KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







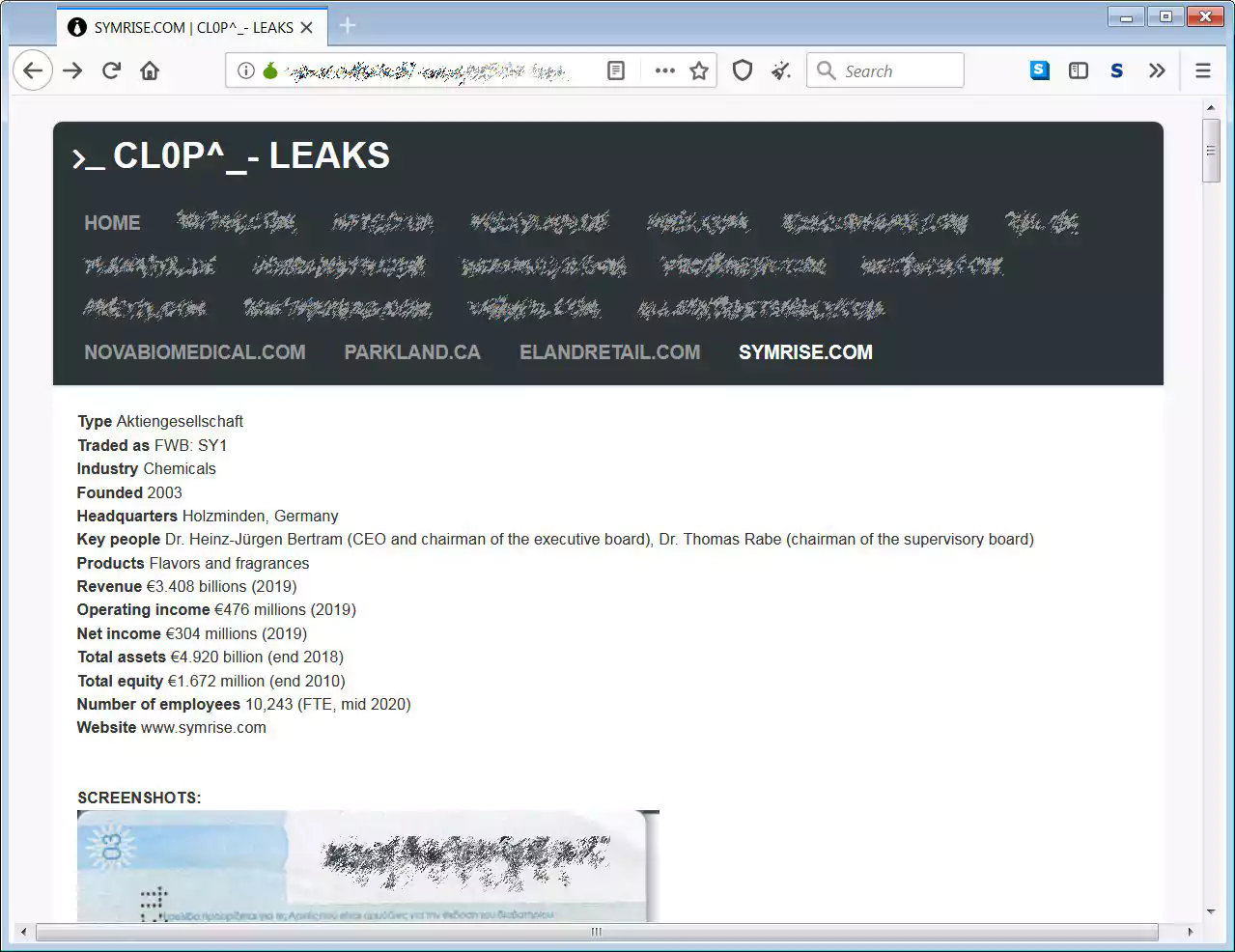
Flavor and fragrance developer Symrise has suffered a Clop ransomware attack where the attackers allegedly stole 500 GB of unencrypted files and encrypted close to 1,000 devices.
Symrise is a major developer of flavors and fragrances used in over 30,000 products worldwide, including those from Nestle, Coca-Cola, and Unilever. Symrise generated €3.4 billion in revenue for 2019 and employs over 10,000 people.
Last week, German media reported that Symrise suffered a cyberattack that forced them to shut down their systems to prevent the spread of the attack.
“In order to be able to assess the consequences and to prevent possible further effects, the company shut down all essential systems,” Symrise told Handelsblatt.
Symrise also stated that they temporarily halted production and shut down facilities to further investigate the attack’s scope.
If you have first-hand information about this or other unreported cyberattacks, you can confidentially contact us on Signal at +16469613731 or on Wire at @lawrenceabrams-bc.
The Clop ransomware gang has claimed responsibility for the attack on Symrise and have told BleepingComputer that they allegedly encrypted 1,000 devices.
Also Read: Going Beyond DPO Meaning: Ever Heard of Outsourced DPO?
Clop told BleepingComputer they compromised Symrise’s network using malware distributed via phishing emails. Once they gained access to the network, Clop stated they stole 500 GB of unencrypted files before deploying their ransomware.
As proof of this theft, Clop has posted images of these allegedly stolen files on their data leak site. The leaked images are for passports, accounting documents, audit reports, confidential cosmetic ingredients, and emails.
Clop ransomware is also behind attacks on Maastricht University, Software AG IT, ExecuPharm, Indiabulls, and E-Land, where they also claimed to have stolen 2 million credit cards.
BleepingComputer reached out to Symrise last week with questions regarding this attack but did not receive a response.
Also Read: Limiting Location Data Exposure: 8 Best Practices