KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The National Security Agency (NSA) has shared mitigations and best practices that systems administrators should follow when securing Unified Communications (UC) and Voice and Video over IP (VVoIP) call-processing systems.
UC and VVoIP are call-processing systems used in enterprise environments for various purposes, from video conferencing to instant messaging and project collaboration.
Since these communication systems are tightly integrated with other IT equipment within enterprise networks, they also inadvertently increase the attack surface by introducing new vulnerabilities and the potential for covert access to an organization’s communications.
Improperly secured UC/VVoIP devices are exposed to the same security risks and targeted by threat actors through spyware, viruses, software vulnerabilities, and other malicious means if not adequately secured and configured.
“Malicious actors could penetrate the IP networks to eavesdrop on conversations, impersonate users, commit toll fraud and perpetrate denial of service attacks,” as the US intelligence agency explained.
“Compromises can lead to high-definition room audio and/or video being covertly collected and delivered to a malicious actor using the IP infrastructure as a transport mechanism.”
Also Read: Compliance Course Singapore: Spotlight on the 3 Offerings
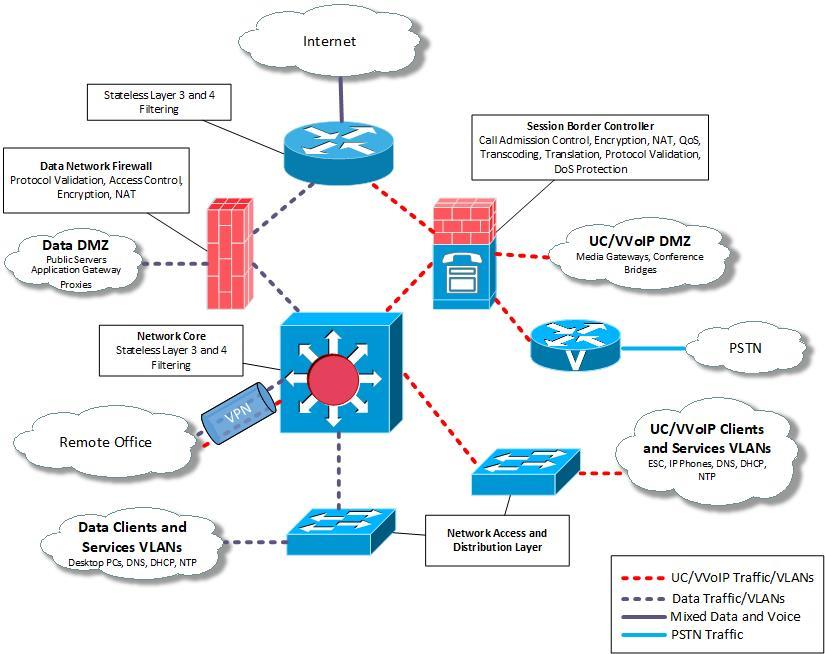
Admins are advised to take these key measures to minimize the risk of their organization’s enterprise network being breached by exploiting UC/VVoIP systems:
“Taking advantage of the benefits of a UC/VVoIP system, such as cost savings in operations or advanced call processing, comes with the potential for additional risk,” the NSA concluded.
“A UC/VVoIP system introduces new potential security vulnerabilities. Understand the types of vulnerabilities and mitigations to better secure your UC/VVoIP deployment.”
Also Read: PDPA Singapore Guidelines: 16 Key Concepts For Your Business
Much more extensive security best practices and mitigations on how to prepare networks, establish network perimeters, use enterprise session controllers, and add endpoints when deploying UC/VVoIP systems are available in the Cybersecurity Information Sheet released today by the NSA.
In January, the NSA also shared guidance on how to detect and replace outdated Transport Layer Security (TLS) protocol versions with up-to-date and secure variants.
The agency also warned companies to use self-hosted DNS-over-HTTPS (DoH) resolvers to block threat actors’ DNS traffic eavesdropping and manipulation attempts.