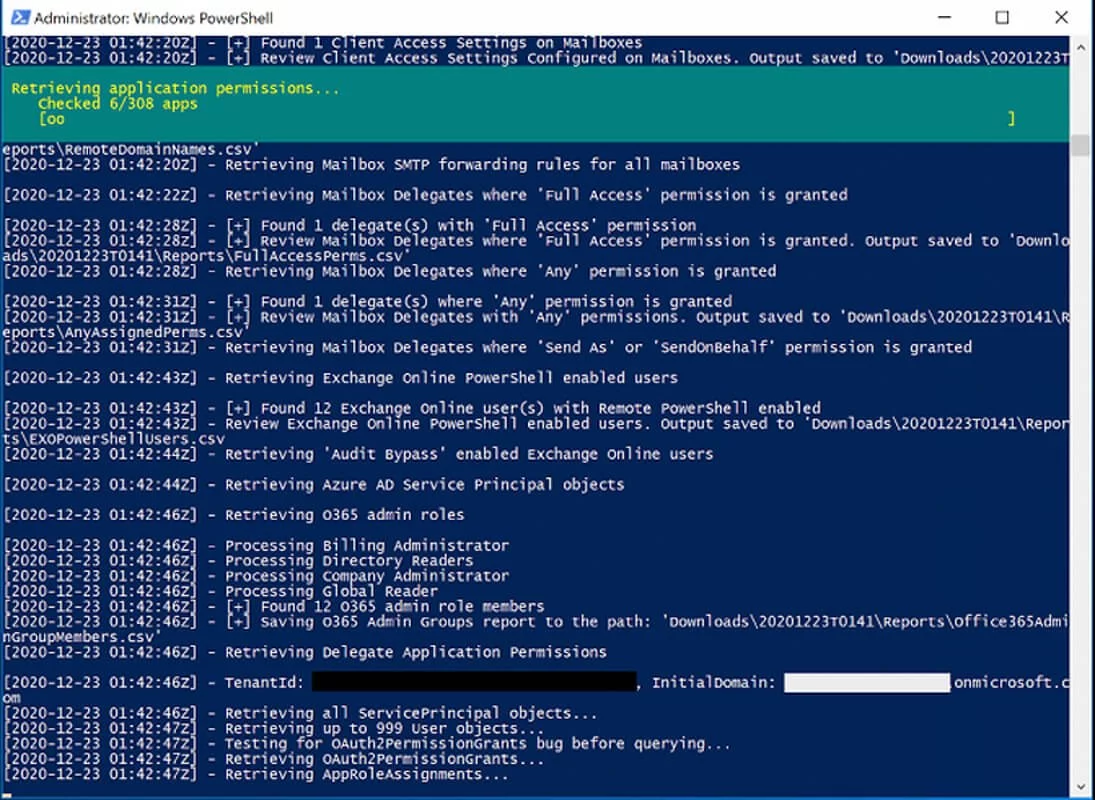
To help administrators analyze their Microsoft Azure environment and see what privileges are assigned to third-party resellers and partners, CrowdStrike has released a free CrowdStrike Reporting Tool for Azure (CRT) tool.
Also Read: 15 Best Tools For Your Windows 10 Privacy Settings Setup
This tool will analyze an Azure environment and create a report listing the following:
Exchange Online (O365):
Azure AD:
CrowdStrike has created full instructions on how to download and use this tool on their GitHub page.