KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The master decryption keys for the Maze, Egregor, and Sekhmet ransomware operations were released last night on the BleepingComputer forums by the alleged malware developer.
The Maze ransomware began operating in May 2019 and quickly rose to fame as they were responsible for the use of data theft and double-extortion tactics now used by many ransomware operations.
After Maze announced its shutdown in October 2020, they rebranded in September as Egregor, who later disappeared after members were arrested in Ukraine.
The Sekhmet operation was somewhat of an outlier as it launched in March 2020, while Maze was still active.
Also Read: What You Need to Know About Singapore’s Data Sharing Arrangements
Fast forward 14 months later, and the decryption keys for these operations have now been leaked in the BleepingComputer forums by a user named ‘Topleak’ who claims to be the developer for all three operations.
The poster said that this was a planned leak and is not related to recent law enforcement operations that have led to the seizing of servers and the arrests of ransomware affiliates.
“Since it will raise too much clues and most of them will be false, it is necessary to emphasize that it is planned leak, and have no any connections to recent arrests and takedowns,” explained the alleged ransomware developer.
They further stated that none of their team members will ever return to ransomware and that they destroyed all of the source code for their ransomware.
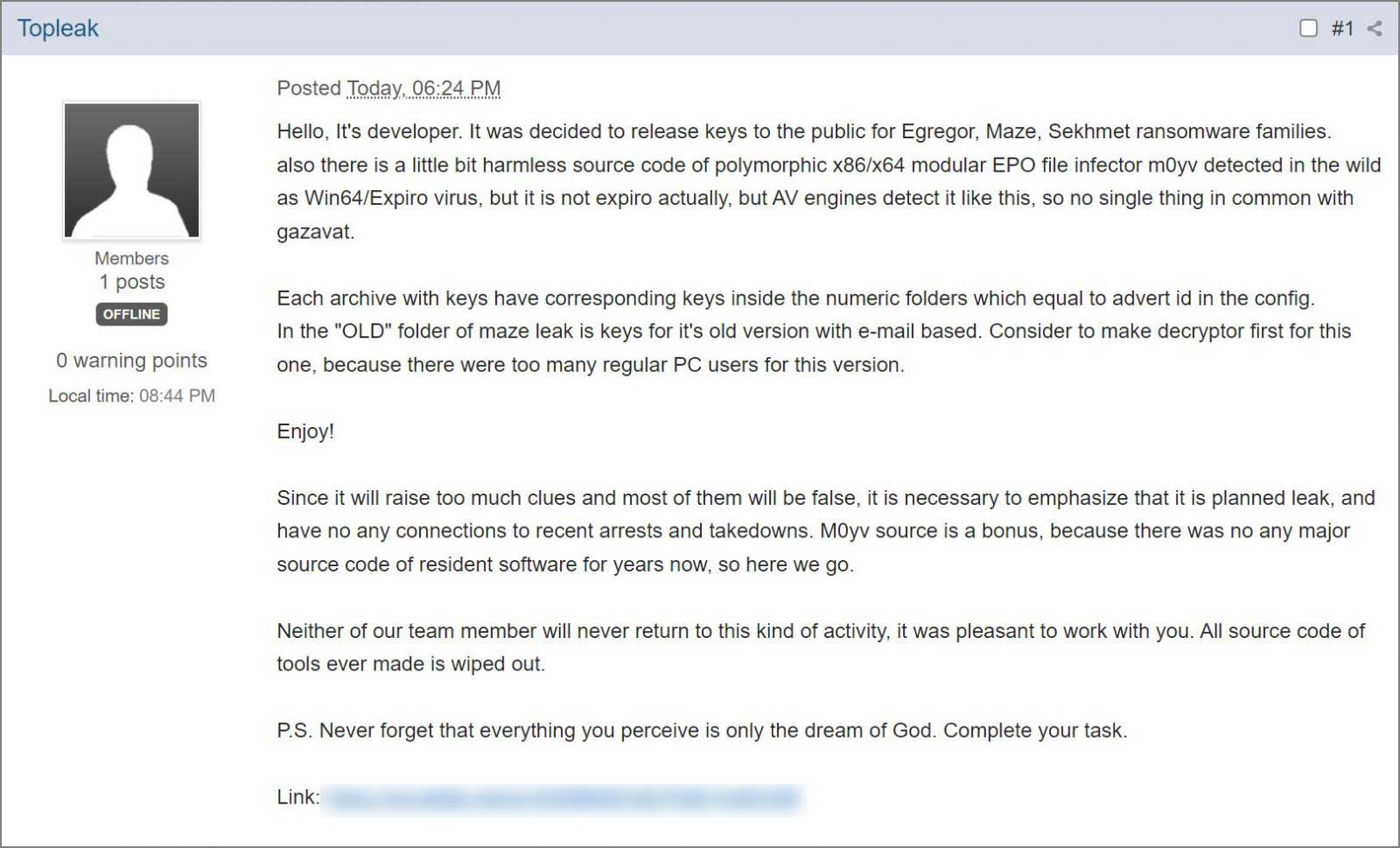
The post includes a download link for a 7zip file with four archives containing the Maze, Egregor, and Sekhmet decryption keys, and the source code for a ‘M0yv’ malware used by the ransomware gang.
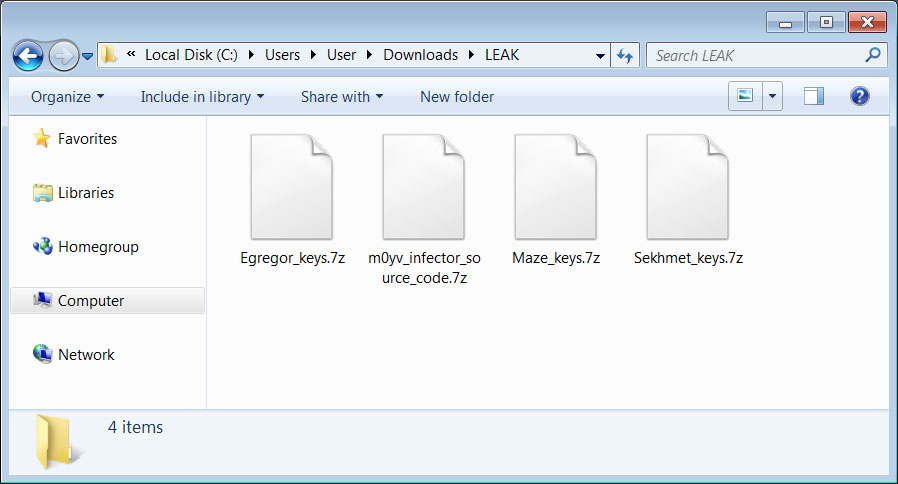
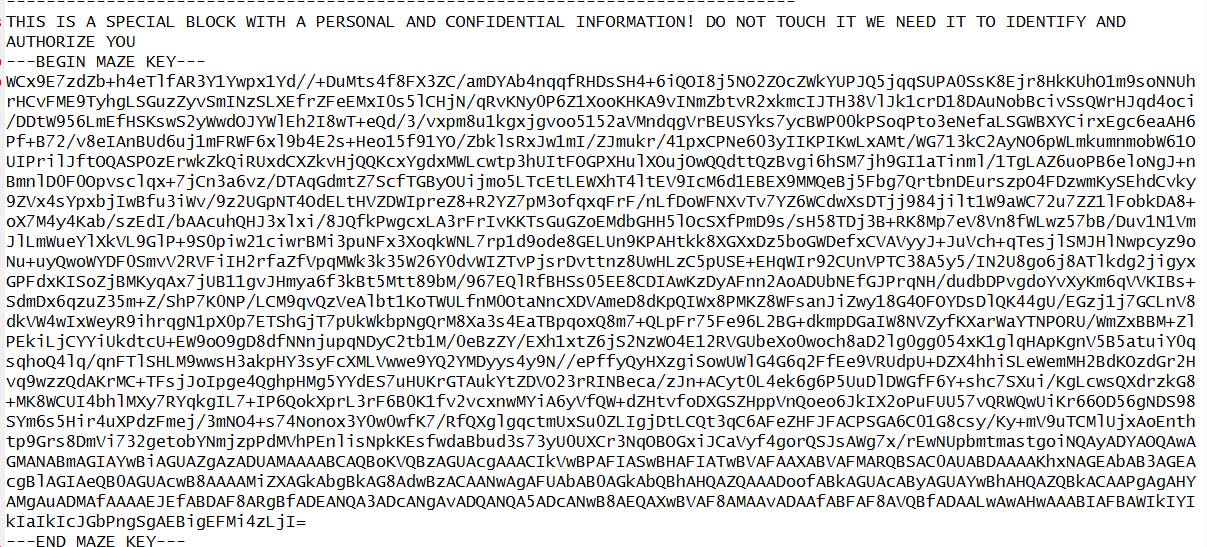
Each of these archives contains the public master encryption key and the private master decryption key associated with a specific “advert”, or affiliate of the ransomware operation.
In total, the following are the number of RSA-2048 master decryption keys released per ransomware operation:
Emsisoft’s Michael Gillespie and Fabian Wosar has reviewed the decryption keys and confirmed to BleepingComputer that they are legitimate and can be used to decrypt files encrypted by the three ransomware families.
Also Read: PDPA Compliance for HR Managers in Singapore: A Must
Gillespie told us that the keys are used to decrypt a victim’s encrypted keys that are embedded in a ransom note.
Emsisoft has released a decryptor to allow any Maze, Egregor, and Sekhmet victims who have been waiting to recover their files for free.
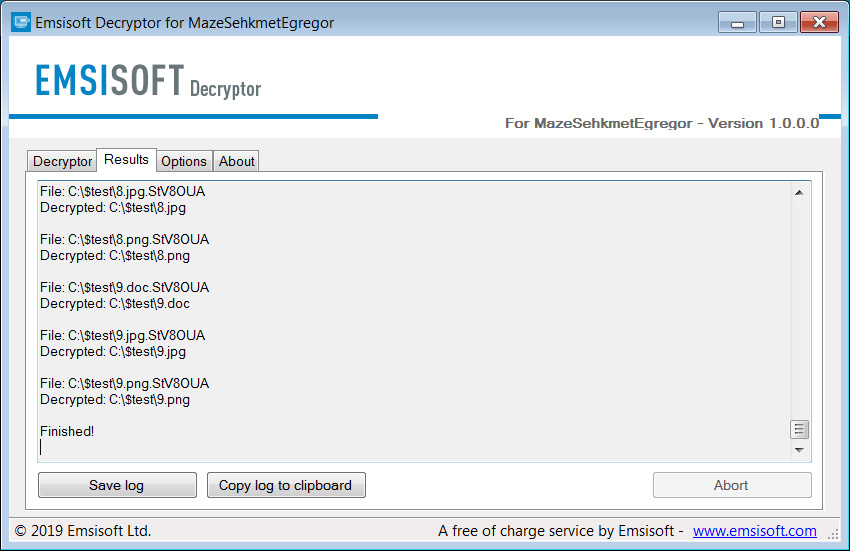
To use the decryptor, victims will need ransom note created during the attack as it contains the encrypted decryption key.
