KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







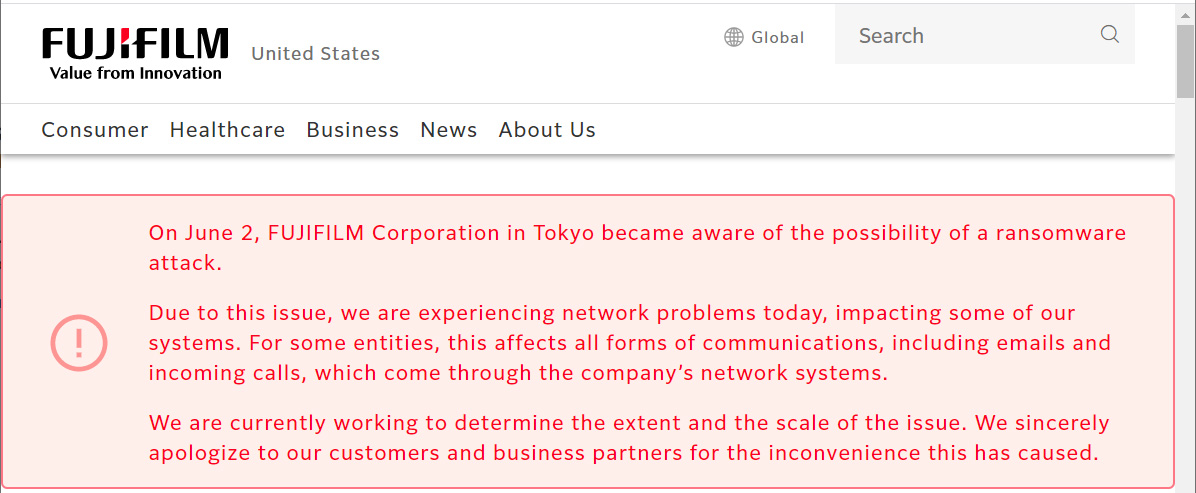
Japanese multinational conglomerate Fujifilm says that it has resumed normal business and customer operations following a ransomware attack that forced it to shut the entire network on June 4.
At roughly 10:0 AM EST, Fujifilm asked employees to immediately shut off their computers and all servers on the network after an ongoing network outage blocked access to email, the billing system, and an internal reporting system.
“After that, from June 4th, we started operating servers and computers that were confirmed to be safe, and resumed communication on the network that had been blocked,” Fujifilm said in a statement issued earlier today.
“We are pleased to inform you that by today, normal operations for customers and business partners, such as reception of inquiries and orders and shipments of our products, have been restored.”
Although in most ransomware attacks, the threat actors are also exfiltrating data before encrypting the victims’ systems, Fujifilm stated that the “investigations completed so far have found no evidence of information leakage to the outside world.”
Also Read: This Educator Aims to Make Good Cyber Hygiene a Household Practice
“In addition, countermeasures against this unauthorized access have already been implemented. We will continue to monitor and continue to strengthen information security,” Fujifilm added.
We deeply apologize for causing a great deal of inconvenience and concern to our customers and business partners. – Fujifilm Corporation
While Fujifilm did not reveal the name of the ransomware operation that managed to breach its network and take it down on June 4, Advanced Intel CEO Vitali Kremez told BleepingComputer that some of the company’s systems were infected with the Qbot trojan last month.
“A network infection attributed to QBot automatically results in risks associated with future ransomware attacks,” Kremez said.
Qbot trojan’s operators have a long history of working with ransomware gangs, providing them with remote access to previously infected networks.
The ProLock and Egregor ransomware groups are known to have partnered with Qbo in the past but, after those operations shut down, REvil is the new ransomware gang that has been using the botnet to gain access to victims’ networks.
While these are only theories at the moment, we will know soon enough who was behind the attack since, if data was stolen in the attack, it will likely be released on a ransomware data leak site and used as leverage to force Fujifilm to pay the ransom.
Fujifilm is far from the first Japanese company to have had its network breached in recent years, with Kawasaki, NEC, Mitsubishi Electric, and defense contractors Kobe Steel and Pasco also having disclosed security incidents and, in some cases, even data leaks.
Also Read: The 5 Phases of Penetration Testing You Should Know
Tokyo-based Japanese multinational conglomerate FujiFilm reported revenues of $20.1 billion in 2020, and it employs 37,151 people worldwide.
FujiFilm initially started in optical film and cameras and expanded to other activity domains, including pharmaceuticals, storage devices, and photocopiers and printers (XEROX).