KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Eggfree Cake Box has disclosed a data breach after threat actors hacked their website to stole credit card numbers.
Cake Box is a UK chain of stores selling fresh cream celebration cakes made without eggs. There are currently 164 Cake Box stores located throughout the United Kingdom.
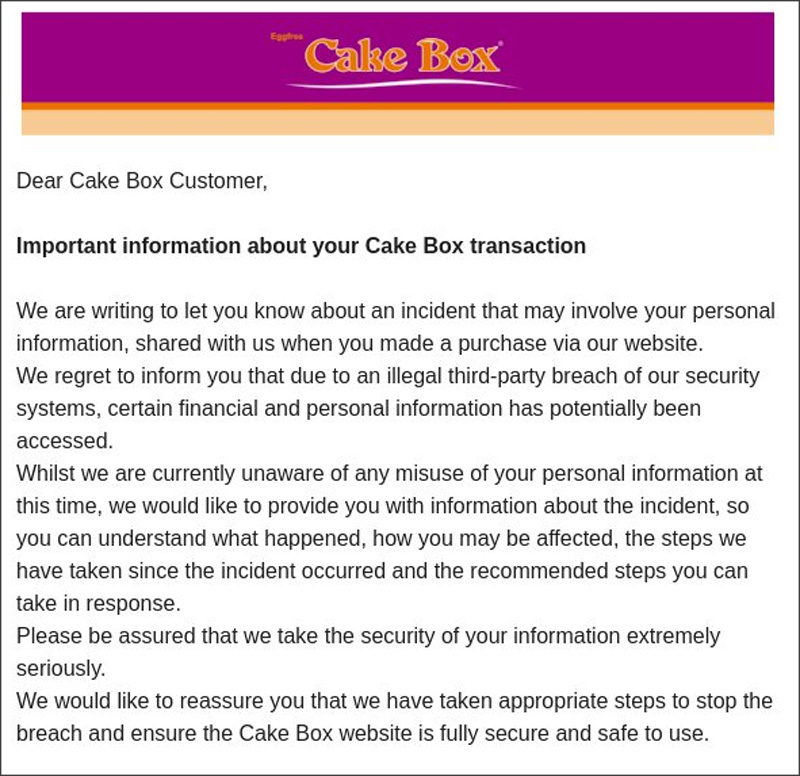
In emails sent to customers this week, Cake Box disclosed that their website was hacked in 2020 to include malicious scripts that stole customer information, including credit cards, submitted to the site.
Cake Box learned of the breach on April 27th, 2020, when they were contacted by their then-payment processing provider, Global Payments, who warned them that the site was breached.
“We immediately launched a thorough investigation of our systems in response and, with the help of experienced third-party security specialists, determined that an unauthorised third party had indeed recently gained access to the Cake Box website and placed certain malware on it”, disclosed Cake Box in a data breach notification sent to customers.
“Using this malware, the third party was able to copy certain information provided by our customers when making purchases from our website. We were then subsequently made aware that, in certain instances, this information has been used to make fraudulent purchases.”
When customers made purchases on the site while it was infected, these malicious scripts sent the first name and surname, email address, postal address, and payment card information, including the three-digit CVV code, to a remote server controlled by the attackers.
Also Read: The Difference Between GDPR And PDPA Under 10 Key Issues
Based on the description, this breach appears to be a MageCart attack.
MageCart attacks are when threat actors hack an eCommerce site and add malicious scripts to their payment confirmation pages.
These scripts will monitor checkout pages, and if credit card information is submitted on the page, transmit the data to a remote site under the attacker’s control.
The attackers can then log in to their servers and retrieve the stolen credit card information to sell on the dark web or perform fraudulent transactions.
Also Read: PDPA Compliance Singapore: 10 Areas To Work On
If you are a Cake Box customer and have received notifications about the data breach, you should analyze your current and past transactions and make sure no fraudulent charges are present.