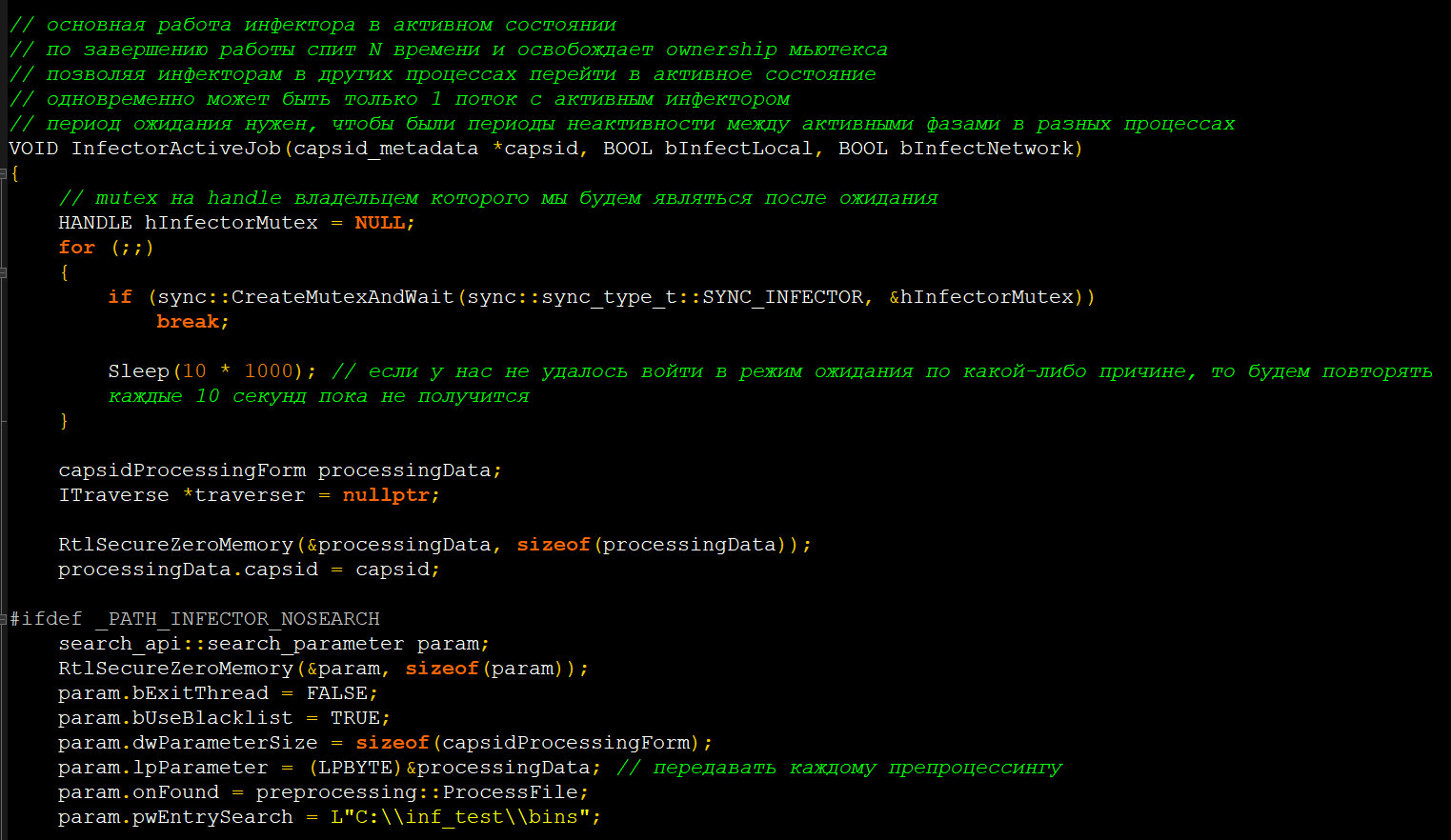
The archive also includes the source code for the M0yv ‘modular x86/x64 file infector’ developed by the Maze ransomware operation and used previously in attacks.
“Also there is a little bit harmless source code of polymorphic x86/x64 modular EPO file infector m0yv detected in the wild as Win64/Expiro virus, but it is not expiro actually, but AV engines detect it like this, so no single thing in common with gazavat,” the ransomware developer said in the forum post.
“M0yv source is a bonus, because there was no any major source code of resident software for years now, so here we go,” the developer later explained.
This source code come in the form of a Microsoft Visual Studio project and includes some already compiled DLLs.
The todo.txt file indicates the source code for this malware was last updated on January 19th, 2022.