KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







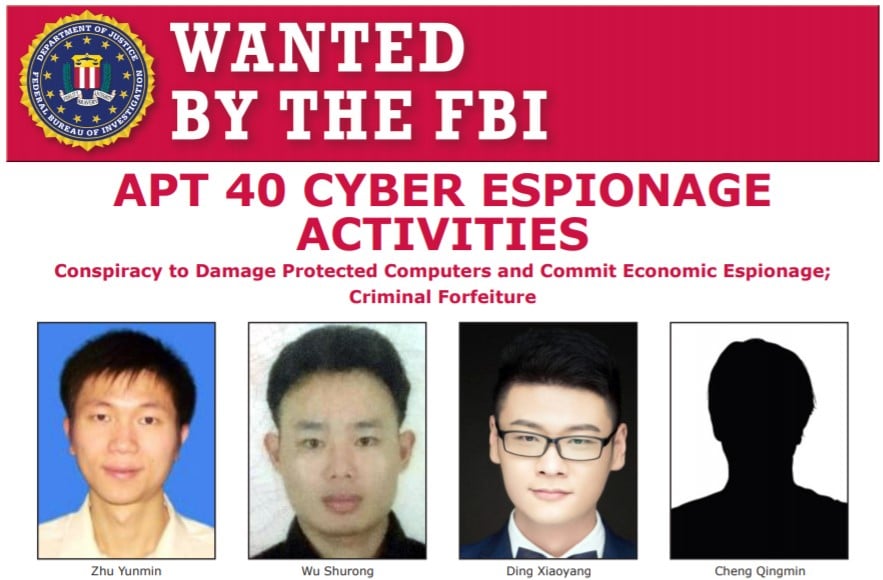
Today, the US Department of Justice (DOJ) indicted four members of the Chinese state-sponsored hacking group known as APT40 for hacking various companies, universities, and government entities in the US and worldwide between 2011 and 2018.
Ding Xiaoyang (丁晓阳), Cheng Qingmin (程庆民) and Zhu Yunmin (朱允敏) were intelligence officers in the Hainan State Security Department (HSSD), a provincial arm of China’s Ministry of State Security (MSS).
They founded a front company, Hainan Xiandun Technology Development Co., Ltd. (海南仙盾) (Hainan Xiandun), that acted as a cover for their hacking operations as revealed in the indictment.
Also Read: Don’t Be Baited! 5 Signs of Phishing in Email
Wu Shurong (吴淑荣), the fourth Chinese national indicted today by the DOJ, was hired through Hainan Xiandun to create malware, hack into foreign governments’ computer systems, companies, and universities to steal trade secrets, intellectual property, and other high-value information, as well as to supervise other Hainan Xiandun hackers.
Industry sectors targeted by APT40 state hackers include, among others, aviation, defense, education, government, health care, biopharmaceutical, and maritime.
Examples of APT40 activity include targeting maritime industries and naval defense contractors in the US and Europe, regional opponents of the Belt and Road Initiative, multiple Cambodian electoral entities in the run-up to the 2018 election per UK’s National Cyber Security Centre (NCSC).
The APT40 operators used multiple tactics to breach their targets’ networks, including spearphishing emails, hijacked credentials, as well as malware (BADFLICK aka GreenCrash, PHOTO aka Derusbi; MURKYTOP, and HOMEFRY) which helped gain initial access to victim systems, move laterally within networks, and steal credentials.
“Stolen trade secrets and confidential business information included, among other things, sensitive technologies used for submersibles and autonomous vehicles, specialty chemical formulas, commercial aircraft servicing, proprietary genetic-sequencing technology and data, and foreign information to support China’s efforts to secure contracts for state-owned enterprises within the targeted country (e.g., large-scale high-speed railway development projects),” the DOJ said.
“At research institutes and universities, the conspiracy targeted infectious-disease research related to Ebola, MERS, HIV/AIDS, Marburg and tularemia.”
The four suspects are charged with one count of conspiracy to commit computer fraud and one count of conspiracy to commit economic espionage, carrying maximum sentences of five and 15 years in prison, respectively.
CISA and the FBI published today indicators of compromise and TTPs to help organizations detect and remediate APT40 intrusions and established footholds within their networks.
The NSA, CISA, and FBI also issued a joint advisory with over 50 tactics, techniques, and procedures (TTPs) that APT40 and other Chinese-backed threat groups have used in attacks targeting the US and allied networks.
Last but not least, the indictment of the four APT40 members comes after the US and allies, including the European Union, the United Kingdom, and NATO, have today officially accused China (the APT group tracked by Microsoft as Hafnium, in particular) of coordinating this year’s widespread Microsoft Exchange hacking campaign.
Also Read: 5 Most Frequently Asked Questions About Ransomware