KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Swiss national Till Kottmann, 21, has been charged for conspiracy, wire fraud and aggravated identity theft, the U.S. Department of Justice announced.
Kottmann has been at the forefront of numerous leaks involving source code, some of it proprietary or confidential, from dozens of large companies.
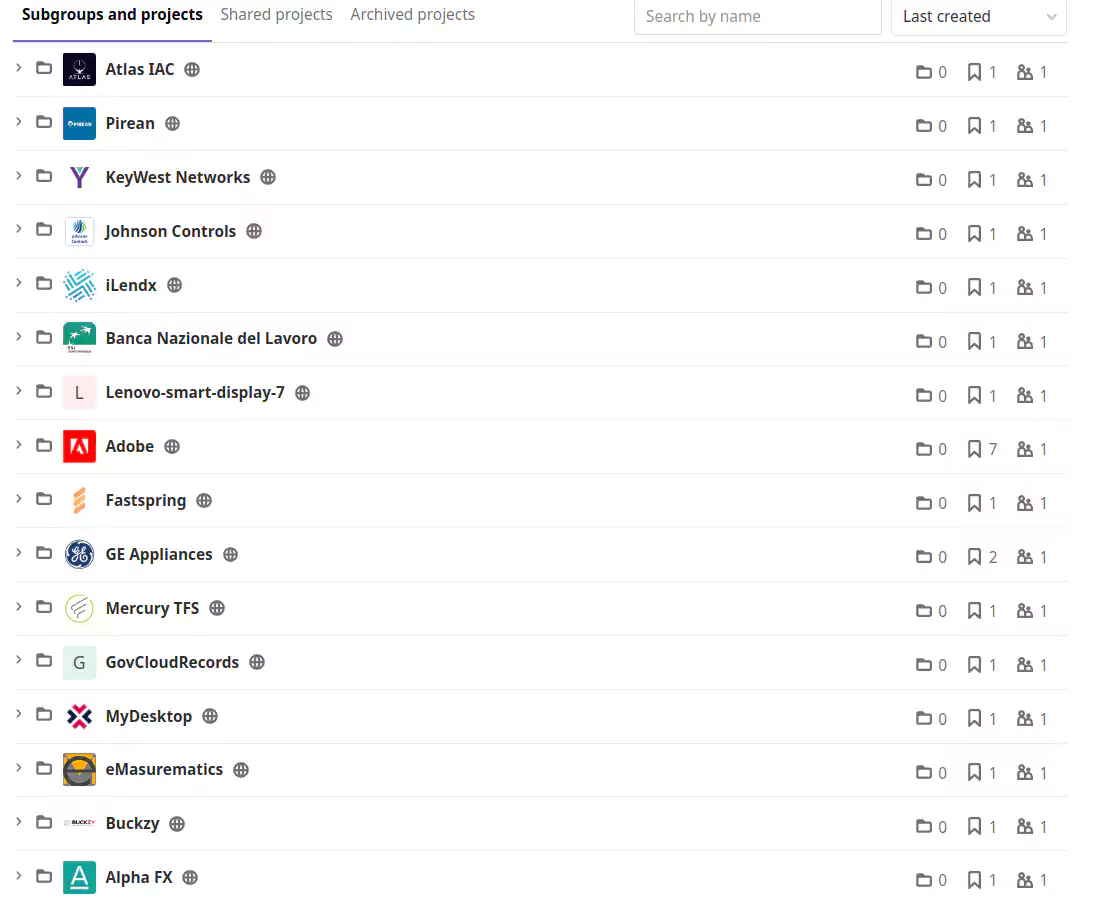
In a public repository, Kottmann published code from Intel, Nissan, Lenovo, Nintendo, Motorola, AMD, Qualcomm [1]. The indictment says that the leaks included internal files and records from more than 100 entities.
Also Read: In Case You Didn’t Know, ISO 27001 Requires Penetration Testing
Most recently, Kottmann and the group of hackers they were part of (the ironically named “APT-69420 Arson Cats“) gained access to surveillance systems at Tesla, Equinox, healthcare clinics, jails, and banks.
The feat was possible by obtaining a super admin account for Verkada surveillance company that provided services to affected organizations. Images and video recordings from surveillance cameras were later shared with a larger audience, including journalists.
The initial charges are for previous hacking activities as the they date from September 2020. Last Friday, Swiss authorities raided Kottmann’s home and seized electronic devices.
That’s also the day of the last post on the group’s Telegram channel sharing the news of the raid. The domain used for leaking the data, git.rip, is no longer online as the FBI seized it recently.

In past conversations with BleepingComputer, Kottmann (who asked us to use “they/them”pronouns when referring to them), said that some of the data they leaked came from other individuals that did the hacking or that access was possible due to misconfiguration.
The DoJ confirmed this on Thursday, noting that the computer intrusion and data theft activities started in 2019 and continued to the present. However, Kottmann is responsible for at least some of the hacking:
The indictment alleges various examples of hacks KOTTMANN committed. For instance, in February 2020, KOTTMANN illegally accessed computers belonging to a security device manufacturer located in the Western District of Washington and stole proprietary data. Likewise, in April 2020, KOTTMANN victimized the manufacturer of tactical equipment. In the latter instance, KOTTMANN improperly used the credentials of an employee to access illegally the manufacturer’s source code databases. In August, KOTTMANN hacked a Washington state agency and a U.S. government contractor and stole source code related to various web applications. And, more recently, in January 2021, KOTTMANN similarly conducted cyberattacks on an automobile manufacturer and a financial investment company. KOTTMANN published data stolen through these hacks, among many others, on KOTTMANN’s website and used social media to promote the hacking activity and the theft and release of proprietary information.
Also Read: 4 Considerations In The PDPA Singapore Checklist: The Specifics
Till Kottmann also used the online names “Tillie,“ ”deletescape,“ and “tillie crimew.” They are currently in Lucerne, Switzerland, and are aware of the pending charges: