KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







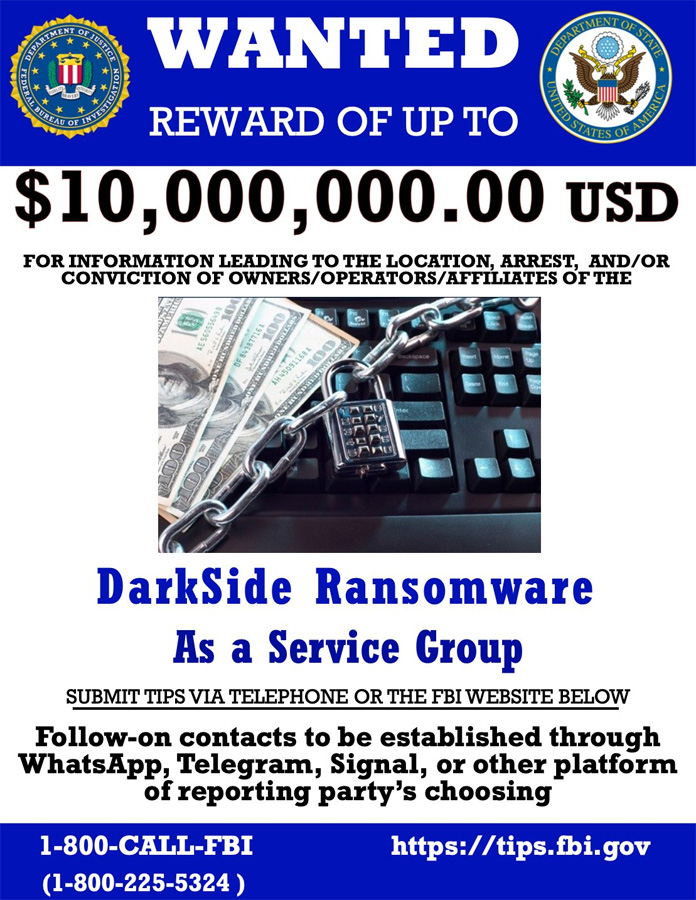
The US government is targeting the DarkSide ransomware and its rebrands with up to a $10,000,000 reward for information leading to the identification or arrest of members of the operation.
The US Department of Statement announced today that they are now offering a $10,000,000 reward for the identification or location of DarkSide ransomware members operating in key leadership positions.
A reward of $5,000,000 is also being offered for information leading to the arrest of any individual who attempts to participate in a Darkside attack.
Also Read: How Formidable is Singapore Cybersecurity Masterplan 2020?
“In addition, the Department is also offering a reward offer of up to $5,000,000 for information leading to the arrest and/or conviction in any country of any individual conspiring to participate in or attempting to participate in a DarkSide variant ransomware incident,” announced the Department of State.
Tips can be submitted to the FBI at https://tips.fbi.gov or via WhatsApps, Telegram, and Signal.
As the announcement states “DarkSide variant ransomware,” this reward will also apply to DarkSide rebrands, including the ransomware gang’s most recent BlackMatter operation.
When ransomware operations begin to feel the heat of law enforcement after attacking a highly sensitive organization, it is common for them to rebrand under a different name.
DarkSide rebranded as BlackMater after attacking the Colonial Pipeline and feeling the full scrutiny of international law enforcement.
Also Read: Heard of Outsourced DPO?
Similarly, other ransomware operations have also rebranded in the past, including:
Yesterday, BleepingComputer reported that BlackMatter also shut down their operation after feeling “pressure from the authorities” and gang members going missing.
Today’s Department of State bounty on DarkSide clearly shows that switching to a different ransomware name will not stop law enforcement from pursuing them.
This reward is offered as part of the Department of State’s Transnational Organized Crime Rewards Program (TOCRP).
“The program gives the Secretary of State statutory authority to offer rewards of up to $25 million for information leading to several desired law enforcement objectives, including the arrest and/or conviction in any country of any individuals participating in, or conspiring to participate in transnational organized crime; the disruption of financial mechanisms of a transnational organized crime group; and the identification or location of an individual who holds a key leadership position in a transnational organized crime group,” reads the program’s description.
The US government is also offering a $10 million reward for information on state-sponsored hackers targeting US critical infrastructure.
With these large rewards, the US government hopes hackers will turn on each other and get a legal, stress-free payout.