KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







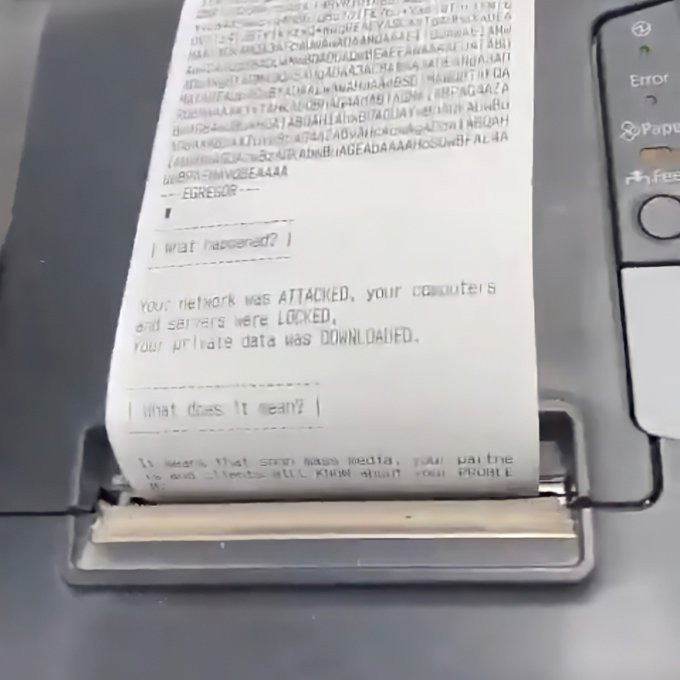
The Egregor ransomware uses a novel approach to get a victim’s attention after an attack – shoot ransom notes from all available printers.
Ransomware gangs know that many businesses would rather hide a ransomware attack than make it public, including to employees, for fear of the news affecting stock prices and their reputation.
To increase public awareness of the attack and pressure a victim into paying, the Egregor operation is known to repeatedly print ransom notes from all available network and local printers after an attack.
While BleepingComputer has been aware of this tactic, it wasn’t until last weekend after Egregor’s attack on retail giant Cencosud that we saw it in action.
Also Read: A Look at the Risk Assessment Form Singapore Government Requires
As you can see from a closeup of the printout, this is the same ransom note created on computers being printed to a receipt printer.
BleepingComputer can confirm that it is not the ransomware executable performing the printing of ransom notes.
Instead, it is believed that the ransomware attackers utilize a script at the end of an attack to print out ransom notes to all available printers.
This script has not been found as of yet.
Also Read: CCTV Law Singapore Edition: Know Your Rights and Responsibilities