KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Delaware County, Pennsylvania has paid a $500,000 ransom after their systems were hit by the DoppelPaymer ransomware last weekend.
On Monday, Delaware County disclosed that they had taken portions of their computer network offline after discovering that their network was compromised.
“The County of Delaware recently discovered a disruption to portions of its computer network. We commenced an immediate investigation that included taking certain systems offline and working with computer forensic specialists to determine the nature and scope of the event. We are working diligently to restore the functionality of our systems,” the Delaware County alert stated.
The County stated that the Bureau of Elections and the County’s Emergency Services Department were not affected and are on a different network than the hacked systems.
Local media has stated that the ransomware operators had access to networks containing police reports, payroll, purchasing, and other databases. As part of the attack, the threat actors demanded a $500,000 ransom to receive a decryptor.
“Sources said the county is in the process of paying the $500,000 ransom as it’s insured for such attacks,” Philadelphia’s 6abc’s Action News reported.
Also Read: 10 Practical Benefits of Managed IT Services
Since then, sources have told BleepingComputer that the DoppelPaymer ransomware gang was behind the attack and that Delaware County had paid the ransom.
DoppelPaymer dervices its name from BitPaymer, which shares a large portion of code, but has been improved over time with a threaded encryption process for faster operation.
DoppelPaymer is known to steal unencrypted files when performing their attacks. It is not known if this was done in the attack against Delaware County.
BleepingComputer was also told that the ransomware gang advised Delaware County to change all of their passwords and modify their Windows domain configuration to include safeguards from the Mimikatz program.
Mimikatz is an open-source application commonly used by ransomware gangs to harvest Windows domain credentials on a compromised network.
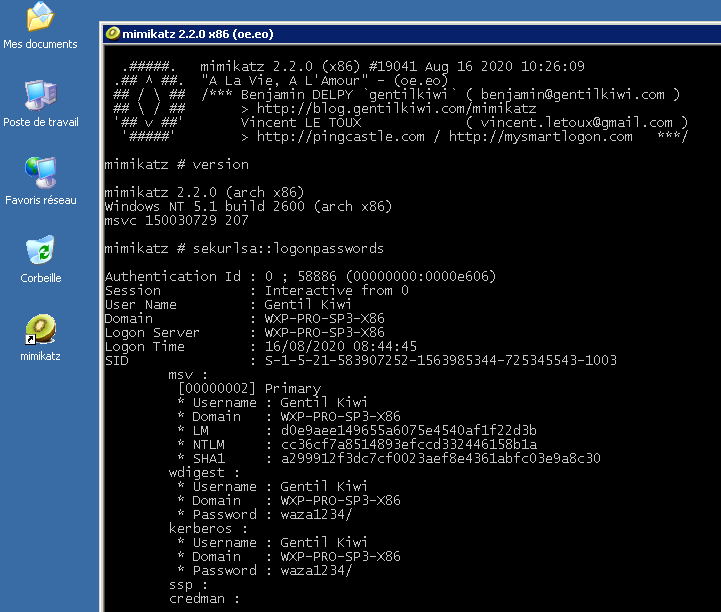
Once the threat actors gain access to a Windows domain administrator password, they deploy their ransomware on the network to encrypt devices.
SANS ISC has a good article on securing a Windows network against Mimikatz attacks that all Windows network admins should become familiar with.
Also Read: Going Beyond DPO Meaning: Ever Heard of Outsourced DPO?
Other victims attacked by DoppelPaymer in the past include Compal, PEMEX (Petróleos Mexicanos), the City of Torrance in California, Newcastle University, Hall County in Georgia, Banijay Group SAS, and Bretagne Télécom.