KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






At least 15 websites belonging to various Ukrainian public institutions were compromised, defaced, and subsequently taken offline.
This includes the websites of the ministry of foreign affairs, agriculture, education and science, security and defense, and the online portal for the cabinet of ministers.
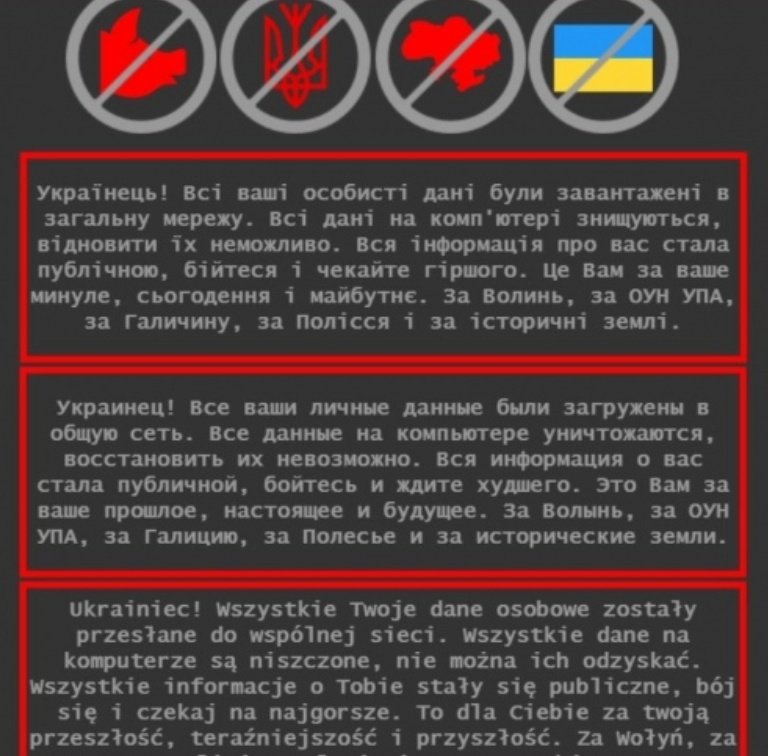
The defacement messages were posted in Ukrainian, Russian, and Polish, warning the sites’ visitors that all citizen data uploaded to the public network had been compromised.
At the time of writing this, some of the websites remain inaccessible as the country’s IT specialists are still in the process of restoring them.
The Ukrainian cyber-police has also posted an announcement where they underline that no personal data was compromised due to these attacks and that the warning messages to visitors were false and only meant to scare citizens.
Also Read: Top 10 Reliable IT Companies in Singapore
“In order to prevent the spread of the attack on other resources and localization of the technical problem, the work of other government sites was temporarily suspended,” explains the police announcement (translated).
“Currently, the Cyberpolice Department together with the State Special Communications Service and the Security Service of Ukraine are collecting digital evidence and identifying those involved in the cyber attacks.”
Sources have told journalist Kim Zetter that all 15 compromised Ukrainian sites were using an outdated version of the October CMS, vulnerable to CVE-2021-32648.
This is a critical (CVSS: 9.1) authentication flaw allowing an attacker to send a specially crafted request to perform a password reset on the platform, thus taking over admin accounts.
This vulnerability was fixed with build 472 version 1.1.5, released in August 2021, but it appears that several Ukrainian government websites hadn’t applied the security updates.
A later advisory from the Ukraine cyber-police confirmed Zetter’s reporting of the October CMS vulnerability as the intrusion vector.
Today, after Ukraine had acknowledged their attacks, the Polish Ministry of National Defense also announced that some of their databases containing sensitive military information were compromised.
The Ministry underlines that it’s not sure whether the accessed database contained test files or actual data, and investigations are still ongoing.
However, members of the local press speak with certainty about the validity of the leaked files and the link to the Ukrainian cybersecurity incident.
The cyber-police has opened criminal proceedings under Article 361 (unauthorized interference with computers and computer networks), but the actors remain unknown.
Also Read: How To Delete Security Camera Footage: 5 Different Ways
Polish people noticed obvious grammatical errors in the messages posted on the defaced pages and claimed this was the product of Yandex translation. As such, the actor could be Russian.
Even though Ukraine is going through extreme tensions with Russia, website defacement acts aren’t the typical attack method of a Russian state-sponsored hacking group like GRU.
However, researchers theorize that the attacks could have been conducted by the GhostWriter APT hacking group, which has a history of targeting government entities in Poland and Ukraine.
In November, Mandiant released a report linking the Ghostwriter group to the Belarusian government.
“UNC1151 has targeted a wide variety of governmental and private sector entities, with a focus in Ukraine, Lithuania, Latvia, Poland, and Germany,” explains a report by Mandiant.
The targeting also includes Belarusian dissidents, media entities, and journalists. While there are multiple intelligence services that are interested in these countries, the specific targeting scope is most consistent with Belarusian interests.”
Also, yesterday, the Ukrainian cyberpolice announced the arrest of five ransomware affiliates responsible for over 50 attacks against companies worldwide.
The chances of this wave of defacements being a retaliative act are slim, as the messages don’t mention anything relevant.