KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







FortiGuard Labs security researchers have linked a new ransomware strain dubbed Diavol to Wizard Spider, the cybercrime group behind the Trickbot botnet.
Diavol and Conti ransomware payloads were deployed on different systems in a ransomware attack blocked by the company’s EDR solution in early June 2021.
The two ransomware families’ samples are cut from the same cloth, from the use of asynchronous I/O operations for file encryption queuing to using virtually identical command-line parameters for the same functionality (i.e., logging, drives and network shares encryption, network scanning).
However, despite all similarities, the researchers couldn’t find a direct link between Diavol ransomware and the Trickbot gang, with some significant differences making high confidence attribution impossible.
For instance, there are no built-in checks in Diavol ransomware preventing the payloads from running on Russian targets’ systems as Conti does.
There’s also no evidence of data exfiltration capabilities before encryption, a common tactic used by ransomware gangs for double extortion.
Also Read: The Difference Between GDPR and PDPA Under 10 Key Issues
Diavol ransomware’s encryption procedure uses user-mode Asynchronous Procedure Calls (APCs) with an asymmetric encryption algorithm.
This sets it apart from other ransomware families as they commonly use symmetric algorithms to significantly speed up the encryption process.
Diavol also lacks any obfuscation as it doesn’t use packing or anti-disassembly tricks, but it still manages to make analysis harder by storing its main routines within bitmap images.
When executing on a compromised machine, the ransomware extracts the code from the images’ PE resource section and loads it within a buffer with execution permissions.
The code it extracts amounts to 14 different routines that will execute in the following order:
Right before Diavol ransomware is done, it will change each encrypted Windows device’s background to a black wallpaper with the following message: “All your files are encrypted! For more information see README-FOR-DECRYPT.txt”
“Currently, the source of the intrusion is unknown,” Fortinet says. “The parameters used by the attackers, along with the errors in the hardcoded configuration, hint to the fact that Diavol is a new tool in the arsenal of its operators which they are not yet fully accustomed to.”
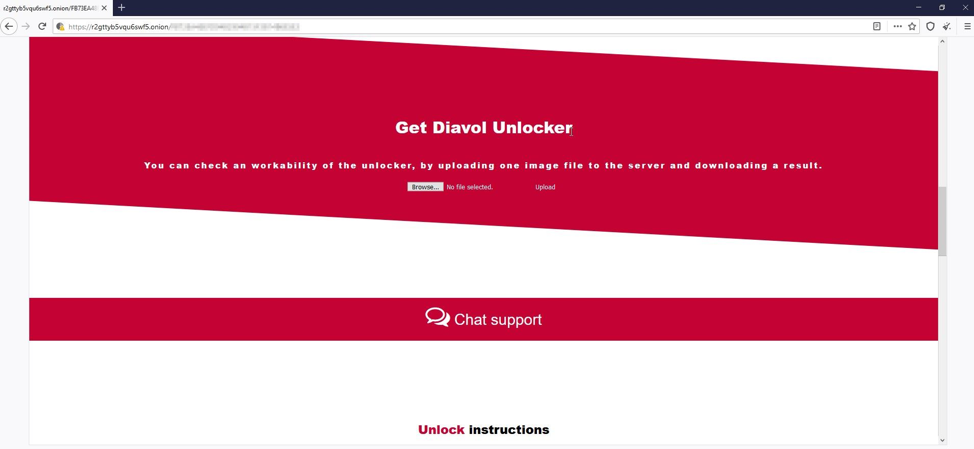
Additional Diavol ransomware technical info and indicators of compromise (IOCs) can be found at the end of FortiGuard Labs’s threat research report.

Wizard Spider, a Russian-based financially motivated cybercrime group that operates the Trickbot botnet used to drop second-stage malware on compromised systems and networks.
Also Read: PDPA Compliance Singapore: 10 Areas to Work On
Trickbot is particularly dangerous to enterprises since it propagates through corporate networks. If it gets admin access to a domain controller, it will also steal the Active Directory database to collect even more network credentials the group can use to make their job easier.
While Microsoft and several partners announced the takedown of some Trickbot C2s after the US Cyber Command also reportedly tried to cripple the botnet, TrickBot is still active, with the group still releasing new malware builds.
The TrickBot gang’s operations entered a higher gear during the summer of 2018 when they started targeting corporate networks using Ryuk ransomware and again in 2020 after switching to Conti ransomware.
The developers of Trickbot have also started deploying the stealthy BazarLoader backdoor in attacks in April 2020, a tool designed to help them compromise and gain full access to corporate networks before deploying the ransomware payloads.