KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







It’s not at all surprising that the forced restrictions over the past year have pushed more and more people online. The beginning of 2021 saw 4.6 billion active internet users worldwide, with over 5 million of them hailing from Singapore. Apparently, this increasing digital adoption in Singapore is also linked to a surge in cybercrime, accounting for 26.8% of all crimes in the island nation in 2019 alone.
Although Singaporeans have high levels of concern for cyber incidents, there is still much room for improvement. For instance, the majority have not installed security applications in their devices even when they are aware of the risks. In addition, the idea that “cyber incidents would not happen to me” is still flagrant, and many have difficulty identifying phishing emails.
Kids, especially, are the most vulnerable in the online world. However, a Google survey reviewed that 1 in 5 parents have done nothing to address safety concerns to their children when it comes to their online practices. These numbers and findings underscore the urgency for education in the area of good cyber hygiene practice, both for individuals and business entities, and ranging from kids to adults
Rising to the challenge is Mark Barnabas Lee, an expert in the area of risk management and data protection. Through “Data Heist”, a first-of-its-kind card game he is currently working on, Mark hopes to make good cyber hygiene a household thing – a daily habit, even – akin to the literal washing or sanitising of hands. In an email interview, Privacy Ninja caught up with the educator to discuss more about Data Heist, good cyber hygiene, data protection, and everything in between.
Also Read: Going Beyond DPO Meaning: Ever Heard of Outsourced DPO?
“Cyber security and data protection are typically not the most exciting topics and yet these are mandatory requirements especially for larger organisations,” Mark begins. The entrepreneur’s background in education and experiential learning solidified his belief that there is always a better, more effective, and more exciting way to learn.
According to Mark, the idea for Data Heist came from an afternoon with friends, when they were playing board. While having a discussion about how board games can be used for education, they encouraged Mark to create a board game to educate the public on data protection and cyber hygiene, a topic that he teaches. Thus, Data Heist was created.
The synopsis of the game sounds intriguing: you are a rookie hacker and want to be admitted into the inner circle of the hacking fraternity. Prove your worth by stealing as much personal data from the marketplace and prevent your competitors from stealing as well. The winner of the challenge will be handsomely rewarded!
Mark claims that the game, although not the first concept in the space of good cyber hygiene and data protection, is the first that’s built for fun and has the capacity to reach out both the employees on the ground and the younger audience (aka the kids).
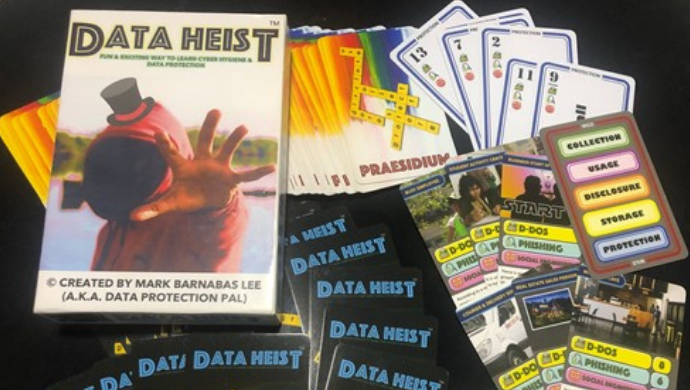
Many of the current courses on data protection (such as PDPA Obligations for Organizational Compliance) are understandably geared towards the workforce. With Data Heist, Mark intends to broaden the reach of awareness, while still ensuring that privacy practitioners such as himself can use the Praesidium set of cards for advisory and training.
What’s up ahead for Data Heist? Mark’s vision for the game is for it to be considered a Data Protection Pal to all, in that it will be in every classroom and boardroom.
“I envision Data Heist to educate the youth and business leaders on good cyber hygiene and promote the ethical collection, use, and disclosure of personal data,” he concludes. To learn more about the premise of Data Heist, watch the short video here.
Also Read: The 5 Phases of Penetration Testing You Should Know
Privacy Ninja, one of Singapore’s best compliance experts and corporate training facilitators, is fully supportive of innovations that promote good cyber hygiene and PDPA compliance, such as Mark Lee’s Data Heist. Besides, Mark is no stranger to the Privacy Ninja team, having guested at one of their podcast episodes in February 2021. To digress, these podcasts also serve to educate the audience on best practices, latest data breach cases, and PDPA obligations.
Just like Mark Lee’s desire to make good cyber hygiene practice as seamless as the literal sanitising of hands, Privacy Ninja also envisions a Singapore nation filled with digitally responsible individuals who are aware of both their rights and responsibilities in the online world.
To learn more about how Privacy Ninja’s affordable DPO and cybersecurity services can help your oganisation in your PDPA compliance journey, contact us here.