KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





In the digital era, data assets have become a commodity which organizations need to tailor fit their services and products with their customer’s preference. As such, companies are smart enough to collaborate with each other in sharing valuable data resources. However, as with any transaction, there are certain challenges on data sharing.
On June 28, 2019, the Info-communications Media Development Authority (IMDA), together with Personal Data Protection Commission (PDPC), unveiled the first comprehensive Trusted Data Sharing Framework. In this article, we will be talking about what this Framework exactly is and how it resolves certain challenges in Singapore’s data sharing arrangements.
The Trusted Data Sharing Framework is a set of non-sequential guidelines that provides the baseline for regulatory considerations, and the contractual, technical, and operational safeguards crucial in any data sharing arrangement.
Through the implementation of a standardized suite of data-sharing practices, the trust between data-sharing companies are further strengthened.
IMDA said in a statement: “The intent of the framework is that, with stronger safeguards and clarity on regulatory compliance, consumers will be more ready to share their data and consequently benefit from more personalised goods and services.”
Also Read: Got A Notice of Data Breach? Don’t Panic!
By providing a common data-sharing syntax to help organizations draft and implement baseline practices, the Framework has solidified the element of trust in Singapore’s data sharing arrangements. The four parts of the Framework is set out as:
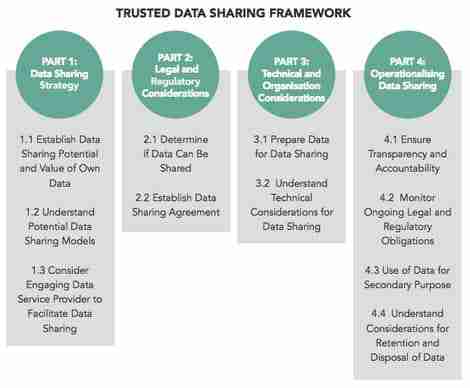
From the Framework‘s set of guidelines, we can see how the IMDA and PDPC intended to set out data-sharing requisites, cases that organizations can assess, technical models, and processes that ultimately ensure transparency during and after data exchange.
It is important to remember that organizations may use the four parts of the framework in any sequence, as suitable to their company’s needs, without omitting any part thereof.
The PDPC has recognized the need of organizations to move faster and keep up with constantly evolving developments in technology and business models. Hence, the committee has created regulatory sandboxes that will allow data to be used and shared accountably beyond the confines of the PDPA.
As an aspect of an organization’s application for exemption from (some) PDPA obligations, Singapore’s data sharing arrangements have to meet all the criteria below:
Finally, IMDA and PDPC has given an overview of the key roles in the data sharing ecosystem thru the Framework:
Singapore’s data sharing arrangements is enlaced with a wide range of guidelines and standards, all designed to address the need to ensure regulatory compliance while solidifying trust between organizations.
This is where hiring an outsourced DPO can help. Aside from the fact that it is mandatory under the PDPA, an outsourced Data Protection Officer (DPO) oversees data protection responsibilities and ensures that organizations comply with the Personal Data Protection Act (PDPA).
With the constant need to keep in line with new and emerging developments in technology and business models, bringing innovation to customers should never be a burden.
With a more robust data sharing framework, organizations can foster trusted partnership with transparency, fairness, security, and of course, data integrity.
Also Read: PDPA Compliance for HR Managers in Singapore: A Must